The Gootkit Malware
The criminals behind the Gootkit access-as-a-service (AaaS) malware have reemerged with modernized methods to trick victims into giving over their personal information.
In its previous tactics, Gootkit masked its dangerous files with freeware installers, but new research reveals that the malware is now using legitimate documents to deceive people into downloading these files, according to a write-up published by researchers at Trend Micro last week.
The recent revelations are an expansion on a previous analysis that was published by eSentire back in January. That research indicated massive attacks directed at workers of accounting and legal firms in order to secretly insert the malware on affected systems.
Gootkit is a component of the expanding underground ecosystem of access brokers. Access brokers are known to offer other malicious actors a pathway into corporate networks, for a fee, thereby opening the door for actual damaging attacks such as ransomware.
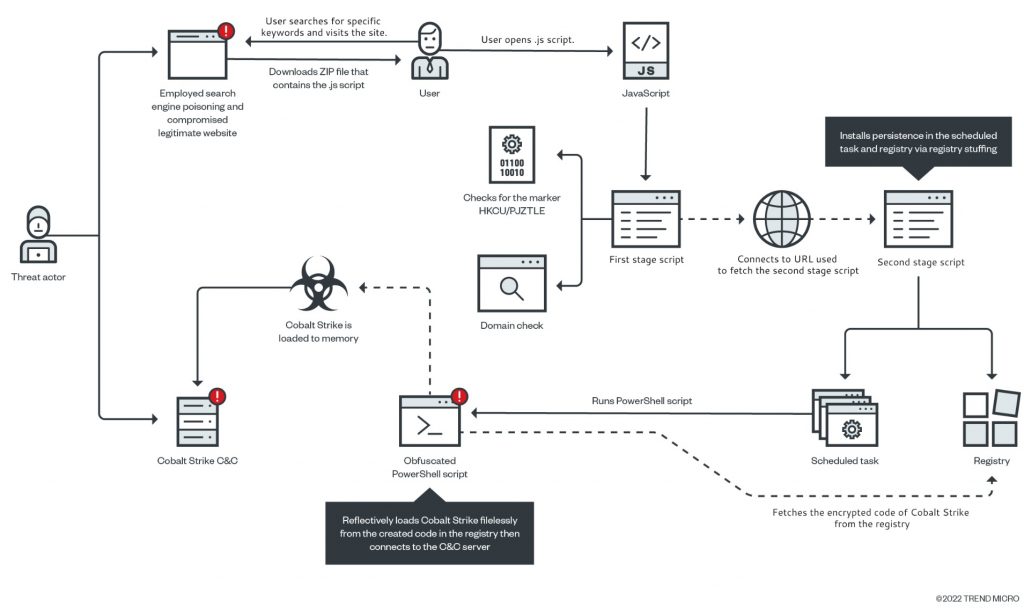
The malware loader uses a technique known as SEO poisoning, which relies on the display of malicious search engine results, that trick unsuspecting users into visiting compromised websites that host malware-laced ZIP package files. These files are typically presented as legitimate files related to disclosure agreements for real estate transactions.
According to the findings of the study, the combination of SEO poisoning and hacked genuine websites may hide the symptoms of harmful activity that would normally alert visitors to be on the lookout for them.
The ZIP package file that is malware-laced contains a JavaScript file that loads a Cobalt Strike binary in the compromised system. Cobalt Strike is a program that is used for post-exploitation operations and runs directly in the memory without using any files.
According to the experts, Gootkit is still operational and actively working to improve its methods. It seems that other threat actors are continuing to use this operation, which suggests that it has already been successful.
Leave a Comment X