Udacha
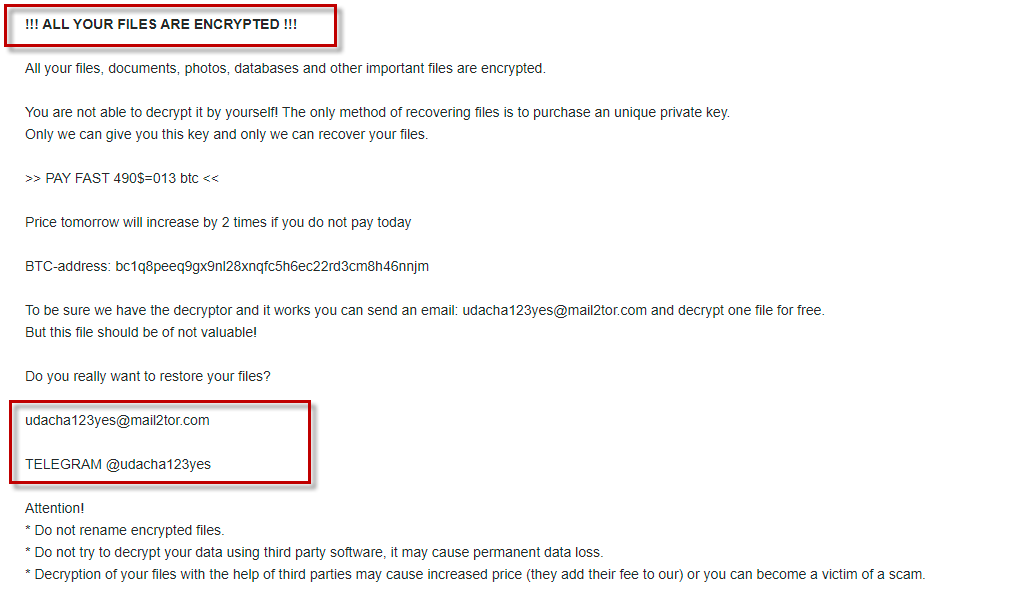
Udacha is malware that attacks Windows systems seeking to block its victims’ access to the files located there. Udacha initiates a data-encryption process that restricts the access to the affected data and then tells the user to pay ransom for the decryption key.
Getting hit by a Ransomware such as Udacha can be a big problem for users who keep important digital data in their computers. Oftentimes, people get some important information related to their work, education, or hobbies locked up by a virus such as this one, and in those cases the options for retrieving the sealed data are not very many. Our goal in this article is to tell you about the possible courses of action you can take, and to help you decide which the best one is for your particular situation. For example, if Udacha or Koom has attacked your computer but there aren’t any valuable or important files in it, you should directly head down to the removal guide below and follow the steps listed in it to remove the threat. The files that the virus has locked would still remain inaccessible but if they aren’t that important to you this shouldn’t be a huge issue.
The Udacha virus
The Udacha virus is a Ransomware file-encrypting virus – a type of malicious program that “kidnaps” user files and makes a ransom demand for their release. Malware like the Udacha virus often gets distributed through the help of a previous Trojan Horse infection.
If you, however, are a person who has some highly sensitive and important data in their infected by Ransomware computer, then you’d surely want to find the best way to recover as many files as possible. One thing you must realize is that full recovery is sometimes not achievable, especially with newer and more advanced Ransomware infections like Udacha. Still, there are quite a few things you can try, so you should definitely not give up.
The Udacha file
The Udacha file is a file that has been rendered inaccessible after this virus has encrypted it. The hackers claim that no Udacha file can be accessed if the corresponding key isn’t present on the computer, and they demand a ransom payment for said key.
One option many users might consider is paying the ransom that Udacha demands from its victims in exchange for the decryption of the sealed data. This might seem like a tolerable option to those of you who have the required money readily available and who really, really need the locked files back. However, one must always remember that the hackers have all the freedom to refuse to send you the private key for the data’s decryption even after all of the requested money has been transferred to their virtual purses. That is why it is pretty much always preferable to at least try the other possible solution that might be out there. For example, you can start with removing Udacha which will open options such as connecting backup devices to your computer in case you have such. And if you don’t have backups, there are some free online decryptors for various Ransomware versions that can sometimes prove helpful. We have a list of such tools on our site (in the second part of the removal guide below) so make sure to check it out. Shadow-copy recovery may also be possible – you can learn more about that from the guide. However, before you opt for any of these methods, you must make sure to clean your computer from the Ransomware, and the next instructions will show you exactly how to do it.
SUMMARY:
| Name | Udacha |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove Udacha Ransomware
To remove the Udacha virus, first make sure that any rogue programs on your computer are deleted, then quit the Ransomware process, and finally revoke any changes made by the virus in the system settings.
- Search the list of program installs in Programs and Features for potentially malicious programs and uninstall the ones you think may be linked to Udacha.
- Open the Task Manager and remove from it any questionable processes that may be from the virus.
- Check the Registry Editor and the Startup items for unwanted entries and if you find anything questionable there, delete it.
- Finally, delete any malicious files that may be stored in one or more of the following folders: AppData, LocalAppData, ProgramData, WinDir, and Temp.
The steps above only outline the removal process of Udacha – if you need more details about the completion of one or more of those steps, please, read on – the following is an expanded version of the removal guide.
Expanded Removal Guide
Start by searching for rogue programs on your computer and uninstalling them. By going to Start Menu > Control Panel > Uninstall a Program, you will see a list of all programs that are installed on the computer. Search that list for anything questionable that you think may have introduced the Udacha Ransomware to your system. Pay special attention to any programs installed just before you realized that your system is infected.
