
*Source of claim SH can remove it.
Ransomware continues to evolve, posing significant threats to individuals and organizations worldwide. One such threat, BlackBit ransomware, has emerged as a variant based on the notorious Loki Locker ransomware, demanding attention for its unique characteristics and the challenges it presents in data recovery and system restoration. This guide aims to shed light on BlackBit ransomware, its operation, and effective measures for its removal, ensuring your digital safety and data integrity.
What is BlackBit Ransomware?
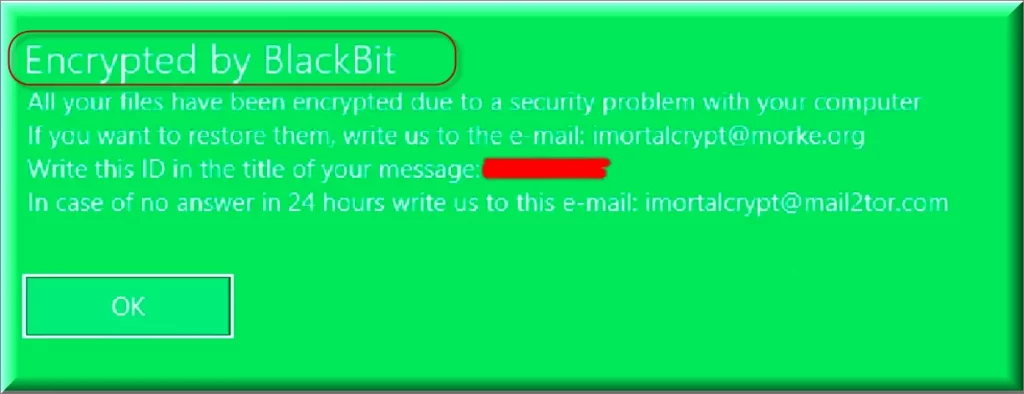
BlackBit ransomware is a malicious software variant derived from the infamous Loki Locker ransomware. First discovered in September 2022, BlackBit has quickly gained notoriety for its encryption tactics and the demands it places on its victims.
Key Characteristics:
- Origin: Variant of Loki Locker ransomware.
- Discovery Date: September 2022.
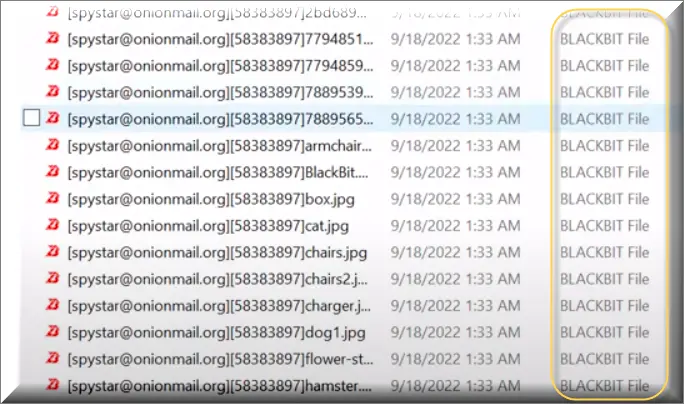
- Encryption Marker: Appends the “.BlackBit” extension to filenames, along with the victim’s ID and the [email protected] email address.
- Ransom Note: Delivers a note named “Restore-My-Files.txt”, providing instructions for contact and payment.
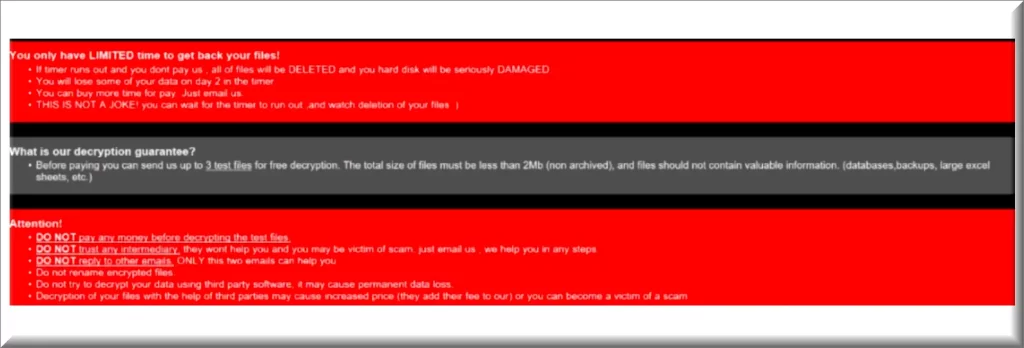
Text in this ransom note and the “Restore-My-Files.txt” file:
BLACK BIT
All your files have been encrypted by BLACKBIT!
29d,23:45:51 LEFT TO LOSE ALL OF YOUR FILES
All your files have been encrypted due to a security problem with your PC.
