Qmak
Qmak is a malware program of the STOP/DJVU Ransomware family, and it has the ability to block all access to your most valuable files. Qmak applies strong encryption to the targeted files to lock them and then demands a ransom for the decryption key.
The Ransomware category of malicious programs is well known at this point, as it is among the most widespread and difficult to counteract and defend against forms of malware. Rather than harming the victim’s files or system, Ransomware threats lie Qmak aims to put the user’s data under a lockdown by using an advanced encryption algorithm that prevents anyone who doesn’t have the matching decryption key from accessing, using, or modifying the locked file.
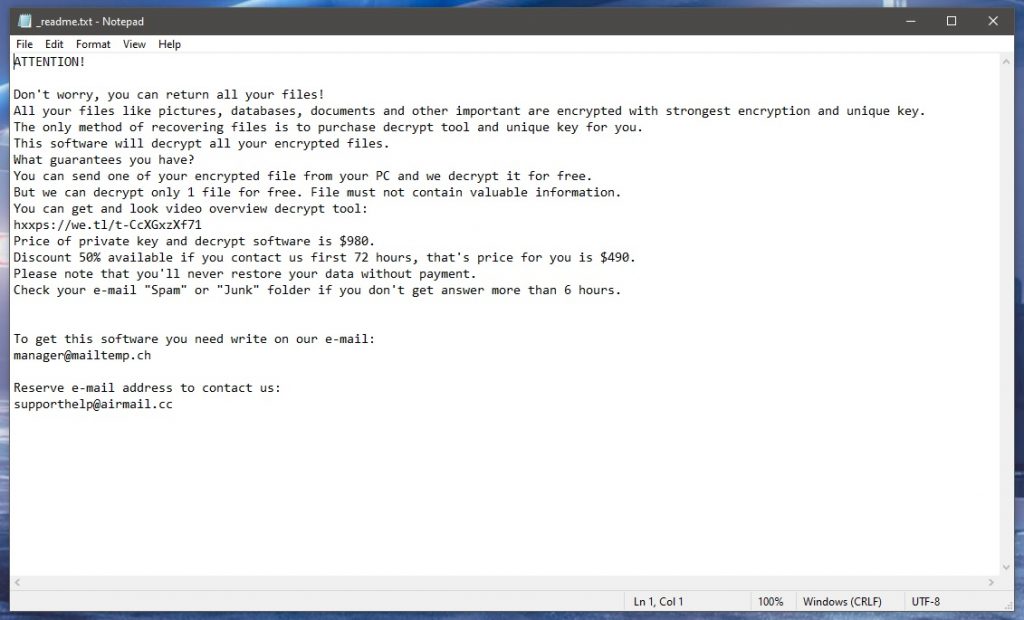
In the case of the Qmak, the Ransomware threat uses Salsa20 + RSA-2048 algorithms to render its victims’ files unavailable. Upon applying the encryption to the targeted files, the malware program automatically makes its presence on the computer known through a notepad file named _readme.txt in which the virus informs its victim about the current inaccessible state of the encrypted files and about the ransom demanded to receive the key that can unlock them.
The Qmak Virus
The Qmak virus is a malicious Ransomware program that specializes in file-encryption and money extortion. The Qmak virus is capable of secretly making your files inaccessible through encryption that can only be removed via a unique key, for which you must pay a ransom.
The attack from such a malware program can be devastating if you have any highly-important and valuable files on your infected computer. Of course, if those files have previously been backed up, then the problem with the virus attacking you wouldn’t be so significant, but, unfortunately, most users get caught off-guard by such Ransomware threats, when they don’t have any extensive data backups.
If you’ve noticed a strange .qmak extension at the end of the names of some (or all) of your files, this means that the Qmak virus has encrypted them and that you’d no longer be able to access them without the decryption key. If you really need those files back, you have two options to restore them:
The first one is to pay the ransom requested by the hackers, but we strongly advise against this approach as you may simply waste any money you send to the criminals without ever restoring your data. The second method is to employ a special decryption tool that may be able to reverse-engineer a decryption key for your files.
