Ryuk
Ryuk is a Ransomware-based infection, focused on preventing users from accessing their information. Ryuk uses data-encryption and targets personal files and system records, making them inaccessible without a decryption key.
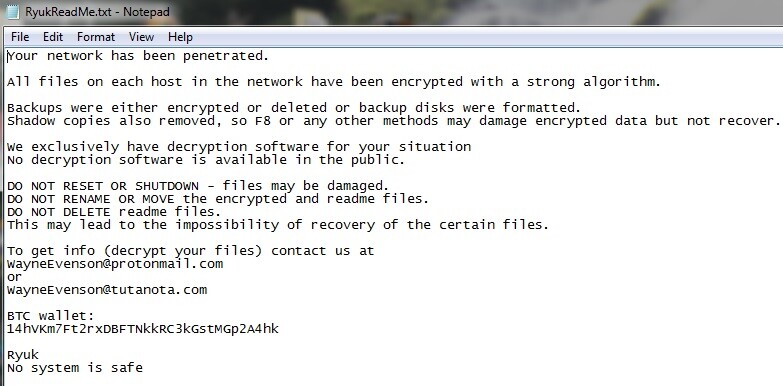
The Ryuk Ransomware will leave a .txt file with instructions
If a scary notification has suddenly appeared on your screen and it states that your files have been encrypted and you have to pay a ransom to decrypt them, then you have surely been attacked by a Ransomware virus. More precisely, you have probably landed on this page because of an infection with a recently discovered Ransomware-based cryptovirus called Ryuk. This virus is an advanced file-encrypting threat which targets computers all over the Internet, secretly taking blocking the access to their data and then proceeding to blackmail their owners. Upon the completion of the encryption, the malware places a ransom-demanding message on the victims’ screen and asks them to pay a certain amount of money, usually in Bitcoins or in some other cryptocurrency. Those, who agree to follow the ransom payment instructions are promised to receive a decryption key which is supposed to decrypt the encrypted files and convert them back to normal. Those who don’t fulfill the ransom demands, however, are threatened to never be able to access their files again. By landing on this page, you are probably hoping to find an alternative solution, which can help you deal with this nasty blackmailing scheme and eventually bypass the ransom payment. Fortunately, we have something to offer you here – below there is a Removal Guide and a trusted malware removal tool which may help you remove Ryuk Ransomware from your system. In the next paragraphs, you are also going to find useful information about the way this Ransomware operates as well as some helpful data protection and file-restoration tips, which may help you minimize the negative consequences of the infection without paying the cyber criminals.
The Ryuk Ransomware
The Ryuk Ransomware is a cryptovirus that seeks to encrypt digital data that is stored on the infected computer. After the attack, the Ryuk Ransomware will ask for a ransom payment to release the encrypted files from the applied encryption.
The term Ransomware raises fear in many web users. This type of malware is famous for its dreadful attacks and their malicious consequences which, to this day, still have no a hundred percent effective method for counteraction. The successfulness of threats such as Ryuk Ransomware to an extent is a result of their ability to remain undetected by most forms of software security that the user might have on their PC. Such infections use various “social engineering” techniques to sneak inside people’s computers and rarely trigger any visible symptoms of their presence until they complete their malicious action. The main reason for that is the file encryption process which the Ransomware-based infections typically use. The file encryption process isn’t normally seen as something malicious because it’s original purpose is actually to help the users. This is one of the most secure and unbreakable data protection methods and is commonly used by software developers for securing important data. Your antivirus software will most probably not detect it as a dangerous process since the file encryption isn’t really going to actually harm or corrupt anything. Therefore, in most of the cases, users fail to spot the threat on time and the virus is allowed to seal the files it has targeted.
The Ryuk Ransomware Decryptor
The Ryuk file decryption is a file-decoding process that can make the encrypted files accessible again. For the Ryuk decryption to be performed, the users need to apply a decryption key, which is held by the hackers behind the Ransomware.
Sadly, the goal of the Ransomware is not to protect your data but to take it hostage by applying its secret algorithm which cannot be decrypted without a specially generated decryption key. That key, as you may guess, is generated at the hackers’ servers and they would gladly offer it to you in exchange for a big ransom sum. But what should you do if you don’t want to pay the ransom? Well, the first thing you should actually think about is how to remove the active malware from the computer. In the Removal Guide below, we have given you instructions for that. This way, you will be able to safely proceed with alternative solutions which may help you recover some of your files. One of the things you should definitely do is check for backup copies of your data. You may have such copies on external drives or on a cloud storage or you may keep some files on other devices, in your email, USB drives, CDs/DVDs, etc. Use them to get back some of your files or give a try to the file-restoration instructions that we have listed below.
Of course, you can decide to pay the ransom as well and hope that the hackers will send you the decryption key they promise. We need to warn you, though, that this course of action hides its risks. In fact, you may end up throwing away your money without getting anything in return because there are cases in which the hackers simply disappear when they get the ransom payment and they never send the so desperately wanted decryption key to their victims. If you are anyway ready to pay, it is far better to consider contacting a professional you trust and receive reliable help rather than sponsoring some anonymous cyber criminals who may trick you any day. Sadly, we cannot give you guarantees of which method will work the best in your particular case because, as we said above, Ransomware that lacks a single truly effective method for counteraction. Still, if there are alternatives that do not involve making the payment, we encourage you to give them a try.
SUMMARY:
How to Remove Ryuk Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.
Hello….How do I know whats new and old in regedit folders and what to delete?
Thank you
Hi Pesh,
in the guide says “Once inside Regedit, press CTRL and F together and type the virus’s Name” did you do that ?