CryLock
CryLock is a Ransomware-based malware that uses a technique called cryptoviral extortion. CryLock extorts money from its victims by encrypting their files and demanding a ransom for their decryption.
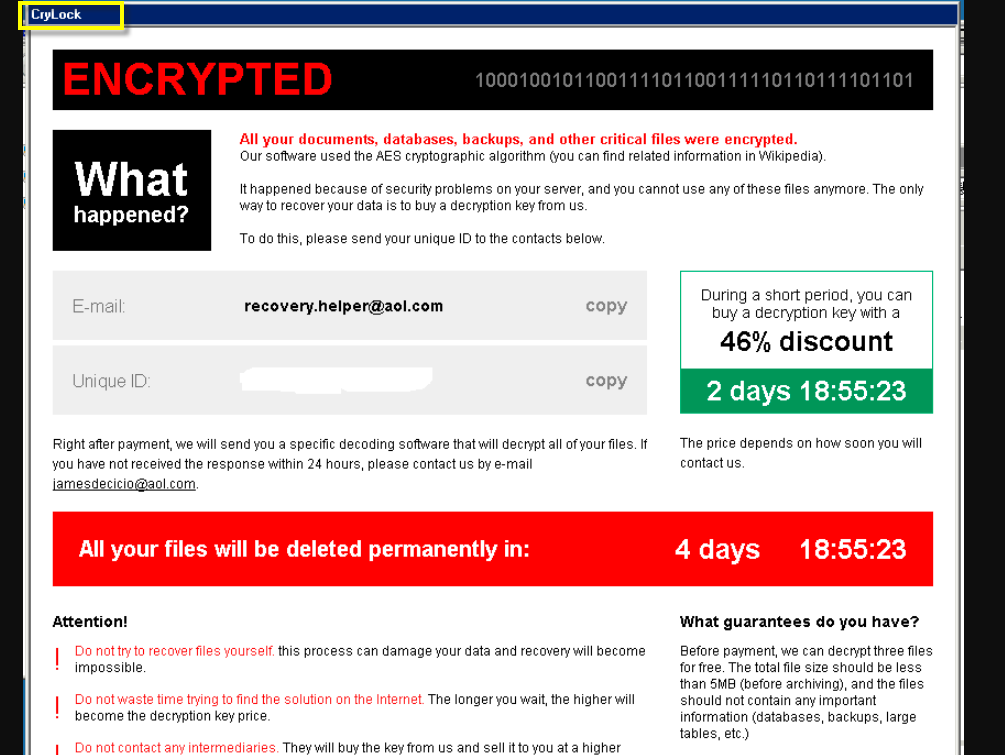
The CryLock virus ransom note
The following article contains information about one of the latest variants of Ransomware known as CryLock . This infection can encrypt a variety of files (documents, archives, audio files, videos, images, etc.) with a complex algorithm and demand a ransom for their decryption. In this post, we’re going to explain exactly how this cryptovirus works, and above all, how to remove it. You will find a removal guide at the bottom of the article specially created to walk you through the steps that will help you clean up your system from the dangerous malware. We have also included instructions with the help of which you could attempt to recover the encrypted files. First, however, it is really important that you effectively remove CryLock , as leaving it on your computer may result in further encryption of recovered files or of any new data.
The CryLock virus
The CryLock virus is an infection that requires a ransom payment in BitCoins. BitCoin payments are impossible to trace, making the criminals behind the CryLock virus difficult to prosecute.
There are several common ways that cyber criminals use in order to spread Ransomware infections like CryLock , the most powerful of which has proved to be the malvertising. Malvertising is the practice of injecting an existing online ad with a virus or creating a new advertisement, embedded with the harmful program right from the beginning. If you click on one of these ads, whether it’s a pop-up, a banner message, or a link, you may end up downloading Ransomware to your machine automatically. The process is a notoriously stealthy, and typically no indication of the contamination can be seen.
Another very likely way you might get compromised by a threat like CryLock and Igvm may be through a spam email with a hidden Trojan Horse inside. Hackers often use Trojan Horse viruses to “transport” the Ransomware into the victim’s computer since they can be downloaded in one click and can automatically download the Ransomware right away. This also occurs without any warning or a hint, so you’re likely not going to be aware of what’s going on.
The CryLock file decryption
The CryLock file decryption is a process that may not always be successful. Ideally, the best way to get back the CryLock files is to use your personal backups.
The moment CryLock gets inside, its first job is to scan the entire computer for specific file types and apply a complex file-encryption algorithm to all of them. This allows the malware to later place its ransom-demanding notification and blackmail you for the specially generated access key. The ransom amount requested for that key may vary from a couple of hundreds to a couple of thousands and will typically be required to be paid within a day’s time.
Earlier we stated that our guide may help you remove CryLock and provide you with instructions to potentially restore the encrypted files without paying a ransom. Unfortunately, we can’t promise that our solution would be 100% successful. This may make you wonder whether it would be a better idea to simply pay the requested ransom amount to the hackers if that will recover all your files.
Of course, we can’t tell you what to do but we should point out that there have been lots of cases of Ransomware victims that have been left with no decryption key after the requested ransom amount has been promptly transferred. The hackers have either disappeared with the money or they have sent a key that failed to get the job done. The conclusion is, you should carefully consider the risks and act in your best interest.
SUMMARY:
| Name | CryLock |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove CryLock Ransomware
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.
Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:
If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:
Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
How to Decrypt CryLock files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!
Leave a Comment X