The .Qmak file encryption
The .Qmak file encryption is what keeps your files inaccessible, and a unique key is required to be able to open the locked files. You might be able to reverse the Qmak file encryption without paying the ransom, by using a free specialized decryptor program.
However, before you make any attempts at restoring files locked by the .Qmak virus, you must make sure that the latter is no longer in the system. Not only that, but you must also ensure that there aren’t any supplemental malware programs hidden in your computer. To make your PC malware-free again, before you try to restore your data, we advise you to follow the removal steps we’ve shown below. After the removal guide, we will show you how you may be able to decrypt your files without paying the Qmak ransom.
SUMMARY:
Remove Qmak Ransomware
First, click on the Bookmark icon of your browser to save this Qmak removal guide because you will need to get back to it in order to complete all the steps.
Next, we highly recommend you to perform the steps that follow under the Safe Mode of your computer.
To reboot in Safe Mode, please use the guide from the link and, once you complete it, get back to this page that you have bookmarked.
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
In case of a ransomware infection, it is very important that you stop any startup items that the malware might have added. To do that, go to the search bar in the Start menu and type msconfig in the search field.
Next, press enter and click the Startup tab in the System Configuration window:
You will see a list of startup items. Your job there is to determine if there are any Qmak-related items or malicious entries that are set to start when your computer starts. Please keep in mind that the ransomware may use fake name and fake Manufacturer to conceal its malicious startup items that’s why if needed, take your time to research online each of the items that look suspicious.
If you locate a malicious item, uncheck the checkmark from its checkbox to disable it and then click OK to save your changes.
The next location where you need to search for dangerous items is the Task Manager. Press CTRL + SHIFT + ESC from the keyboard to open it and then click on the Processes Tab. If you spot a process that has a random name or a process that uses a lot of CPU and Memory and you cannot explain that with any particular legitimate activity or a program that you are running, do the following:
With a right-click on the suspicious process, select Open File Location.
Next, drag and drop the files of that process in the free online virus scanner below:
In case that the files that you scan get flagged as malicious, then you should end the process and delete them along with their folders.
If you have a suspicion that, aside from the ransomware, some other threat may also have compromised your computer, it is a good idea to check your Hosts file for malicious changes. To do that, copy this line:
notepad %windir%/system32/Drivers/etc/hosts
Then paste in the Start menu search bar and press Enter.
If you are hacked, one of the most visible signs of hacking is the presence of dozens of strange IP addresses in your Hosts file under Localhost in the text:
If you find suspicious IPs below “Localhost” in your Hosts file, it is best to write to us in the comments, so we can advise you on what is best to be done.
To remove parasite on your own, you may have to meddle with system files and registries. If you were to do this, you need to be extremely careful, because you may damage your system.
If you want to avoid the risk, we recommend downloading SpyHunter
a professional malware removal tool.
More information on SpyHunter, steps to uninstall, EULA, Threat Assessment Criteria, and Privacy Policy.
Finally, if you want to remove all traces of Qmak permanently, you should not forget to check your registry for ransomware-related entries.
The easiest way to do that is to open the Registry Editor (type Regedit in the search bar of the Start menu and press Enter).
When the Editor launches, open a Find box (CTRL and F) and type the name of the Ransomware in it. Then press Find Next and if any results appear with that name, make sure that you delete them. Be extremely careful though, because if you delete an entry which is unrelated to the infection you may seriously corrupt your OS and the legitimate software installed in it.
After you are done, close the registry editor and go to the search bar of the Start menu. In it, type each of the following and open the folder:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
To remove any traces of Qmak, delete everything in Temp. In the rest of the folders, just check if anything new and random has been added and if you think that something is part of the infection, remove it.
In case you need help, or you run into trouble, feel free to leave us a message in the comments. For quick and risk-free removal of Qmak and all of its related files we recommend you use the powerful anti-virus program we recommend or scan the files that you find suspicious with our free online virus scanner.
