Cse.google.com
Cse.google.com is neither a virus, nor it is malicious. However, it is possible that you have encountered a compromised version. An important note that must be made when talking about Cse.google.com is that it is not categorized as a virus. That program is unwanted and irritating, but it is not actually malicious.
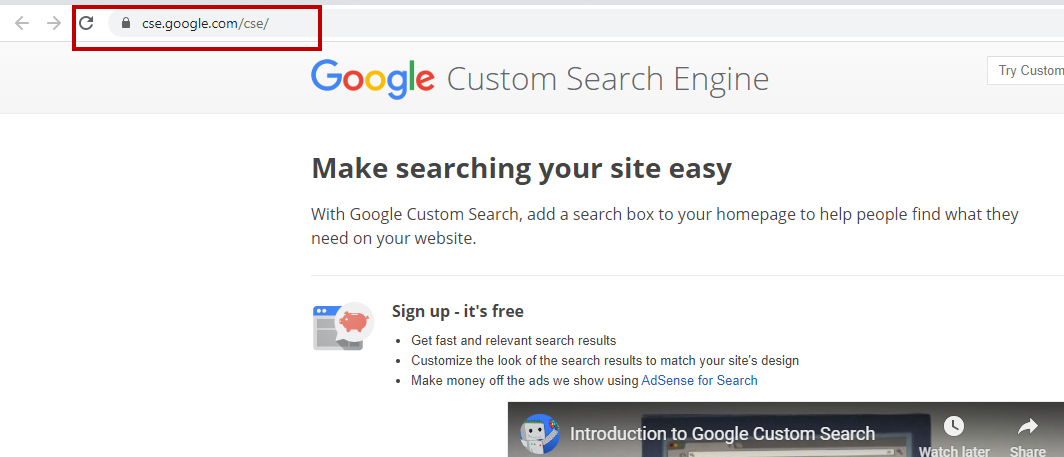
Internet criminals use Cse.google.com to generate revenue from each search you perform.
Landing a Browser Hijacker is probably one of the most annoying and frustrating things that can happen to a person who regularly uses their browser and let’s be honest, most people do use their browsers on a regular basis. After all, this is how we utilize our connection to the internet. Therefore, having your Firefox, Chrome, IE’s homepage and default search engine changed along with other unwanted alterations can certainly frustrate even the calmest person.
If you have ended up on this article, chances are that you’ve already faced one of those irritating programs – Cse.google.com. This is one of the newest Browser Hijackers that roam the internet looking for their new victim and since many people have been complaining about it, we’ve created this article to help those users. We will provide you with a lot of essential information and tips that will both help you get a better understanding of what Browser Hijackers are and also how you can protect your PC from them in the future. Additionally, below the article, you will find a guide that can help you uninstall Cse.google.com and eliminate every last bit of it from your machine. Just make sure that you first read the rest of the actual article instead of rushing for the removal manual. After all, understanding how Browser Hijackers function is the key to dealing with them.
If the guide didn’t help you, download the anti-virus program we recommended or ask us in the comments for guidance!
Cse.google.com , for example, does not have the potential to damage your system or files on its own. Additionally, removing a Browser Hijacker is much easier than getting rid of a virus, like a Trojan or Ransomware. Many people panic once they realize that their PC has been invaded by a Browser Hijacker, but there’s really no need for that. As long as you remain careful, there’s hardly anything that the intrusive program could do to your computer. With all that being said, you should still keep in mind that Cse.google.com is unwanted and should be removed as soon as possible. Some Browser Hijackers might even be promoted as useful and beneficial to the user. In fact, they might even have some actual functionality. However, is that functionality really worth putting up with all the negative effects of the program? We, for one, don’t think so.
Why you need to be cautious
As we already mentioned, even though Browser Hijackers are usually regarded as safe, you still need to be careful around them. This is because there are quite a few questionable and sometimes even shady features that most of these programs possess. For example, Cse.google.com could try to keep an eye on your online activity, which on its own is a privacy invasion. This is usually done so as to help the program modify the adverts it displays in your browser. Yes, this is yet another unwanted trait of most Browser Hijackers – their tendency to display obstructive browser ads. Apart from that, those Hijackers, as mentioned earlier, might alter some of your browser settings like changing your search engine or homepage. Last, but not least, a Browser Hijacker could potentially redirect you to pages with questionable content that might turn out to be hazardous and possibly harmful. This is rather rare but is still something you should be on the lookout for.
