The Jupyter Malware distribution via MSI installers
A .NET infostealer named Jupyter has been tracked by security experts for its propensity to target healthcare and education organizations. The malware seems to be particularly effective at evading conventional endpoint security scanning solutions, according to the revealed information.
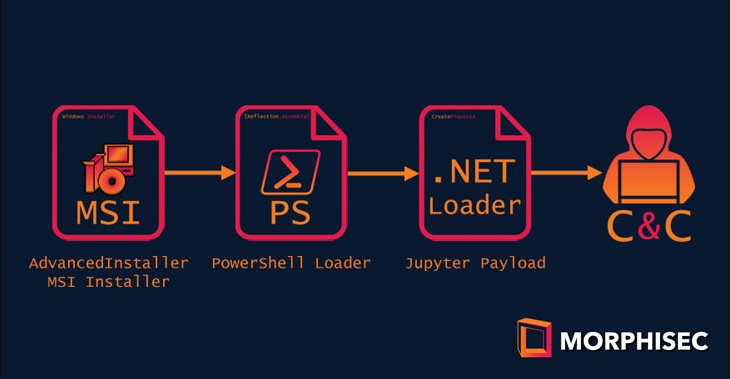
The delivery chain of Jupyter shows how threat actors continue to evolve their attacks to become more efficient and elusive. Morphisec, the Israeli firm that discovered the new delivery chain, it is now examining the attack’s scale.
Jupyter (also known as Solarmarker) was first discovered in November of 2020. What is known about the malware is that it primary targets the data stored in Chromium, FireFox and Chrome browsers. It has additional capabilities that allow for full backdoor functionality, including features that siphon data, upload the details to a remote server, download additional payloads, and execute them. Insights from Morphisec’s forensics team indicate that numerous Jupyter versions started to appear around May 2020.
The attacker is a “very skilled perpetrator” focusing on credential and residual information theft, according to security researchers. This statement is supported by the fact that the malware has a multi-stage, highly obfuscated PowerShell loader that launches a.NET built backdoor once it has been executed.
As per what has been revealed, the current attack chain uses a new PDF program named Nitro Pro. The anti-malware engines are smartly bypassed through the use of MSI installer payloads exceeding 100MB in size. These payloads are obfuscated using a tool called Advanced Installer, a third-party program packaging wizard.
Once the MSI payload is executed, a PowerShell loader signed with a valid certificate belonging to a real Polish company is activated in Nitro Pro 13, allowing for certificate impersonation or theft. The last step of the attack chain is when the in-memory Jupyter.NET module is decoded and executed.
According to Morphisec researcher Nadav Lorber, the development of the Jupyter infostealer/backdoor since its discovery in 2020 shows the validity of the notion that threat actors are always inventing new and more sophisticated methods for invasion. The fact that this type of attack successfully managed to bypass most security tools indicates just how adept threat actors have become in eluding malware-detection solutions.
Leave a Comment X