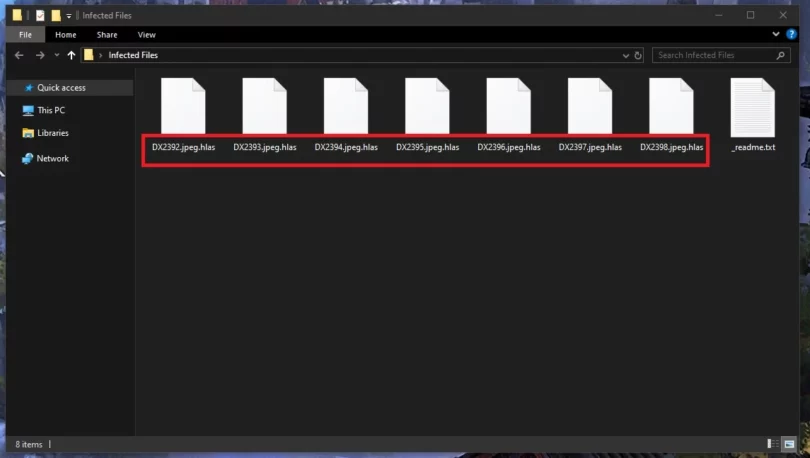
.Hlas is the latest virus in the DJVU family of ransomware, which is the prevalent strain that targets consumers in the last several years. Unlike other ransomwares, DJVU (the .Hlas file extension) explicitly doesn’t target enterprises. Instead it is the most reliable method for criminals to...
Category - Ransomware
What is a ransomware?
Ransomware have become the new plague of the internet and their numbers have been growing at an alarming rate. But what are they actually and what makes them different from any other type of malicious code out there?

Ransomware is a type of malware that infects people’s devices (there’s ransomware for every OS in existence) and attempts to block access to some components of said devices. For example, this can be the screen of the device, which essentially prevents users from being able to access anything on it. But more often than not, ransomware tends to target a wide range of file types and applies encryption to them in order to prevent anyone from being able to open or use those files.
Once all is said and done, the Ransomware, or rather the hackers behind it, will proceed to blackmail their victims for money. In essence, they demand to be paid ransom for the victims’ access to whatever component they are locked out of. That is how ransomware gets its name.
In recent years ransomware have gained such momentum that their numbers are growing exponentially. In fact, according to some estimates, by 2021 ransomware attacks may cost companies and organizations on a global scale in the region of $20 billion!
Therefore, being adequately prepared for this type of malware is just as important as being able to handle the aftermath of an attack that has already taken place. So in the next few lines we would like to emphasize on what users can do to protect their systems and files from potential ransomware infections.
How does a ransomware infect you?
Ransomware viruses can be distributed using a number of techniques. Some of the most common include infected social media messages and spam emails, along with malicious online ads (aka malvertisements).
The latter are easiest to protect yourself from in that all you need to do is avoid interacting with any online ads. There’s simply no way you would be able to tell if a certain banner or box message has been embedded with a virus just by looking at it. So with that in mind, the only sensible thing to do is steer clear of all online advertisements altogether.
As for emails and other such messaging transmitters, these can be a little bit trickier to navigate as you can’t just avoid any and all electronic correspondence. But the telltale signs of a phishing scheme are usually apparent when you know what to look out for. Namely, be on the watch for attachments and/or links that the body of the message is trying to persuade you to click on under whatever pretext. These are usually where the virus is embedded. Or alternatively, they may contain a Trojan that is used as a backdoor and downloads the ransomware afterwards.
But if you happen to have second thoughts about a given attachment or just any file really, you can always run it through our free virus scanner to make sure it isn’t a threat.
How can you protect yourself against ransomware?
Avoiding the potential sources of ransomware is of course a great thing. But there can still be loopholes in your system’s security that viruses can potentially exploit and use to get inside. So that’s not exactly a foolproof solution that would shield you from the effects of a hypothetical attack of this type.
What we recommend as a sort of ‘insurance’ in case of a ransomware infection is regularly creating backups of your most valuable data. If there is certain information on your computer that you know you can’t afford to lose, then be sure to have copies of it stored someplace safe. For example, an external drive that isn’t constantly connected to a computer and therefore the internet is a really good option. Another one, if this doesn’t work for you, is storing your backups on a cloud, although some experts argue that these aren’t always 100% safe either.
But the idea is that even in case you do happen to land a ransomware virus on your machine, the blackmailers won’t have any leverage to use against you and all you will need to do is simply remove the virus and carry on with your life.
How to remove ransomware?
Removing ransomware from your machine is about as tricky as malware removal can get. There are many risks involved, including even the risk of permanently damaging your computer if you aren’t careful. And on top of that, the process can take up to several hours, so it’s not something you should take lightly.
On our site, we offer manual removal guides for users who are willing to undertake this process on their own. But we also have a special malware removal tool (available for download here) that is certain to detect the malware and thoroughly clean your system of it in a matter of minutes. So both options are available here, it’s just a matter of what you prefer.
How to Decrypt Magniber Files
Magniber Ransomware is one of the few remaining ransomware strains that target end-users and are unrelated to DJVU. In the case of Magniber, the virus is a successor to the Cerber ransomware. Generally, it can been seen as an iteration of the same thing, but unlike Cerber and DJVU threats like ...
How to Remove and Decrypt the .Watz Virus Files
The Watz ransomware is one of the most commonly encountered interactions of the STOP/Djvu ransomware family, similar to .Waqa and .Qual. If this malware has attacked you and your files now have the .watz extension, then this guide is for you. We’ll attempt to help you delete the virus and...
How to Remove and Decrypt the .Qual Virus Files
This page was created to help victims of the latest Djvu family ransomware variant, called .Qual. This is not an official name, only the suffix of the files that the victims see and search for on the internet, just like with the .Watz and .Waqa ransomware threats. All Djvu variants have worked in...