This page aims to help you remove the Hermes 2.1 Ransomware for free. Our instructions also cover how any Hermes 2.1 Ransomware file can be recovered.
There is a new Ransomware virus named Hermes 2.1 Ransomware that appears to be a very malicious addition to this notorious malware family. Generally, as any other Ransomware, this new threat aims to invade your PC secretly, infiltrate its data and encrypt a certain list of targeted files. Usually, the virus may replace the file extensions and may place various ransom notifications on the victim’s screen, as well as inside the affected, files’ folders. You should be very careful not to come across any such type of viruses because they can, basically, block the access to your data and ruthlessly blackmail you if you want to release it.
The Hermes 2.1 Ransomware will encrypt your files
Even if our advice comes too late and this danger has already caught your computer, do not panic. First of all, you need to perform a proper and complete removal of Hermes 2.1 Ransomware to continue with the recovery of the files. Fortunately, it is not that difficult to remove the crypto virus by yourself, especially if you use the detailed instructions in the removal guide below. But the problem remains with the decryption of the files, locked by its secret encrypting algorithm. That’s why, in the next lines, we will do our best to help you in both – first, eliminating the infection and second, restoring your data in various ways. Just make sure you carefully read all the information provided and be realistic about your recovering expectations because Ransomware is indeed a very serious threat, the effects of which may not always be fully reparable.
The Hermes 2.1 Ransomware
The Hermes 2.1 Ransomware is a new variant of the Hermes Ransomware family. Like previous versions, Hermes 2.1 targets the data of its victims, encrypting it with a powerful algorithm. If the user wants to unlock their files, they must pay a ransom.
Judging by the latest reports, it seems that Hermes 2.1 Ransomware is a Ransomware threat that quickly gains popularity. The number of its victims is growing rapidly and the success of the infection has probably exceeded the expectations of its criminal creators. Hermes 2.1 Ransomware employs a number of tricky methods in order to sneak inside the users’ computers and take their data hostage.
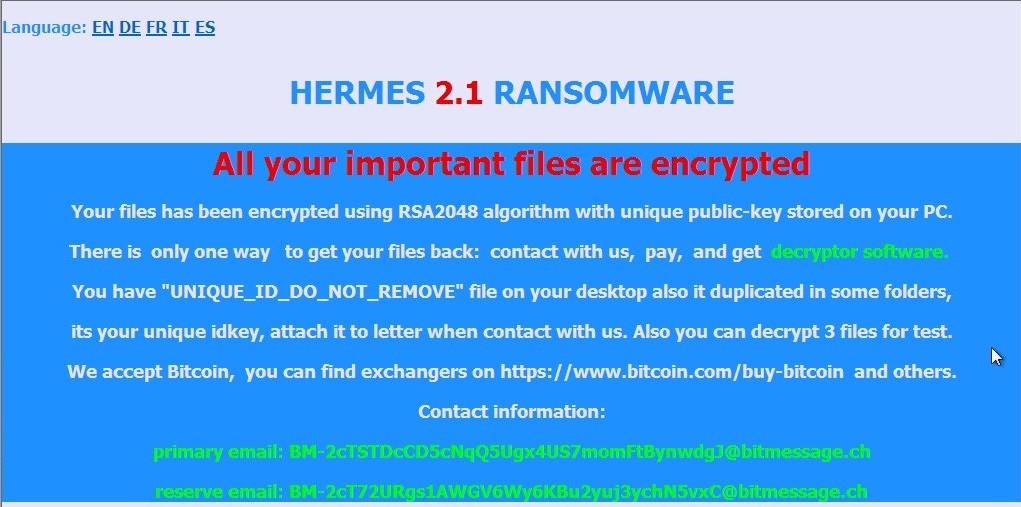
As per the current information, the malware spreads far and wide on the web and uses very good camouflage. Once it tricks the users and compromises their system, the Ransomware starts to infiltrate it. In addition, in order to cause more damage, the creators of the malicious program have set a wide range of file extensions to be targeted by the virus. Hermes 2.1 Ransomware basically searches for valuable files (such as office documents, images, videos, archives, etc.). Then it applies very complex encryption algorithms to all of them. The process may take some time, but the victim may not even notice it because the malware tries its best to remain undetected. When the encryption process is completed, a ransom note reveals the infection and its effects. There, the hackers place their ransom demands and prompt the victims to pay a certain amount of money if they want to decrypt their files. It is expected that the victims will make the payment and eventually receive a unique private key to unlock their files.
Unfortunately, since the encrypting algorithms that are used are based on very complex code, finding an alternative decryption key that can reverse the encryption without paying ransom is a rather difficult task. However, paying the criminals does not in any way guarantee that the victim will receive a decryption key, let alone that it will really work. For this reason, in case you are confused what to do, we would advise you to put aside any thoughts about spending your money on ransom payments and concentrate on removing the malicious software. Let the removal guide below help you make the process faster.
Hermes 2.1 Decryptor
Hermes 2.1 is a computer virus from the Ransomware category that gets distributed with the help of a AZORult Trojan Horse. Hermes 2.1 intimidates its victims into sending the hackers money by keeping their data encrypted until the payment gets transferred.
Most likely, Hermes 2.1 Ransomware has taken the chance to get into your device via an infected spam message. This is a common strategy for most Ransomware threats, as, unfortunately, this trend has been quite successful. After receiving a fake invoice or plain video file with an intriguing title, there are very few people who suspect that there might be a potential threat behind it. So, out of curiosity, users open the infected attachment, and then it is only a matter of a few seconds for the virus to install its scripts and perform its malicious actions. Also, some versions of Ransomware are commonly distributed using Trojan horses or exploit kits, masked inside seemingly harmless ads, links, web pages or software installers. To protect yourself from such insidious files, it is very important to improve your security with an appropriate antivirus application.
Steps to remove Hermes 2.1 Ransomware
Because we’re dealing with complicated malware encryption, we do not recommend doing it manually. In this regard, it is better to entrust the removal of Hermes 2.1 Ransomware to a security application. There are plenty to help you get rid of the virus, however, we recommend you use the professional removal tool. Alternatively, you can follow the manual removal guide in case you are a bit more confident in your computer skills. Once you have finished removing the virus, you may surely want to recover your information. That’s why we’ve given some suggestions under the article. You can also safely use your file backups, if you have any. Still, remember that you first need to remove the infection and only then try to restore your files. Otherwise, the file recovery may be unsuccessful.
SUMMARY:
Remove Hermes 2.1 Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.
I am currently desperate for a decryption solution for my files I was a victim of this Ransomware Hermes 2.1 and I hope that you can find a solution that can release and access my files again, the feeling of sadness that I am feeling I do NOT wish for anyone
I have Hermes 2.1 virous into my computer
How deciript my files
Please help me
Hermes 2.1 Ransomware. Are they any application to decrypt this malware as it has encrypted my 20GB data.
Hi Ram
you can go to this page How to decrypt ransomware and check any of the methods there