The FoggyWeb Malware
Custom malware used by the Nobelium hacking organization has been spotted to spread additional payloads and steal data from Active Directory Federation Services (AD FS) servers. This discovery was announced in the Microsoft security blog in a post from Monday.
The tech giant reminds that Nobelium is a Russian Foreign Intelligence Service (SVR) hacking group (also known as APT29) that was behind the SolarWinds supply-chain attack from last year, which compromised numerous US government agencies.
The Nobelium Hackers
Named FoggyWeb, the new malware of the notorious Nobelium group is a “passive and highly targeted” backdoor that makes use of the Security Assertion Markup Language (SAML) token, according to experts at Microsoft’s Threat Intelligence Center (MSTIC).
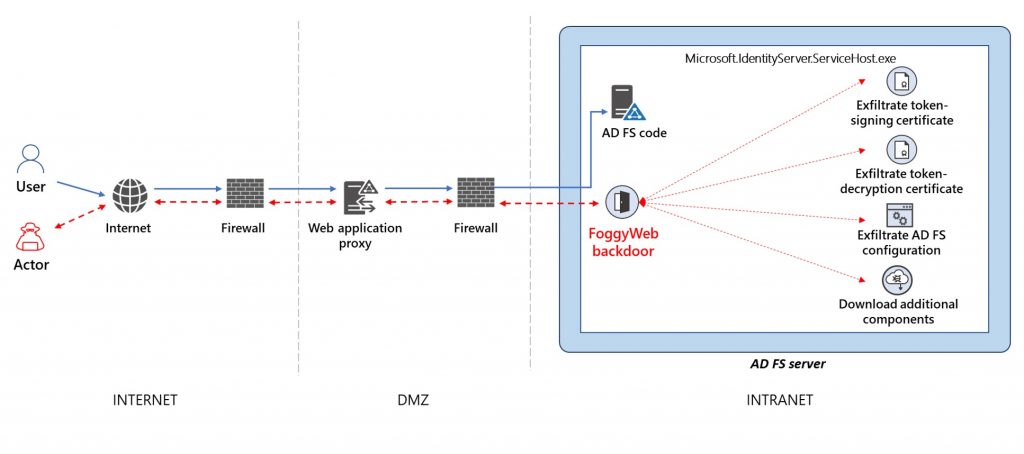
According to what has been revealed, FoggyWeb operates by setting HTTP listeners for actor-defined URIs and intercepting GET/POST requests sent to the AD FS server matching the custom URI patterns, in an attempt to remotely exfiltrate sensitive information from infected AD FS servers.
Aside from that, FoggyWeb is used to download and run additional components, as well as exfiltrate decrypted token-signing and token-decryption certificates. A command-and-control (C2) server may add additional malicious components to the hacked server, which can then be executed on it.
By configuring HTTP listeners for actor-defined URIs, FoggyWeb acts as a persistent backdoor that enables the misuse of SAML tokens and intercepts queries made to the AD FS server that match the custom URI patterns. According to Microsoft, the FoggyWeb backdoor has been put in active use since April this year.
Tips for defending yourself from FoggyWeb
Microsoft has notified users who were the target of this backdoor attack or whose data has been stolen. Organizations that think they might have been hacked or compromised are advised to perform full audit on-premises and cloud infrastructure, including user and app configuration, forwarding rules, and any other modifications the malicious actor may have made to retain their access.
In addition, it is recommended that they remove user and app access, review the settings for each, and issue new, strong credentials in accordance with established industry best practices. To stop FoggyWeb from stealing their sensitive information, organizations are also advised to install a hardware security module (HSM) on their server, as explained in Securing AD FS Servers.
Leave a Comment X