Installation of Browser Hijackers
This last paragraph will teach you about the most common ways via which programs like Cse.google.com get installed on your PC. Being aware of the different methods of Browser Hijacker distribution is crucial if you want to make sure your PC does not get infected by such programs ever again. Some of the more frequently employed distribution strategies include the use of spam e-mails, deceptive links that serve to directly download the program on your PC and unreliable torrent files. Still, none of those seems to be as effective as the infamous file-bundling scheme. In this method, the hijacker is combined with some other programs that form the so-called file bundle. In most cases, users install these so that they could get a specific program and not all the added content. However, since most people tend to rush for the Quick installation setting, they unknowingly agree to the installation of the whole package. Still, since this is a perfectly legal method for spreading software, all you need to do in order to prevent the installation of any unwanted applications is to select the advanced installation menu. From there, you can customize the installation and leave out any add-ons that you might consider unwanted by simply unchecking them.
SUMMARY:
| Name | Cse.google.com |
| Type | Browser Hijacker |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove Cse.google.com
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone



Hi Aranya, these entries are not the problem. It appears cse made changes to your lan settings. Can you go and confirm that your DNS is OK? Check in the guide on how to do it.
Hi Ristiza,
you should delete these IPs.
thank you. it worked for me, found 5 unknown entities
You are most welcome Vipul. Remember we are here to help if you happen to find anything suspicious in your system.
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
127.0.0.1 down.baidu2016..com
127.0.0.1 123.sogou..com
127.0.0.1 http://www.czzsyzgm..com
127.0.0.1 http://www.czzsyzxl..com
127.0.0.1 union.baidu2019..com
Hi ankit,
you should delete these IPs.
I cant del8 them it requires admin permission
Have you made sure that you have logged in with an account that has Administrator rights? If the current account that you are using on your PC does not have admin rights, you won’t be able to delete the IP’s.
How do i delete those IPs???
Hi Kittu,
threat the file like a normal text document and just erase the IPs.
Hi Yannis,
did you try to restart your PC ? And try again ?
Hi WIN10_USER,
you should definitely remove these IPs.
127.0.0.1 down.baidu2016..com
127.0.0.1 123.sogou..com
127.0.0.1 http://www.czzsyzgm..com
127.0.0.1 http://www.czzsyzxl..com
127.0.0.1 union.baidu2019..com
Hi ashish,
you should delete these IPs.
how to delete??
Hi, Ashu, all you need to do is delete the suspicious IP’s as you would normally delete text in a regular text file. After doing so, you must save the changes you have just made to the hosts file by pressing Ctrl+S.
Hi, Saranghan, now you will have to delete those IP adresses and then save the changes to the hosts file.
No need for panic, simply delete the IP addresses as you would delete them on a regular text file. After that, click on File and then select Save to save the changes. However, know that you would need be logged in with an account that has Administrator rights in order to implement the changes in the hosts file.
127.0.0.1 down.baidu2016. com
127.0.0.1 123.sogou. com
127.0.0.1 http://www.czzsyzgm. com
127.0.0.1 http://www.czzsyzxl. com
127.0.0.1 union.baidu2019. com
Now, that you have found the intrusive IP addresses, delete them from the hosts file and save the changes.
127.0.0.1 down.baidu2016.com
127.0.0.1 123.sogou.com
127.0.0.1 http://www.czzsyzgm.com
127.0.0.1 http://www.czzsyzxl.com
127.0.0.1 union.baidu2019.com
Hello, Sripad. What you have to do now is delete those intrusive IP addresses and save the changes you’ve just made to the hosts file so that they could be implemented.
Hi, Harsh, were there suspicious any IP addresses in the hosts file under localhost (Step 3)? Also, did you uninstall anything as described in Step 2?
I did every possible step. But it still redirects to cse .google. com..please help..its really annoying..Thanks in advance
Hello, Rahul. Were there any suspicious IP’s in your host file under “localhost” when you checked (as instructed in Step 3)? Also, did you figure out the directory of the Hijacker by following the fila location from your Task Manager’s Processes tab (Step 5). A screenshot of your hosts file, installed programs (Step 2) and Processes tab posted here, in the comments, might help us get a better grasp of your situation.
https://uploads.disquscdn.com/images/9464a239a5abbe6718e48584e3d37f5c40c2dbad2b127bfc84915bf0a0d30021.jpg https://uploads.disquscdn.com/images/200246b038185f8634cdd802e225b8a2245bbde5e20be43c6312a22d54a9644a.jpg https://uploads.disquscdn.com/images/d049db53ab269ed957a477a8dde9584c434df132caf8fc2612836185e92ecf4b.jpg
Thank you for your reply sir.
I’ve attached the screenshots below.