How to decrypt Qmak files
To decrypt Qmak files, you are advised to use a specialized decryptor tool for Ransomware viruses of the STOP/DJVU family, rather than pay the ransom demanded by the hackers. Before trying to decrypt Qmak files, however, you need to ensure your PC is malware-free.
We already explained how to clean your system in the previous steps, so if you have completed them and can confidently say that there’s no more malware on your computer, you can follow the next instructions to hopefully restore those of your files that the Qmak virus has encrypted.
Before you try to use the decryptor, however, know that you will need to have one (preferably more) file pairs, where one of the files in each pair is encrypted by Qmak, and the other is its original and accessible version. To try to find such original and accessible versions of encrypted files, we recommend looking for them in other devices, USB flash memory sticks, external drives, phones, tablets, cloud storages, and even inside email letters you’ve sent or received. If you find such original and accessible versions of some of your encrypted files, you will be able to use the decryptor tool shown below to reverse-engineer the necessary decryption key.
- Open this link, click the first Choose File button, find the encrypted version of one of the file pairs, and open it.
- Use the second Choose File button to find and open the unencrypted, original version of that same pair.
- Click Submit to begin the process of extracting the decryption key. If an error occurs, you will have to try again with a different pair of files.
- Download the decryptor program that you will find on this page.
- Right-click the executable that you just downloaded (decrypt_STOPDjvu.exe) and select the Open as Administrator option.
- When the app opens, click on I Agree after reading the Terms and Conditions and then click OK on the next window.
- Select the drive or specific folder where there are encrypted files and then click Decrypt to begin unlocking the files. If any of the files get skipped, it means that the key that is currently being used cannot unlock them and you will need a different key. You may be able to extract it using a different pair of files, but it is also possible that the required key is simply not in the decryptor program’s database.
Qmak is a malware threat that sneaks into the computer unnoticed, locks the most important user files, and then places a ransom-demanding message on the screen. If the Qmak victim doesn’t pay the ransom, they’d never receive the decryption key that can unlock their files.
During the encryption process of the victim’s files, the virus shows almost no symptoms, so it’s very difficult and unlikely to notice its presence. In addition, oftentimes even the best security programs out there fail to recognize the activity of such malware and intercept it, which is one of the main reasons behind the high success rates of threats like Qmak.
After the encryption is completed, the main symptoms of the malware infection are the user’s inability to open any of the encrypted files and the presence of a ransom note in the form of a notepad file or a banner shown on the computer’s screen. This note details the ransom demands of the hackers and gives instructions on exactly how to perform the payment, which is often demanded in Bitcoins or another cryptocurrency.
Qmak is a virus that encrypts valuable data in order to make it inaccessible and requests a ransom payment from the data’s owner for the decryption key that can unlock it. The Qmak virus doesn’t damage the computer but could lead to severe data loss.
The encryption of the virus, once applied to your files, won’t automatically go away if the malware gets deleted from the computer. In other words, even if you manage to remove Qmak, you’d still have to deal with its encryption. That said, the removal of the virus is still a crucial part of dealing with such a malware attack because this could prevent Qmak from locking up any more files in the future.
In addition, once you remove the virus, you’d have the option to try different alternative data-recovery methods that do not involve making a ransom payment. This is, in fact, the course of action that we recommend for those of you who have been attacked by Qmak.
To decrypt Qmak files, you can either send the ransom money to the hackers or attempt to recover the files on your own, using alternative methods. When trying to decrypt Qmak files, we recommend exhausting all alternatives before opting for the ransom payment.
The reason we always try to discourage our readers from giving in to the demands of Ransomware blackmailers is that the payment of the ransom is not a guarantee for the recovery of the locked data. As you can imagine, the people behind viruses the likes of Qmak are dishonest cybercriminals and they do not care whether your files become accessible again. What this means is that they may or may not provide you with the needed decryption key, yet any money you may send them would be gone for good regardless of whether you get to regain access to your encrypted files. And while the alternative methods that you could also turn out to be ineffective, it’s still better to try them first before considering the ransom payment.
Plz help for .QMAK file decryption key online
Hi tayeb,
if it is an online encryption, then decryption is impossible.