If you think that a certain item from the Uninstall a Program list may be related to Udacha, click on it, then click on Uninstall, and complete the uninstallation process. If the uninstaller asks you whether you’d prefer to keep personalized settings for the program or any other type of temporary data, choose not to keep such data – everything must be deleted with the uninstallation.
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Use the search box under the Start Menu to find the Task Manager utility and then open the latter. In it, open the Processes section where you will see what processes are running in the system at the moment. If the Ransomware is still active, its processes should be shown there.
The majority of Ransomware threats require significant amounts of system resources (virtual memory and processing power) to operate. Therefore, it’s likely that the Ransomware process would be shown at the top of the list, among the most resource-intensive processes.
If you see a process with an odd-looking or unfamiliar name, especially one that is using up a lot of resources, look it up and if there are other users or security researchers that say the process in question is related to Udacha or to other malware, then do the following:
- Right-click the process in the Task Manager, access its File Location, and scan all files that are in it with the online scanner posted below (it is free, and you can use it straight from the browser):Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To ScanAnalyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
- Should one or more of the tested files turn out to be malware, you must first quit the malicious process – right-click it and select the End Process option.
- Next, you must delete its entire location folder with all of the files stored in it (including ones that didn’t get flagged as threats by the scanner).
- If the virus prevents you from deleting its folder, try to delete as many of the files that are in the folder and then continue with the rest of the guide. Once the other steps are completed, you should have no problem deleting the file location folder of the malicious process, so be sure to do that once you complete the guide.
Important Note: If the scanner finds no malware in the scanned files but the information you found online comes from a reputable source, is conclusive, and says the process is malicious/unwanted, you should still go ahead and quit that process and then delete all files related to it.
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Your PC must be in Safe Mode while you are completing the remaining steps as this will help prevent any malware processes that you didn’t manage to find and quit from interrupting your attempts to delete the virus.
The following line must be placed in the Start Menu after which you must hit Enter: notepad %windir%/system32/Drivers/etc/hosts.
If Windows needs you to select a program with which the file will be opened, opt for Notepad.
When the text file pops-up on your screen, see what text is at its end – if the file has been modified/hijacked by the virus, there will be text (usually suspicious IP addresses) after “Localhost“. If you see such text/IP addresses, copy everything after “Localhost” and send it to us in the comments. After we see what text you’ve sent us, we will be able to determine if it is from the virus, and we will tell you what to do next in a reply to your comment.
A Word of Warning!: In this step, you will have to find Udacha items in the computer’s Registry and delete them. The Registry stores many sensitive and important system settings, so you must be really careful not to delete something that’s from the system and not from the virus. For that reason, we recommend consulting the members of our team by writing us a comment below this post whenever you feel uncertain about whether you are supposed to delete a given item from the Registry.
To access the Registry Editor, first press together Winkey and R and then type regedit in the Run search box. Hit Enter and if you get asked to allow the Registry Editor to make system changes, give your permission by clicking on Yes.
Once you see the Registry Editor utility on your screen, select its Edit menu and then select Find. In the search field, type Udacha, hit Enter, and delete whatever gets found. To see if there are other Udacha items, repeat the search and delete the next thing. Keep doing this until you have deleted all results for Udacha.
You must now manually go to the three Registry directories shown below:
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
It is possible that they may contain Udacha-related items that wouldn’t get found if you searched for Udacha in the Registry. See if you see any entries in those directories that seem strangely-named. For instance, an item with a very long name that looks like a random string of letters and/or numbers is likely to be related to Udacha or to another unwanted/malicious software. You should delete any such items you see in those directories, but it’s advisable to first consult us before the deletion.
One last thing you must do is access each of the folders we’ve listed below and delete any rogue files that may be stored in them. To go to each of those folders, simply copy its entry from below (copy it with the “%” signs), place it in the Start Menu, and press the Enter key.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
In each of the folders, delete the most recent files – all files created after the Ransomware’s arrival on your computer. When you get to the last folder (Temp), delete all of its files.
Use Professional Removal Software
If the manual steps don’t seem to be effective, it may be time to try deleting the virus with the help of a professional anti-malware program. Many of the newer Ransomware threats are very advanced and deleting them manually may prove to be too difficult even for an expert. Additionally, it must be said that many Ransomware viruses attack the system helped by a Trojan Horse that introduces them into the system and then helps them gain persistence and become difficult to manually remove. For that reason, the best option in cases where the manual instructions don’t help would be to eliminate the threat with a specialized malware-removal program. We strongly recommend one such program that you will find linked here, on the current page – it will find any malicious software and data on your system and delete it quickly, and without any risk for the system.
How to Decrypt Udacha files
To decrypt Udacha files, you must make sure that the virus is removed from the system and then try any of the available data-recovery methods. To decrypt Udacha files, you can also pay the ransom but this is inadvisable because the hackers can’t be trusted.
Once you’ve made sure that the threat is deleted, our advice is to visit our How to Decrypt Ransomware article where you will find a compilation of the best alternative data recovery methods we’ve been able to find along with an explanation of how to apply them. However, remember that the virus must first be removed so as to prevent it from encrypting your data for a second time.
Lastly, remember that if you suspect that there are any remaining malware file son your computer, you can always check them for malicious code with our online scanner that you can use for free at any time, without need to install anything.
HI,
my pc was hacked and attaked udacha virus. How may I recover data?.pleae help me.
Hi mohan pandi,
Udacha virus is still a new virus and there is no decryption available yet. i would suggest to you to bookmark this page and wait for decryption.