Haron
Haron is a virus that belongs to the file-encrypting Ransomware category – a type of computer threats that can lock user files using advanced data-encryption. The files Haron encrypts remain inaccessible even after the virus is removed and no regular software can open them.
If a Ransomware has attacked you and locked your files in order to extort money from you, you need to be informed about the potential courses of action you can now take so as to ameliorate this problem and fix things to the best of your abilities. Before we get any further, there is a disclaimer we must make:
Although there are specialized decryptor tools that can unlock the encryption used by some Ransomware versions, most Ransomware viruses do not currently have decryptor tools that correspond to the encryption used by them. Unfortunately, without a backup of your files and/or a decryptor tool that corresponds to the virus that has attacked you, there can be no guarantee with regard to the recovery of your data. We will do our best to help you bring some of your files back but we simply cannot make any promises as to how effective our suggestions would be in your case.
Now that we’ve gotten this out of the way, let us tell you a bit more about the virus you are currently faced with.
The Haron ransomware
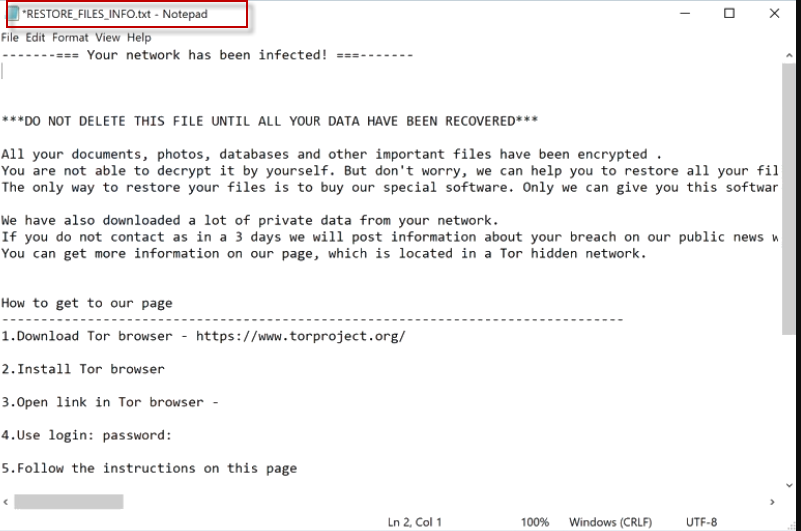
The Haron ransomware is a malware program that can infect any Windows computer and encryption-lock the user files present in it. The Haron ransomware displays a message on the infected machine which tells the victim that a ransom must be paid to free the files.
There are two main reasons why an attack from Ransomware can be so devastating. The first one is that the encryption these viruses apply goes unnoticed in most cases. The majority of antivirus programs aren’t suited to detect Ransomware encryption like Haron or Aeur and usually fail to notify the user about what’s going on in their computer, which, in turn, allows the Ransomware to fully lock-up all of the files that it has targeted.
The second reason has to do with the nature of the applied encryption and the fact that it won’t go away even after the Ransomware is removed. We can help you remove the Haron ransomware (and we advise you to do exactly that) but you must know that this won’t automatically set your data free.
The Haron file extension
The Haron file extension is a special sequence of symbols that is added in the place of the regular extensions of the files targeted by the virus. Manually removing the Haron file extension doesn’t work – only decrypting the files will make it go away.
Paying the ransom that the hackers require from you isn’t a very wise course of action because there’s a chance that this may make things worse for you. What we mean by that is the hackers may simply deny you the decryption key you’ve paid them for, leaving you with no way to release your data. Therefore, we strongly suggest you first try the guide below before you consider opting for the ransom payment.
SUMMARY:
| Name | Haron |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | There are very few symptoms that a Ransomware may show, and most of them are almost unnoticeable. |
| Distribution Method | Ransomware mostly gets distributed through the use of spam letters, and misleading ads. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Haron Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Haron files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply