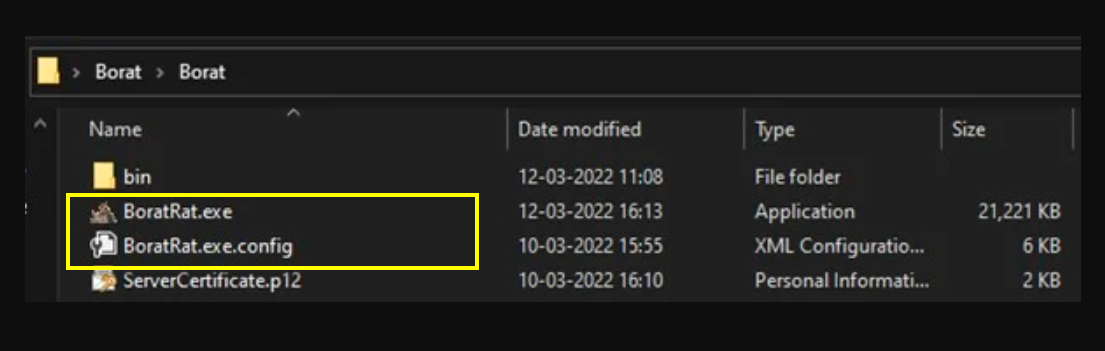
Borat RAT
Borat RAT is one of the infamous Trojan viruses. Borat RAT a type of PC virus that is highly versatile and can have many different purposes. This particular characteristic makes the malicious programs in this software category so dangerous.
Two really important things that need to be factored in regarding Trojans is that they can get distributed in a number of stealthy ways and also that they could be used to complete a big variety of criminal tasks.
Common sources of this kind of malware
The hazardous online threats like Borat RAT are really stealthy since they could be lurking almost everywhere in the online world. Torrents, spam emails with malicious attachments and also shady and illegal web platforms are among the most common hiding places for such forms of malware. To top it all, hackers could be able to add those viruses to seemingly harmless advertisements that might trick you into downloading the malware.
Regardless of what the used method for distribution is, the infection normally occurs with no visible symptoms. Once your machine has been attacked by such a virus, it could be utilized for many various illegal and harmful purposes.
Possible manners of exploiting a virus such as Borat RAT
One way in which most Trojan versions may damage your device is by destroying something stored on it. It might be personal or work-related data and it could also be some system files that are essential to the normal functioning of your machine. Another potential use may be the malware-backdooring function that a lot of Trojans may also have.
Most of these viruses could be used as a means for distributing different kinds of malware. Typically, what they most commonly spread is a version of ransomware. The aim of the Trojan in such a case is to review your computer system and search for any existing system or program weaknesses. Vulnerability, for example, could be a program that is not updated. If such a vulnerability is detected, the ransomware would be able to infiltrate your device and from then on it will likely try to encrypt your files or lock your screen.
Another one of the many purposes of Borat RAT and Bloom.exe may be to function as a personal data extractor, meaning that your bank account credentials, social-media accounts as well as everything you have online about you might be endangered. Cyber scammers make use of such malware to take advantage of your private info by making copies of it, taking over your machine in a stealthy way, or to stalk on you during the whole day using your own webcam and mic.
Some online terrorists may use such a dangerous programs since they want to benefit from YOUR OWN SYSTEM RESOURCES for some sort of illegal purposes. This kind of viruses might turn your PC into a bot and therefore – use it to mine for cryptocurrencies using your infected computer.
Prevention is essential
Unfortunately, it’s difficult to say what a virus like Borat RAT will try to do in each separate case due to the versatility of most viruses of its class. Its nature is really versatile and this is one of the basic reasons why, if you realize such an infection is going on inside your machine, you need to remove it as soon as possible.
The actual removal could be achieved on the condition you make sure you follow the instructions we have shared for you inside the removal guide down in this article. Also, it is likely that you are going to need to purchase a piece of special software, or to get your antivirus program updated in order to handle such threats in a successful way.
Also, ensure that you never go to web locations that may be unreliable, illegal and may hold questionable content. Another aspect of an efficient prevention process is to make sure you avoid all the emails and attachments you receive and cannot recognize.
SUMMARY:
| Name | Borat RAT |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | No visible ones which makes this threat quite horrible. |
| Distribution Method | Sadly, all types of web content can be potentially dangerous – torrents, fake ads, spam emails, etc. |
| Detection Tool |
Remove Borat RAT
If you are looking for a way to remove Borat RAT you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Borat RAT and any other unfamiliar programs.
- Uninstall Borat RAT as well as other suspicious programs.
Note that this might not get rid of Borat RAT completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment