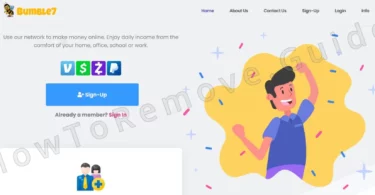
One recent scam scheme I just came across is a site called Bumble7.com. I’ve seen similar sites before so I immediately noticed that something was off about it. At first, it appears to provide an opportunity for earning some extra income that...
Category - Tips
This category covers the “Tips” section of HowToRemove.Guide. Our team mainly focuses on our users’ questions about errors, general how to’s and other related issues not clearly defined as malware infections. Over time some of these questions were asked enough times that we felt the need to create specific pages to which we can refer concerned users.
Prominent examples include questions such as:
- What to do if your WiFi is not connecting on Windows 10 automatically and can that be caused by malware?
- How to use the basics of the Mac Automator to help with malware removal?
- How to protect your Mac from malware attacks?
- What is a Password Manager and do you need one?
If you are someone interested to ask such questions, please search this category first and if you can’t find anything answering your query, head on to our Contact page or to the comments section of the post you first encountered on our website.
The XELUREX Bitcoin Scam – Report
Investing in cryptocurrency is a valid way to earn money but it requires knowledge and experience that most people lack. Despite this, too many online users have this false idea that getting into crypto will quickly get them enormous profits at...
Zoprax.com Scam Report
Here’s the latest crypto scam of the week – Zoprax.com. Despite this going on for years, cryptocurrencies continue to be a rampant playground and safe haven for fraudsters, who continue to increase complexity in their schemes and methods...
“Apple Approval Notice” Scam Report
Cybercriminals thrive on unsuspecting users – it’s been this way literally for decades, just with ever more elaborate schemes as technologies evolve and encompass our everyday lives. Case in point: the “Apple Approval Notice” is a...
Apple Pay Pre-Authorization Scam Report
There appears to be an ongoing trend with online scams that leverage the trust people have in the Apple brand and use it to deceive less experienced users. The latest of these scams is Apple Pay Pre-Authorization – a fraudulent scheme that...
The Ilroads Text Scam – Report
A common type of online/text scam is when you are sent a message that informs you that you’ve been charged a fee for a service you may or may not have used. In either case, seeing the message gets a lot of people worried and gets them to react...
The Zorunax Bitcoin Scam – Report
Zorunax is a type of online scam that is both one of the most widespread and also one of the easiest to avoid. Yet, millions of users still fall for such fraudulent sites and there are several reasons for this that will be explained below. For now...
The Cevonax Scam – Report
If you saw a post on social media (Instagram, TikTok, Twitter/X, etc.) that promised you a bunch of free money in Bitcoin if you visit a site called Cevonax, I warn you not to engage with that offer or interact with the linked site. The Cevonax.com...
The Zelunor Bitcoin Scam – Report
One of the most important skills to have in order to stay safe on the Internet is the ability to recognize (and stay away from) online scams. They are everywhere, come in all shapes and forms, and constantly evolve their tactics and deception...
The Saedex Scam – Report
If you are someome who isn’t every experienced with cryptocurrency, coming across an online offer from a site such as Saedex.com might seem like a great and rare opportunity to make a bunch of money quickly and without investing much time or...