.Bot
.Bot is a harmful program of the Ransomware variety – a type of virus that locks-up user data. The .Bot encryption is what keeps the files inaccessible, and a ransom is demanded from the user for the decryption key.
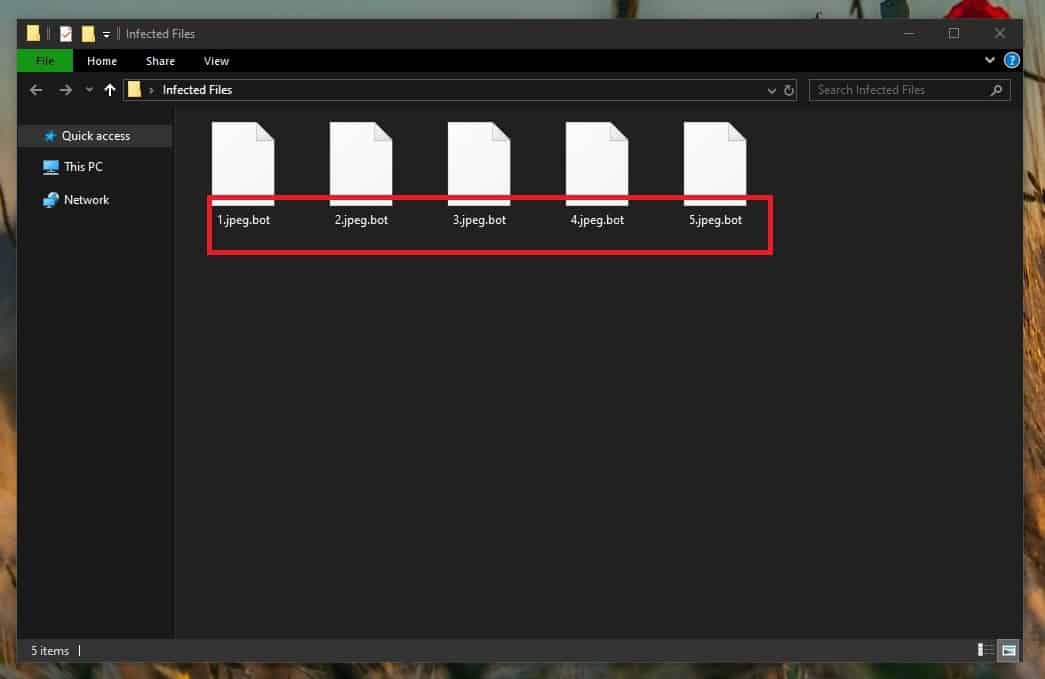
The .Bot Virus will change the extension of your files
The purpose of the lockdown under which your files would get put if a virus such as this one enters your system is simple – it’s all done to make you pay a significant amount of money to the criminals behind this infection. Since many people keep sensitive files in their computers related to their job, education, or simply files that have high sentimental value to them, having the access to those files taken away from them may be quite unpleasant and cause some serious issues. This is why many may be willing to pay the ransom just so that they could bring back their data. However, not everyone can afford to pay the money that the hackers require. Oftentimes the ransom sum is a four-digit number, and no matter how important your files are, you may simply lack the opportunity to make such a payment. Furthermore, even if you have the money and are willing to issue the payment, this in no way guarantees the recovery of your data. The hackers behind such a virus might be lying about helping you recover your data once you pay them. In such a case, all that would happen if you complete their demands is you would lose a sizable amount of money in total vain.
The .Bot virus
The .Bot virus is a computer threat of the Ransomware type. The .Bot virus will restrict the user’s access to their data by applying military-grade encryption. The user will be asked to pay money for the data’s release.
The typical practice among the Ransomware hackers is for them to demand the payment in a cryptocurrency form. This is an important detail, because the use of cryptocurrency such as BitCoin, and Ukash makes stripping the hackers off their anonymity an almost unachievable task. There are very few cyber criminals using Ransomware who have ever been caught and brought to justice. This is also one of the main reasons why this type of computer infections (.Derp, .Coot) are everywhere nowadays, and why they are such a huge issue.
Another very serious problem with Ransomware is that they dealing with them is a very arduous, and not always achievable task. In the case of Ransomware, removing the threat is not enough. Though it is still crucial to eliminate the infection, to unlock the files, you will need to take additional steps. The problem with that is there isn’t a surefire method that can universally bring encrypted files back to their functional states. As we said, the payment, though it may seem like a workable option, is not something you should actually rely on. At best, it should be a last resort option, and not a go-to one.
The .Bot file encryption
The .Bot file encryption is a process that makes digital data inaccessible. The .Bot file encryption rearranges the contents of the targeted file, making it unreadable to any software.
The encryption placed on your files will keep them inaccessible, and as long as it’s on them, no program on your computer would be able to read the sealed data. The encryption stays in the files even when the virus isn’t present in the computer. To recover some of your data without the decryption key that the hackers want you to pay for, you can try the suggested alternatives from our guide. However, remember that they might not work for all of you, and also make sure to first remove the virus before you try to recover any data. The removal instructions are in the first part of the guide.
SUMMARY:
Remove .Bot Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.
I hope I’m doing the right thing here and I hope this does not lock up my whole computer
Hi Melissa Taylor,
you can follow this link to successfully remove the ransomware from your system.