If you want to restore them, please send an email [email protected]You have to pay for decryption in Bitcoin. The price depends on how fast you contact us.
After payment we will send you the decryption tool.
You have to 48 hours(2 Days) To contact or paying us After that, you have to Pay Double.
In case of no answer in 24 hours (1 Day) write to this email [email protected]
Your unique ID is : –
You only have LIMITED time to get back your files!
•If timer runs out and you dont pay us , all of files will be DELETED and you hard disk will be seriously DAMAGED.
•You will lose some of your data on day 2 in the timer.
•You can buy more time for pay. Just email us.
•THIS IS NOT A JOKE! you can wait for the timer to run out ,and watch deletion of your files 🙂
What is our decryption guarantee?
•Before paying you can send us up to 3 test files for free decryption. The total size of files must be less than 2Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
Attention!
•DO NOT pay any money before decrypting the test files.
•DO NOT trust any intermediary. they wont help you and you may be victim of scam. just email us , we help you in any steps.
•DO NOT reply to other emails. ONLY this two emails can help you.
•Do not rename encrypted files.
•Do not try to decrypt your data using third party software, it may cause permanent data loss.
•Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
How BlackBit Operates
Upon successful infiltration, BlackBit encrypts the files on the affected system, making them inaccessible to the user. It distinguishes itself with a dual notification approach:
- Ransom Note: A text file, “Restore-My-Files.txt”, is dropped within the encrypted directories. This note contains detailed instructions for the victim, urging them to establish contact with the ransomware operators using the provided system ID for identification purposes.
- File Naming Convention: BlackBit uniquely modifies filenames by prepending the contact email ([email protected]) and the victim’s ID, followed by appending the “.BlackBit” extension, making the encryption readily identifiable.
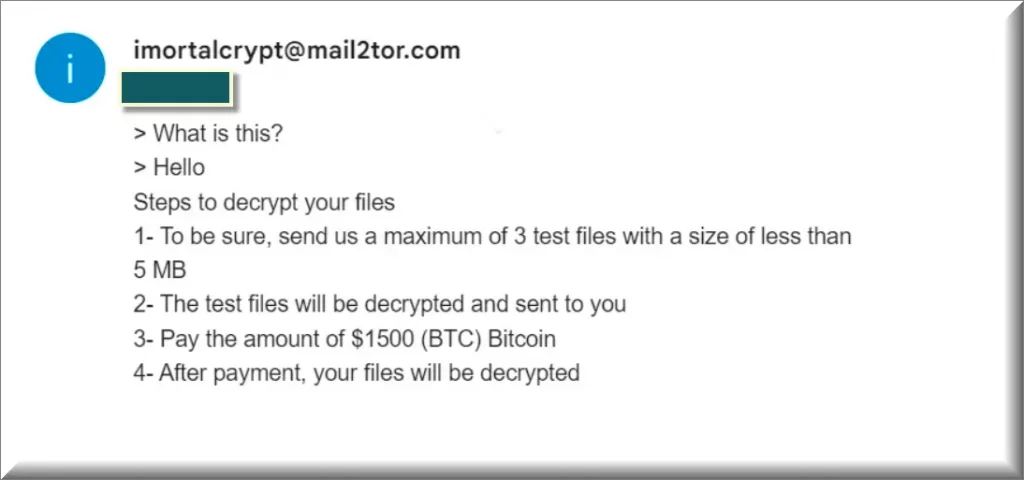
Victims are instructed to contact the attackers through various means, including email addresses ([email protected], [email protected], [email protected], [email protected]) or via Telegram (@Spystar_Support). A critical note is the urgency imposed by the attackers, demanding contact within 48 hours to avoid a ransom increase to twice the original amount.
Preventive Measures:
- Regularly update software and operating systems to patch vulnerabilities.
- Educate users on phishing and other common attack vectors.
- Implement regular backup protocols, ensuring data is stored in multiple, secure locations.
Conclusion
BlackBit ransomware, with its roots in the Loki Locker variant, presents a formidable challenge due to its encryption tactics and ransom demands. Understanding its operation and implementing a comprehensive removal and recovery strategy are crucial steps toward mitigating its impact. By following best practices for digital hygiene and security, individuals and organizations can enhance their resilience against such malicious threats.
SUMMARY:
| Name | BlackBit |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
We tested that SpyHunter successfully removes BlackBit* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and BlackBit may reinstall itself at the end if you don’t delete its core files. |
*Source of claim SH can remove it.
Remove BlackBit Ransomware
Removing BlackBit ransomware and recovering encrypted files involves a multi-step approach, focusing on both eliminating the malware and attempting to restore data without succumbing to the attackers’ demands.
Immediate Actions:
- Isolate the Infected System: Prevent the spread of ransomware by disconnecting the affected device from the network.
- Identify the Ransomware: Confirm the presence of BlackBit through its unique identifiers mentioned above.

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt BlackBit files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply