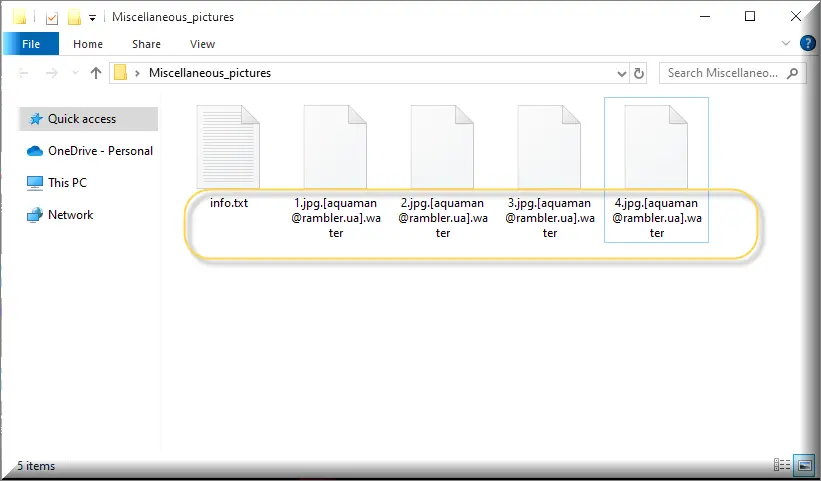
.Water
.Water is a virus, member of the Phobos Ransomware family, which prevents users from access to the files they store on their computer. Through searching the hard drive of the infected device, .Water creates a list of files that are considered of great value and then encrypts them all so that a ransom can be demanded for their decryption.The .Water virus normally sneaks inside your PC without showing you any signs and without your knowledge. This Ransomware then starts to encrypt the files it considers to be the most important for you. Then, a message that appears on your monitor informs you that a ransom payment is requested to decrypt the encrypted files.
Generally speaking, if we have to describe the term “ransomware”, it is used for software that is able to do something to your computer, and then demand a ransom to reverse it. There are various types of ransom-demanding threats such as screen-locking ransomware and mobile ransomware, but the file-encrypting one is probably the most popular and the most difficult to remove and deal with.
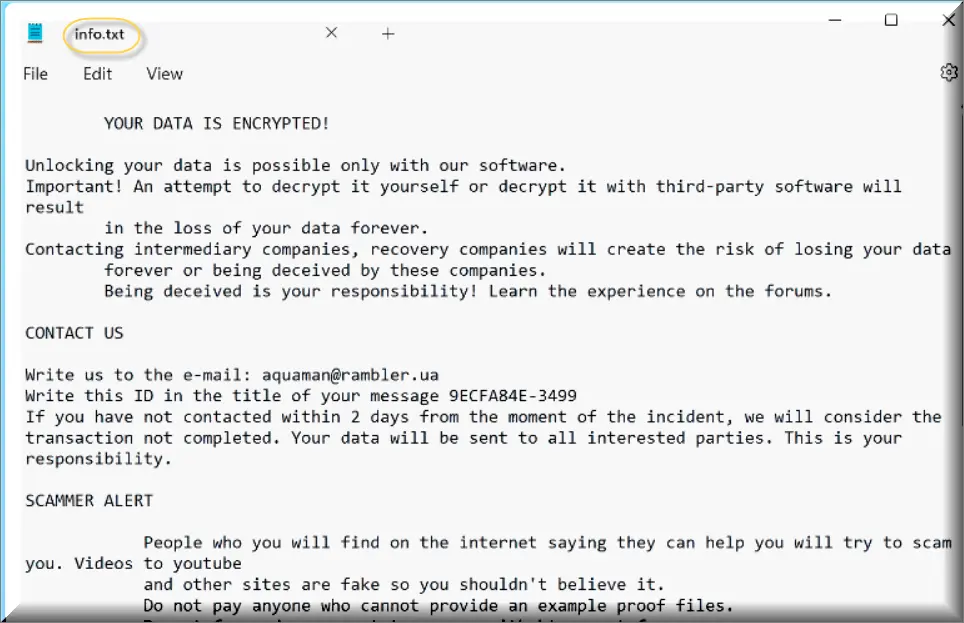
Text in this ransom note and the “info.txt” file:
YOUR DATA IS ENCRYPTED!
Unlocking your data is possible only with our software.
Important! An attempt to decrypt it yourself or decrypt it with third-party software will result in the loss of your data forever.
Contacting intermediary companies, recovery companies will create the risk of losing your data forever or being deceived by these companies. Being deceived is your responsibility! Learn the experience on the forums.
CONTACT US
Write us to the e-mail: [email protected]
Write this ID in the title of your message –
If you have not contacted within 2 days from the moment of the incident, we will consider the transaction not completed. Your data will be sent to all interested parties. This is your responsibility.
SCAMMER ALERT
People who you will find on the internet saying they can help you will try to scam you. Videos to youtube and other sites are fake so you shouldn’t believe it. Do not pay anyone who cannot provide an example proof files. Do not forward a payment to anyone with btc apart from us. You can get your exemplary proof file for free by contacting us with your company email.
Not a single file will be sent to any other email except the company one (This is a precaution in order to for you to not get scammed) Contacting any other third party or data rescue companies will create the risk of losing your data forever or you getting scammed by these firms. Getting scammed or not is up to you. Learn about the experiences of other people on the forums.
ATTENTION!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
If you have not contacted within 2 days from the moment of the incident, we will consider the transaction not completed. Your data will be sent to all interested parties. This is your responsibility.
Don’t be afraid to contact us. Remember, this is the only way to recover your data.
.Water is a typical representative of the file-encrypting ransomware type. What a virus such as this one can do is it can sneak inside the machine, typically using a Trojan horse virus or some malicious component that the users have clicked on. It then checks the most commonly accessed data on all your hard drives. After that, the ransomware is ready to apply its encryption. Typically, you will receive a huge alert after the file encryption process is complete, and that alert will consist of a number of extra alerts from the hackers, ransom payment instructions and a deadline, after which the recovery of your files may not be possible.
The .Water virus
The .Water virus is a ransomware infection that is designed to generate income for its criminal creators through ruthless money extortion. What the .Water virus usually does to perform its agenda is it encrypts a variety of user files without the knowledge of the victims and then blackmails them to pay a ransom.
There may be many different ways to spread Ransomware. The malvertising method is probably the most popular one where the harmful ransomware virus can be spread through fake ads and legitimate-looking offers. You can get infected instantly by clicking on such an ad, but sadly, due to the fact that the ransomware operates without visible symptoms, you may not have a clue about the contamination. Threats like .Water could also be distributed via emails, along with a Trojan horse, or inside malicious attachments. You will automatically get the virus in them immediately after you download such an infected attachment or load a malicious file. Of course, there are other sources such as infected web pages, and platforms that stream videos and audios or distribute shareware.
The .Water file encryption
The .Water file encryption is a very malicious method that cyber criminals use to take user data hostage. The .Water file encryption is basically a process that converts a list of target user files into bits of data that cannot be opened or used in any way.
Nothing can guarantee that the encrypted files will ever be restored no matter what you do. That’s why, regardless of what you choose to do, your information will be at risk. That is why we warn you not to rush with the ransom payment immediately after the disclosure of the contamination. Seek first some other methods that can help you remove .Water and eventually save some of your files for free. Consult a person with experience in dealing with these issues, purchase a specialized program to decrypt your blocked data or try the manual instructions in the removal guide below.
SUMMARY:
| Name | .Water |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool | Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove .Water Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt .Water files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply