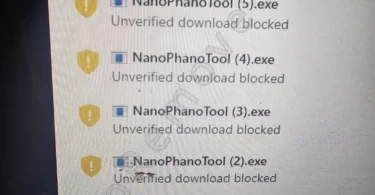
NanoPhanoTool is a piece of malware that forces its way onto your computer and doesn’t play fair. It often slips in through redirects on sketchy streaming sites, the kind that promise free movies but deliver headaches instead. I’ve seen...
Category - Trojan
What is a Trojan?
A Trojan horse virus is a type of malicious code that uses deception in order to trick users into allowing it on their computers. The name is derived from the Ancient Greek tale, in which a wooden horse was allowed into the besieged city of Troy under the guise of a trophy. But as it turned out, the horse was actually filled with enemy warriors who ended up capturing and destroying the city.

The Trojan Horse Virus
So, the comparison here is that Trojan viruses pretend to be something they’re not. And once they have entered their victim’s system, they are free to execute their true purpose.
Now as to what that may be, the possibilities are numerous. Trojan horse viruses are incredibly versatile and can be programmed for a wide range of different malicious tasks. We will cover these in a little more detail further on in this post, but a brief list of what they are capable of includes theft, spying, data corruption and performance disruption.
Aside from their versatility, Trojans are also known for being rather difficult to detect as they rarely have any symptoms. And although we do call this malware type ‘viruses’, that is a misnomer and it’s good to know that Trojans aren’t actually the same thing as regular viruses. One important distinction between the two is that unlike regular viruses, Trojans cannot self-replicate.
How does a Trojan infect you?
The answer to this question is in the name of the malicious code we’re discussing. Namely, Trojans will use a variety of disguises in order to deceive you into trusting them and installing them in your system.
For example, a Trojan horse may pose as a legitimate software application available for download on some questionable (or even illegal) website. And once you give your permission and run the executable file on your computer, it is free to perform whatever malicious task it was initially designed for.
Alternatively, and this is perhaps the more common scenario, you may receive a Trojan via email or some other messaging platform. In this case, the Trojan will be disguised as an attached file, or perhaps it may even be embedded in a link that you are asked to click on. In either instance, one click is usually all it takes to unleash the malware. If you have a message/file/link like this that you have suspicions about but aren’t entirely sure of, we have a free virus scanner that you can make use of.
What can a Trojan do?
This is where things get bizarre. Trojans are so unbelievably multifaceted, the mind boggles at the amount of potential havoc they can wreak on one’s system. Here is a list of possible usages that this malware category can be employed for, but it is by no means extensive.
- Destruction. Trojans can be programmed to downright corrupt files and even whole operating systems by formatting disks, deleting data, etc.
- Backdoor. A malicious piece of this types may be used to act as a ‘backdoor’ to your system for third parties to access it or for other malicious threats to enter (e.g. ransomware).
- Remote access. In this case, the Trojan will provide its creators with remote access to your computer and allows them to gain complete control over it.
- Banking. There are Trojans designed specifically to steal financial information from the infected computers.
- DDoS. Trojans can also be used to launch DDoS attacks in order to take down certain networks. In this case the malware will send multiple requests to the targeted web address from your computer.
- Spying. Trojan horses can very often also be used for the purpose of spying on you and/or the way you use your computer. For instance, it can take screenshots, make a list of the active applications or even log your keystrokes.
How to remove a Trojan?
As pointed out, Trojans are quite notorious for their ability to hide very well in the infected system. Some may even mimic system processes or files in order to avoid detection. So locating a Trojan in your system is by no means an easy task and is best done with the help of a professional malware scanner, such as the one you can download here.
Please feel free to search the removal guides we have developed if you know the specific Trojan that has infected you as well. They contain instructions on how to locate and delete the malware manually.
How to Remove X-essentiApp.exe
X-essentiApp.exe is a malware file that gets automatically downloaded from sites that feature a lot of unsafe ads, pop-ups, and redirects. Most of the affected users report getting this file from non-official movie/TV show-streaming sites. A lot of...
How to Remove Watchdog
Watchdog is a malware program that installs on the computer through file bundling. The virus is usually found in game hacking apps, cracked games, and other questionable or illegally distributed software. It’s also possible to get this malware...
How to Remove PCAppStore
PCAppStore is a common type of malware that has been bothering users for quite some time now. It’s been around for years and yet people today are still struggling with removing it from their PCs. I’ve researched this threat several times...
How to Remove Expiro
Expiro is a malicious piece of software, similar to Weather Zero and Nwjs, that can use a variety of distribution vectors to infect your PC. It can be included in pirated software, automatically downloaded onto your PC when you visit a harmful site...
How to Remove Altrisk
Altrisk is a Trojan Horse malware with a primary function to use up your system resources (CPU, Memory) for the mining of cryptocurrency. It does this without your knowledge or permission and will often lead to significant system slowdowns that make...
How to Remove the Altrsik Virus
Altrsik appears to be the latest iteration from a widespread family of Trojan Horse threats disguised as regular apps. It’s similar to other malware programs like Altisik and Altruistics and works pretty much in the same way. It drains your...
How to Remove Nwjs
Nwjs (Nwjs.exe) is the name of a group of Trojan Horse malware processes that start automatically and run in the background without user permission. The Trojan’s purpose could differ from one instance to the other. Some of the more common...
What Is W32.AIDetectMalware?
W32.AIDetectMalware is one of the most common Trojan Horse detections nowadays, together with Malicious.moderate.ml.score and Malicious.high.ml.score, which leads many people to believe that this is simply a false positive and not a real threat. In...
How to Remove Weather Zero
Weather Zero is one of those unwanted apps that try to present themselves as something legitimate and helpful, but their true nature is so thinly veiled that it immediately becomes clear you are dealing with malware. To be fair, this app isn’t...