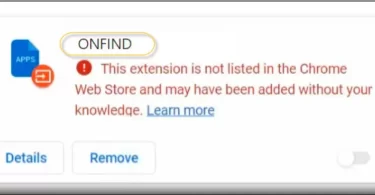
What is ONFIND? ONFIND is a new browser extension that reroutes the users’ web browsing results to Boyu.com.tr. This piece of software, which we recently discovered, functions as a browser hijacker, diverting all queries from default search...
Category - Browser Hijacker
What is a browser hijacker?
A browser hijacker is a software initiating browser redirects to select websites and landing pages without the user’s consent. Browser redirects are called as such because of the effect they have on the browsers they embeds themselves in. Namely, software applications that belong to this particular category have the capacity to take over the browser by overriding the user’s configurations of it and installing their own. Ecamples of this include setting a new homepage, changing the default search engine, and at times even introducing a new toolbar to the browser’s interface.
In addition to the above, these programs trigger something we call page redirects, which is where the term ‘browser redirect’ originates from. Page redirects, in turn, are the instance in which your browsing program automatically loads a new URL in your current tab or just spontaneously opens a new one to load said URL.
Browser hijackers are very often associated with computer viruses, although it is factually incorrect to use these terms interchangeably. Browser redirects or hijackers are actually not malicious and they don’t have the qualities necessary to inflict any real harm on the infected computer – much unlike viruses.
Instead, it would be more accurate to refer to these programs as potentially unwanted or PUP’s. This is because despite their relative harmlessness, there are a number of issues related to them that make them an undesirable presence in one’s OS. And we would like to elaborate on those issues further down in this article.
How does a browser hijacker infect you?
In most instances of first seeing such an application on their machine, infected users will have no idea where it came from. And that is because the developers of this type of software rely on stealth tactics in order to have it successfully distributed, most commonly software bundling. As part of it, the developer will usually include the browser hijacker in the setup of another program (typically some free system optimization tool or similar piece of programming). The hijacker will be included as an optional install, meaning that users would normally have the opportunity to leave the hijacker out of the installation process.
However, if the user were to select the default installation settings of said optimization tool, which tends to most often be the case, then the added component (in this scenario, the browser hijacker) will automatically be installed as well. The only catch is that this information is generally withheld from the end user and they come to find out about it already post factum.
What can a browser hijacker do?
Browser hijackers generally serve one purpose: generating paid ads. These are advertising tools in a sense and their creators earn money from clicks on the advertisements that they showcase on users’ screens during their browsing sessions.
With that in mind, again you can see that they don’t have any malicious intentions. The problems arise in the practices that these software products are often involved in, in order to maximize their profits from said clicks.
Namely, hijackers will very often be engaged in collecting data from your web browser so as to optimize their online ads and tailor them to each individual user. This is rarely made known to the user in question (just like the installation process itself), and there are also a lot of questions that arise as to how the gathered information can be utilized aside from just the target ads.
In addition, as you might have guessed it already, browser hijackers expose users to vast quantities of unwanted web locations. Either way, among the numerous sites and pages that browser redirects can link to, there can be those that are unsafe and may potentially lead to malware infections, including higher-class malware like Trojans or ransomware.
How do you remove a browser hijacker?
Anyone who has ever had a browser hijacker on their computer knows that removing them is trickier than uninstalling regular programs, because the developers deliberately avoid including an obvious uninstallation option. So as a result, users are forced to figure out how and where to locate all the components of the hijacker that has ended up nestled in their system. And if you happen to miss one – that residual part of the software can oftentimes be enough for it to end up reinstalling itself in the computer, which can be highly frustrating, not to mention suspicious.
Thus, in order to effectively get rid of hijackers, it’s a good idea to have some professional malware removal tool scan your computer. Alternatively, there are special removal guides available for specific browser hijackers. In fact, if you can pinpoint the exact variant that has infected your system, then chances are we might have a guide created for it already, which is what this category is dedicated to.
Roun.co.in Browser Hijacker – Virus Removal Instructions
Is Roun.co.in a dangerous website? Roun.co.in is a website that has been categorized as dangerous by several sources. Our research shows that it has a very low trust score due to a number of reasons. The main red flag is that the owner of the Roun...
How to remove Nhereugo.com from browsers
What is Nhereugo.com? Nhereugo.com is a search engine promoted by browser hijackers – that’s what we call a software that enforces new settings in your browser without your consent. We cannot definitively rule that Nhereugo.com is...
Eliminating the Zakolata Virus from your computer
What is Zakolata and can it do harm? Zakolata is a software that is considered as potentially unwanted, and falls under the category of browser hijackers. Though it rarely does any harm to the system, this type of software is very intrusive and...
Removal instructions for the Guardian Angel application
*Source of claim SH can remove it. Is Guardian Angel a dangerous software? Guardian Angel falls in the category of potentially unwanted software that is commonly referred to as a browser hijacker. This kind of software is very intrusive and gets...
How to remove Web Bear Search and Webbearsearch.com from browsers
Web Bear Search No matter how advanced operating systems and security tools become, it appears that annoying forms of malware and scamware like Web Bear Search will always find their ways inside users’ browsers. This particular example is what...
Removal instructions for the Explore Spot extension
Explore Spot Ads flooding your browser, redirects to unknown sites, and a new homepage with the name Explore Spot that has replaced your previous one? If any of these annoyances sound familiar, then you are likely dealing with an unwanted piece of...
Removal instructions for the Weebseeker Chrome extension
What kind of software is Weebseeker? Weebseeker begins interfering with your web browsing preferences as soon as it is installed on the system, therefore it can be described as a browser hijacker. This type of software modifies your homepage or...
Removal instructions for the SerachMates browser extension
What is SerachMates, and what can it do? SerachMates is as a browser hijacker that starts tampering with your browsing options the moment it is installed. It forces your browser to display a few pre-selected URLs and changes your homepage or default...
Removal instructions for the NymphMiniica browser extension
What is NymphMiniica, and what can it do to my PC? In its core, NymphMiniica is a software that can be described as a very aggressive tool. In other words, it is a browser hijacker that starts to interrupt with your browsing settings right after...