This page aims to help you remove Nasoh for free. Our instructions also cover how any Nasoh file can be recovered.
The category of Ransomware cryptoviruses is a highly dangerous and problematic family of malware threats. Here, we will go over the main characteristics of this group of viruses, and we will tell you what your options are if one new Ransomware threats named Nasoh has manage to enter your computer and lock your files with its advanced encryption algorithm. One thing you should remember while trying to deal with this insidious virus is that a full recovery of your data may not be possible at the moment. This due to the advanced encryption codes that threats like Nasoh use – breaking it or getting the decryption key may not always be an option, and the alternatives that you may use to bring back your files may also not be effective in all situations. Still, you should definitely take action towards handling this infection in the best way possible, or else, the consequences could be quite unpleasant and severe.
The .Nasoh virus
The .Nasoh Virus is the newest of the ever-changing ‘STOP Ransomware’ strain which has been plaguing users around the globe in 2019. The .Nasoh Virus primarily targets asian and african countries, through which it slowly spreads to the western globe.
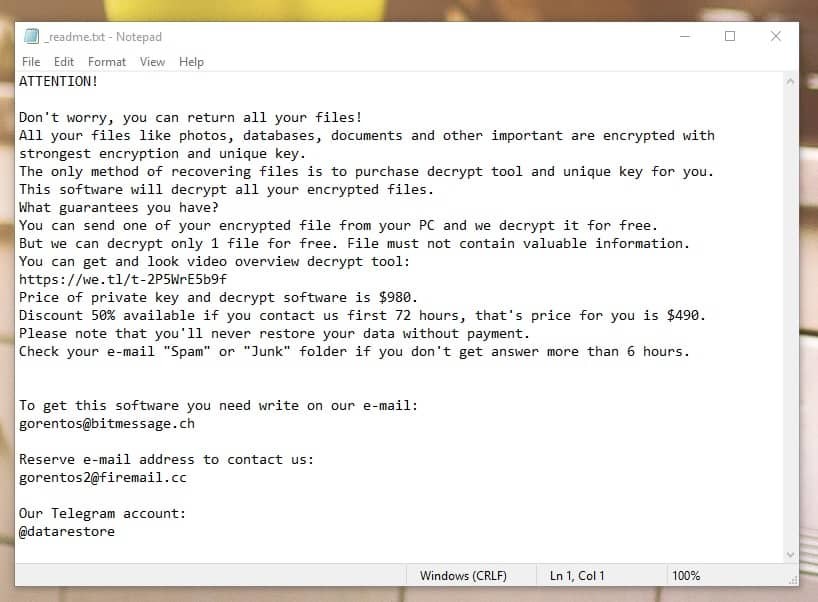
The Nasoh Virus will drop a _readme.txt file with instructions for you to follow
Like most other Ransomware threats, Nasoh doesn’t really give away its presence in the system with any visible symptoms while it is busy encrypting your files. The most you may notices is a slow-down of your system and decreased free hard-drive space while the encryption process is still in progress. Those symptoms, however, aren’t all that apparent, and may also be caused by many other things, so noticing a Ransomware doesn’t normally happen.
Another problem related to detecting Ransomware is that most antivirus programs lack the specialized features to spot this particular type of threats. Some advanced and high tier antivirus solutions offer detection features specialized for Ransomware but even those can’t guarantee that some sneaky threats like Nasoh, Coharos, Masok won’t manage to silently enter your machine and lock up your data. Because of this, and because of the lack of easily-noticeable symptoms, most infections of the Ransomware cryptovirus category manage to lock the files of their victims. Once the encryption is over, the virus itself makes sure to make its presence known by showing a banner on the user’s screen, in which the user is told about the money that is required of them if they want their files back.
The .Nasoh file lockdown
The .Nasoh file are basically and extension that signifies your files were encrypted. As in the picture below, a .Nasoh file appears only when it is too late to save the file. The ransomware works in the background and adds the extension to each file as it progresses.
These are the infected files by a new strain of the STOP Ransomware, modifying the extension with .Nasoh
Obviously, if the locked files aren’t that important, the problem isn’t all that big. In fact, removing the virus is totally manageable, and you can do it yourself as long as you follow the instructions from the guide below and use the recommended removal tool. However, even if the malware gets eliminated, this doesn’t mean yoru files would get automatically released, and if those files are important to you, and you have no backups of them, then you may be in trouble. Unfortunately, though there are methods you can try in order to restore your data, and some of those methods will be presented to you in the second section of our guide, we can’t promise that they will work for all of you. Still, trying them out won’t cause harm and it won’t cost you anything, which is why we encourage you to at least give them a try.
SUMMARY:
Nasoh Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.
Hi
I got infected with the ransomware .NASOH
These are the list of IP addresses that are below the localhost. Grateful if you could please help me to resolve and recover my files. I have no back ups of my files.
Please help.
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
5.149.252.98 www. gstatic. com
5.149.252.98 www. google-analytics. com
5.149.252.98 adservice .google .com
You should definitely delete those IP addresses from your Hosts file. After you remove them, be sure to save the file and complete the rest of the guide.
I got infected with the ransomware .NASOH. Grateful if you could please help me to resolve and recover my files. I have no back ups of my files.
Please help.
my important file is hacked and i want to get it in a fastest way
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
Those IPs shouldn’t be in your Hosts file, so you should delete them and save the changes.
Hi there. My pc also effected by nasoh virus. I tried all the methods but any of them doesn’t work. What if we format the pc and try to recover files. Is there any possibilities to get the files with their original format??
Formatting the computer won’t really help you restore the files. You can try the methods suggested in our How to Decrypt Ransomware article, but they may now work for all versions of Ransomware.