Calendar.wpu.sh
If you have recently discovered that your iPhone or iPad has been infected by Calendar.wpu.sh, you’ve fallen victim to what’s known as a browser hijacker. Calendar.wpu.sh is generally harmless and won’t result in any damage on your device. But software like Calendar.wpu.sh can potentially lead to complications for you in the long term.
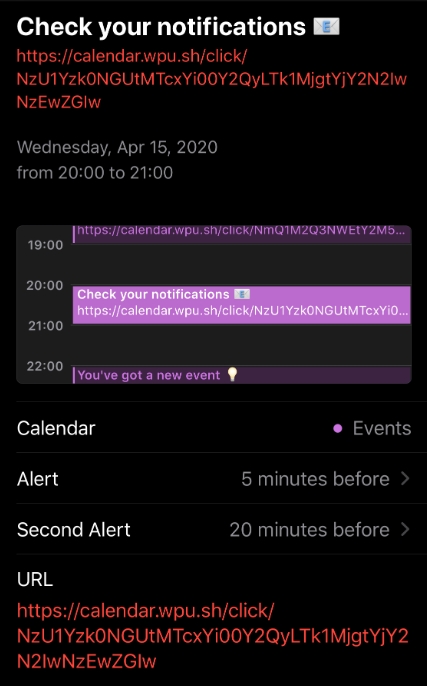
The Calendar.wpu.sh Virus will spam your calendar with fake events.
Browser hijackers are designed as online advertising tools. And when they end up in your device, they target the main browser, be it Safari, Chrome or some other one. And then, they begin to alter its settings so as to enable their advertising processes. For example, Calendar.wpu.sh may change the homepage of your browser and may also set a new default search engine. This, in turn, may lead to you seeing a lot more sponsored search results for your queries, many of which may not even be relevant.
In addition, due to Calendar.wpu.sh’s presence, your browser may begin to trigger page redirects during your sessions, which is also quite annoying. And on top of that, browser hijackers are particularly known for generating ads directly from your device when you browse the web: popups, banners, box messages – you name it.
All of this is done for the purpose of earning revenue for the developers of the browser hijacker in question. And usually this revolves around Pay Per Click or similar remuneration schemes. One of the bigger problems with this, however, is that amidst all this various content you could potentially be exposed to viruses such as Trojans, ransomware and others.
For this reason, we usually don’t recommend interacting with any of the displayed ads. And it’s simply best to remove Calendar.wpu.sh, which can be done by following the steps in the following removal guide.
Calendar.wpu.sh iPhone Virus Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.
Thank you so very much!! Your directions were very easy to follow. I was able to remove this calendar.wpu.sh from my iphone and watch. THANK YOU!