The Orchard Botnet
Researchers from Qihoo 360’s Netlab security team have spotted a new botnet named Orchard, that, according to them, uses Satoshi Nakamoto’s account transaction information to create domain names to hide its command-and-control infrastructure. According to the information that has been published, this method is more unpredictable due to the uncertainty of Bitcoin transactions, and, hence, more difficult to fight against.
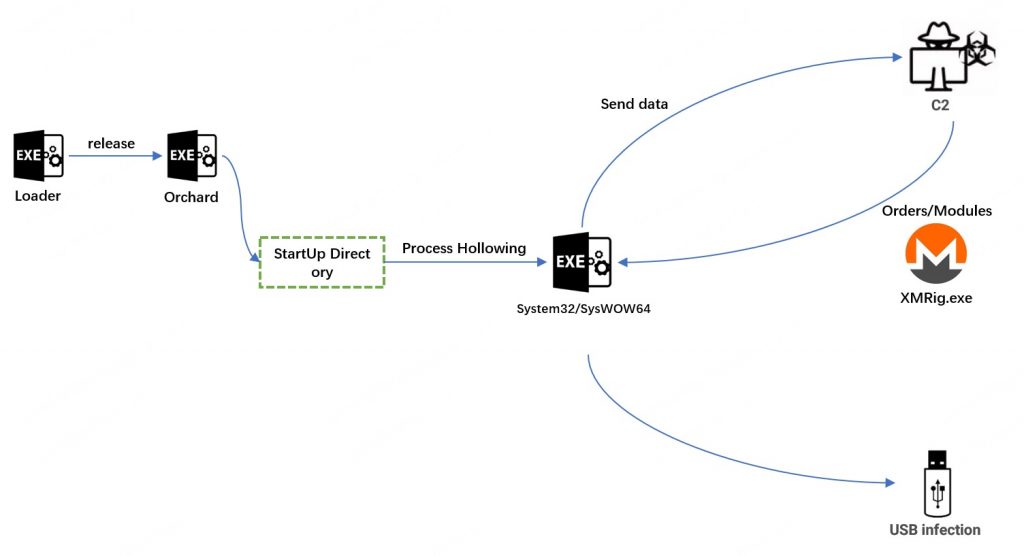
Since February 2021, Orchard is alleged to have undergone three upgrades, with the botnet mostly used to deliver additional payloads on a victim’s PC and execute commands and instructions received from the C2 server.
Aside from distributing malware, the botnet may also upload data and user information, collected from the infected device, as well as infect USB drives. More than 3,000 computers have been infected by the malware so far, according to analysis shared by Netlab, with the majority of victims located in China.
A year after its first release, Orchard has undergone several changes, including a short foray into Golang before returning to C++ for its third version. The latest analysis of the threat reveals that XMRig mining functionality has been added to the newest version, which makes it possible to mine Monero (XMR) using the compromised system’s resources.
The usage of the DGA algorithm in the attacks has also undergone some significant changes. The latest version of the malware uses balance information from the cryptocurrency wallet address “1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa“. Just for comparison, the previous two versions were using date strings to generate the domain names.
An interesting fact that needs to be noted is that the wallet address is the miner reward receiving address of the Bitcoin Genesis Block, the owner of which is believed to be Nakamoto. According to researchers, small amounts of bitcoin have been transferred every day to this wallet, so, its balance information may also be used as a DGA input.
Leave a Comment X