This page aims to help you remove Cerber3. These Cerber3 Ransomware removal instructions work for all versions of Windows, including Windows 10.
Cerber3 File Virus is one of the many existing variants of ransomware, which puts it at the top of the list of cyber threats out there. Ransomware has become the most feared type of malware in just the few recent years and has experienced a neat-exponential growth in its number of unique samples. It targets businesses and private users alike, although the former are becoming a more and more desirable target due to the obvious fact of corporations and organizations having deeper pockets. Nonetheless, the risk of getting infected is still very great and it’s important to be informed about such threats, so as to be able to better protect yourself from them. Let us first go over what ransomware is, how it works and most importantly: how it affects users.
The basics
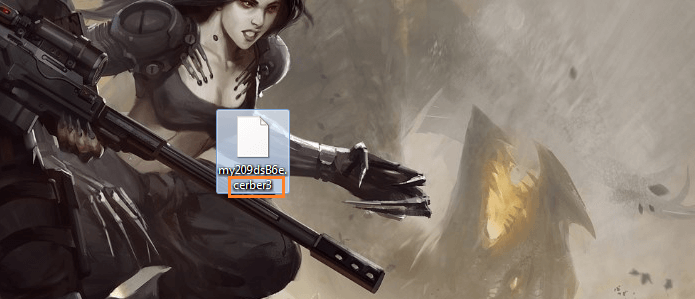
Programs like .Cerber3 are designed to infiltrate the victim’s machine and apply a strong encryption on certain files that are stored on that particular PC. In this case turning them into .cerber3 file extensions. Ransomware tends to mainly affect documents, pictures, music and videos, but it’s not limited to those. Once the encryption process is complete, with all the file extensions changed to those of the virus, a ransom note is displayed on the computer screen. It will usually inform the user that his or her files have been locked and will also let them know that they can unlock them in exchange for a given amount of money. Typically, this money (ransom) is requested to be paid in bitcoins – the well-known cryptocurrency. The reason for this is mainly because bitcoins are pretty difficult to trace, which allows the hackers to stay hidden.
Now comes the most vital question in all of this and that’s how ransomware gets into people’s computers. There are many tactics hackers use to distribute their harmful scripts, but we will outline only the most used ones:
- This is the number one possible way for you to contract .Cerber3 or some other virus of this stem. Malvertisements are harmful ads, which have been injected with malware. Once you click on them, they either redirect you to a malicious website, or directly download a virus onto your system, in this case ransomware. Malvertisements can seem as real as any ad and might actually be a real ad, only it was contaminated by hackers. You’re more likely to find one of these on shady, obscure-looking websites with questionable content, but there’s really no limit as to their distribution across the web.
- Program bundles. This is another common method and it represents the combination of one type of software with another or several other within one downloadable package. You might be thinking you’re downloading some useful freeware or other program, but as a result you’re actually bringing in more than just that. Torrent sites are a likely source for contaminated files, so be very careful around those and it is best you avoid downloading anything from sites you cannot fully trust.
- Spam emails. When sent through a spam email, it’s usually the ‘middle man’ that arrives – a Trojan horse. Trojans are well known to be used as backdoors for ransomware, so once you expose your system to one of those – it proceeds to automatically download the ransomware on it, too. The Trojan is usually embedded within an attached file, which could be as innocent as a Word or PDF document, but don’t let that fool you. No matter how elaborate a disguise the cybercriminals might come up with, you are responsible to be very cautious with any incoming emails.
What about paying the ransom?
You might be trying to figure out what the best course of action is for you and since you’re on this page, you’re probably trying to find a way past paying the ransom. And that’s a good thing. We encourage users to try other solutions first, even though it is of course up to each individual to make those decisions. We have prepared a removal guide for you below with the exact steps that will lead you to removing this malware from your system. In addition, there are also a few steps dedicated to retrieving the encrypted files. While we cannot promise that the restoration of your data will be fully successful, we can assure you that it’s worth giving a try and won’t cost you anything even in the event of a failure. We should probably also mention that succumbing to the hackers’ blackmailing won’t guarantee you access to your files either, as they might not even send you the promised decryption key. Consider the information you’ve read so far and make an informed decision based on that. Good luck!
SUMMARY:
.Cerber3 Ransomware Virus File Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.
Hello Pratik, unfortunately there is currently no way to decrypt files targeted by cerber3. Check out our list of active decryptors here -> https://howtoremove.guide/how-to-decrypt-ransomware/ A lot of people have problems with cerber3, so as soon as a solution is found we’ll share it with everyone.
Hello I’ve got infected with cerberware but it has a different extension (.b6e3) instead of .Cerber . It has the same message with all the warnings. Can you please help me?
Did you try using our guide? Also, we advise you to visit our How to Decrypt Ransomware article where you can find additional information regarding the decryption and restoration of the locked data.
Hi….i have lost all my images from childhood until university and mariage ..and pregnance and whole my life by cerber3.can any one help me please ?
Our advice for you is to give a try to the instructions in the guide from this page and also to visit our How to Decrtypt Ransomware article where you can find additional help against Ransomware infections like Cerber.
hello in 2020 any updates on cerber3 decrypter