Helpdatarestore@firemail.cc
If Helpdatarestore@firemail.cc has made its presence known on your PC, then you have been infected by one of the latest ransomware variants. Helpdatarestore@firemail.cc is sophisticated malicious code that requires a cautious approach.
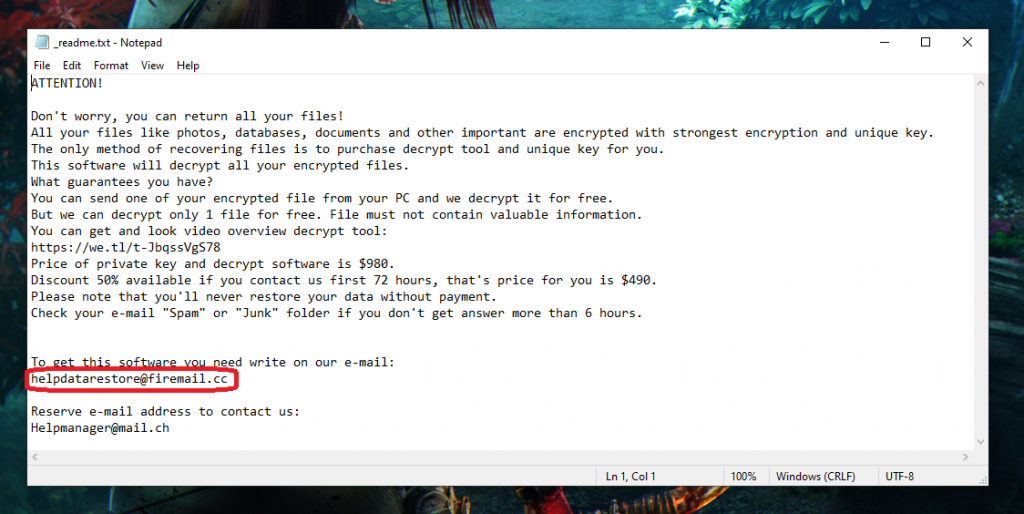
The hacker group will tell you in the .txt file to write to them on Helpdatarestore@firemail.cc so they can give you decryption software.
Helpdatarestore@firemail.cc falls into the category of file-encrypting ransomware, which is by far the most devastating kind. Unfortunately, as a result of attacks of this kind, users may end up permanently losing access to critical information. This, in turn, could lead to severe financial losses as well, especially if the files lost to the encryption were of professional value.
Hopefully, this won’t be the case for you. And we have suggested several options that don’t involve paying some anonymous criminals money in order to have your data restored to its original state. We cannot promise, however, that they will all be effective in your case, because all such cases are unique in their own ways. But it is certainly worth trying before you choose to resort to the ransom payment.
Important note: be sure to first follow the steps provided in the first part of the removal guide below. It is essential that you remove Helpdatarestore@firemail.cc from your computer before you attempt to recover your files, because otherwise any such attempts will simply be rendered futile.
Helpmanager@mail.ch
Normally, variants like the Helpmanager@mail.ch virus act in complete stealth and it’s almost impossible to detect them while they’re at work. This is in part what makes the Helpmanager@mail.ch virus so dangerous.
Helpmanager@mail.ch is placed in a .txt file in order to contact the group of hackers responsible for the encryption of your files.
Furthermore, most antivirus programs prove to be quite useless in the face of ransomware variants such as Helpdatarestore@firemail.cc. This is because, for the most part, the encryption applied by such malware doesn’t trigger a response from antivirus software. And that, in turn, is due to the simple fact that encryption is not in and of itself a malicious or harmful process. If anything, it’s actually a very useful and necessary thing that we rely on pretty much every day whilst we’re using the internet. It allows our online financial transactions, correspondence and other sensitive information to remain secure and safe from prying eyes. If it were to prompt a reaction from our security software all the time, we’d never get anything done.
The Helpdatarestore@firemail.cc file encryption
The Helpdatarestore@firemail.cc file encryption is a tedious process that can often also be very time-consuming. The Helpdatarestore@firemail.cc file encryption may sometimes cause a significant system slowdown which is the only symptom users can expect to experience.
And the leading sources of ransomware like Helpdatarestore@firemail.cc are spam messages and malicious online ads. In regards to the latter, these are easiest to avoid by simply not interacting with any forms of online advertising that you may come across online. There’s no way to tell a malicious ad apart from a safe one, therefore it’s best to just not risk it.
And as far as spam goes, here you might need to engage your discerning abilities a little more. But all in all, the general rule is to not interact with messages that come from unfamiliar senders, especially those trying to persuade you to open a link, enter a password or download some attached file.
SUMMARY:
| Name | Helpdatarestore@firemail.cc |
| Type | Ransomware |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Helpdatarestore@firemail.cc Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.
my files are encrypted whit mado virus. and i have important files. what should i do, i ran the recommended programs to remove the ransomware. but the files are encrypted. please help!
Hello sean, the removal programs can only help you delete the virus inside your PC, it cannot help you recover your files, you will have to wait for a working decryption tool to be released for that specific file extension.