Attention: Taskeng.exe is a normal windows process which predetermines the time some tasks are performed in. However, there are instances a Trojan Horse can disguise itself as the process. The article below is dedicated to this Trojan horse.
The Taskeng.exe Virus
Taskeng.exe is a legitimate Microsoft Windows process which is an important part of the operating system. There are some reported cases of a Trojan horse virus hiding under the name Taskeng.exe.
The Taskeng.exe Virus can disguise itself as a normal windows process.
Here, we will focus on one particular Trojan horse program called Taskeng.exe Virus that is currently terrorizing users all over the globe with its malicious processes and harmful agenda. We assume that many of the users who are currently reading this article have ended up on this page because the malware has already reached their PC. We could help you handle the virus threat and eliminate the noxious piece of software from your machine by presenting you with a guide, which contains instructions on how to locate and remove the infection. However, you must first make sure that you are well acquainted with this particular type of malware, which is why we advise you to first read the remainder of this article and only then head down to the removal guide manual. Besides, in one of our next paragraphs, you will learn how Trojans like Taskeng.exe Virus get distributed to people’s computers and what you can do in order to prevent this from happening to you in the future. You have probably already heard about Trojan horse viruses. This is a malware type infamous for its high levels of versatility and potential to cause all sorts of issues once it has infected one’s computer.
What is Taskeng.exe Virus?
A Trojan horse such as Taskeng.exe Virus is a malware type infamous for its high levels of versatility and potential to cause all sorts of issues once it has infected one’s computer. Programs like Taskeng.exe Virus are extremely sneaky and stealthy, most of the time the best way to detect them is to have a reliable and fully-updated anti-malware program.
Some possible signs of infection might include system slowdown, BSOD crashes or frequent errors; but depending on what the malware is used for, you might not notice any of these.
Trojan horse versatility
If Taskeng.exe Virus has currently taken over your machine, you might need to know what it can potentially be used for. As we already stated, the Trojan horse type of malware is notorious for its ability to carry out all sorts of illegal tasks and run a wide variety of insidious and harmful processes on the infected machine. As long as the malware has been run under Administrator privileges, it would be able to do whatever the hacker who’s using it wants to use it for. A few examples of what a typical Trojan can be used for will be provided below:
- Harming the PC system – A lot of Trojan horses are simply used to mess with the computer, significantly slowing down its productivity, causing all sorts of unpleasant errors or even crashing it to the dreaded Blue Screen of Death (BSOD). Many computers become totally unusable after a virus like Taskeng.exe Virus has invaded their systems.
- Spying on the user – Espionage is another thing that this malware could be used for. The nasty program might keep tabs on what you type on your keyboard (keylogging) or show the hacker what’s going on on your PC’s monitor. Furthermore, if you have a webcam, the malicious program could use that to directly spy on you even when you think that the cam is disabled and not being used.
- Malware distribution – Oftentimes, viruses like Taskeng.exe Virus are also used to infect the targeted PC with additional viruses. One very common example is when a Trojan is used to infiltrate somebody’s PC and later infect it with Ransomware that can encrypt the personal files of the victim and request a ransom payment for the decryption key.
- Taking over the computer – Apart from what we’ve mentioned so far, this type of malware can sometimes go as far as to take over the user’s PC and remotely use it for a variety of shady tasks some of which are the distribution of spam messages or the mining of bitcoins for the hacker’s profit.
The aforementioned potential uses of Taskeng.exe Virus are only part of all the possible ways in which such a virus can be employed. Generally, if you have landed such a virus, all sorts of bad things can happen to your machine and virtual privacy, which is why it is essential that Trojans are taken care of as soon as they get detected.
Methods for spreading Trojans
There are a number of ways via which a virus like Taskeng.exe Virus can get on your PC. Some common examples are different forms of online malvertising and deceitful Internet offers/notifications as well as spam messages and untrustworthy download sources. If you want to avoid landing any such viruses on your computer, you ought to make sure to stay away from anything online that could be a potential hazard for your PC’s security and safety. Do not click on any suspicious banners and ads and keep away from sites that do not seem like they can be trusted. Also, if anything that is sent to you (an e-mail, a Facebook/Skype message, etc.) looks sketchy, do not interact with it to avoid exposing your system to possible risks.
SUMMARY:
| Name | Taskeng.exe Virus |
| Type | Trojan |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove Taskeng.exe Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
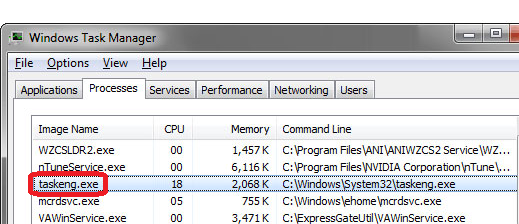
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone



Make sure you remove all of these IP addresses from your Hosts file as they are not supposed to be there.
After that where do I need to save the file at?
You should save the file in its original directory.
it said “access is denied” when i try to replace
Do you have Administrative privileges on the PC you are using?
https://uploads.disquscdn.com/images/e803f65e17c58f902c45b00b1b7db2bcc5a07daf478a3feb01cc89b2b60d0e1f.jpg https://uploads.disquscdn.com/images/d129690438c787794ce5ccc06c63112ca54308dc3c2c97bf4b016d89066118f8.jpg
which folder should I delete? please help T_T
Search for a folder that has the name of the unwanted software by pressing Ctrl+F and then typing the name of the software. WE don’t see any suspicious folder on the screenshot.