Also when i go to the file location from the task manager then it just takes me to the chrome.exe file(where the chrome is installed) nowhere else..
also to mention i always get a popup blocker with some unkown site jok.something something. i doubt its that thing thats affecting. I cant acces that site though
awaiting reply
Thanks in advance.
Thanks for providing us with those screenshots. However, not all processes are visible so we cannot say if there is not some sort of an unwanted process lower on the list. Your hosts file seems to be okay. We took a look through your program installs . Most programs seem to be legit. So far the only exception appears to be Social2Search. Unless you remember installing this and you need it, we advise you to uninstall the program since it’s known to display online ads and behave as a typical Adware/Browser Hijacker software. Once you get rid of this, write to us in the comments to inform us if there were any results.
thanku for your prompt reply.
I have downloaded Spyhunter. The good news is i was able to remove the program that was causing the cse redirect. but the bad news is i ran a scan through spyhunter and found many other files that are infected, also my antivirus is not detecting any of them.
I want to know few things now sir.
1. do i need to do anything other then deleting the entire folder that was causing the cse stuff?
2. how do i remove the other malwares?
thank you
You should definetely delete the folder directory of cse. When it comes to the other files that have been detected, you have two options: You should either update your SpyHunter so that it has the automatic removal feature or you can manually delete all files that have been targeted as harmful/infected. Also, be careful with what you install, Browser Hijackers are often distributed via other software so you aways must be on your guard when installing new stuff.
We are glad to have succefully helped you resolve your issue, Rahul. Your gratitude means a lot to us!
Hi there, Ahdra, your job now is to delete those IP’s from your Hosts file and save the changes afterwards. Know that Administrator privileges are required in order to implement changes to that file.
Hi, alvin, can you send us a screenshot of that? This will help us determine what your situation is.
Can you give us a screenshot of the problem and if possible of the flashin cmd? Also, are there any steps from the guide that you did not complete? Did you search for the cse.google.com in your Registry Editor? Also, you can send us a screenshot of your Task Manager (the processes tab) and of your program installs from the Control Panel. You might have deleted suspicious apps but there could still be something that’s left so it’s better if we take a look.
Hi there, Sam. You must now delete those addresses and save the Hosts file afterwards. Administrator privileges are required in order to save the changes to that file.
whenever I try to delete those it says ‘access denied’ even after I’m logged in with by administrator account.
In this case, try the following: Open your Start Menu and type “%windir%/system32/Drivers/etc/hosts” . Right-click on the first result and select Run As Administrator. Now, try again deleting the IP’s and saving the file. Tell us in the comments if that worked.
Didnt work, please help me
Does the account you’re currently using on your PC has Administrator privileges?
Hello, I did all the steps, but in step 5, I do not know what all to uninstall. Could you guide?
Send us screenshots of all the processes there so we can determine which ones are potentially unwanted.
Your processes look okay so do not delete anything from there. Instead, go check your hosts file for any suspicious IP addresses as it is instructed in the guide above.
I have removed the IP addresses, still the problem persists
Did you complete the rest of the steps. The program that is causing the issue is probably still on your PC. Did you check the programs installed on your computer from the Control Panel for any suspicious entries (Step 2)?
Yes I did. The only thing I did not do was Step 5. I did not delete any process.
Were there any IP addresses below “Localhost” in the Hosts file?
Yes. I removed them as guided. Should I post a screenshot of the same?
Yes, and also, can you give us a screenshot of what programs you have on your PC (from the Control Panel) since there might be some shady program there, that is causing the issue.
Hello, Theodore. You should definitely remove those IP’s from the hosts file. Once you delete them, be sure to safe the changes to the file.
Make sure to remove all of them and then save the changes to the hosts file.
Hello again, Sushurt. Everything seems to be in order with your program installs. Our advice for you is to do the following: Open your Start Menu and type “cmd”. Right-click on the first icon and select Runs as Administrator. When the command line opens, type in the following command: “netsh winsock reset” . After you type it, hit Enter and after the command is completed, restart your PC. Now see if the problem has been fixed. If the issue persists, make sure to inform us and we will seek another way to aid you.
Is your PC in Safe Mode when you’re trying to get rid of the unwanted software? This is important and should not be overlooked. How and when does AmuleC get installed? Does it show in your Control Panel when it gets installed? A screenshot of the issue itself (your browser, the redirect, the installation of AmuleC, etc.) might help us determine where the problem is actually coming from.
At this moment, what is your situation – do you have Amulec and are you still getting redirected to the link above? If the issue persists, then there’s almost certainly a file buried somewhere in your system that is responsible for the installation of Amulec and the redirects. Here’s what I want you to do: Open your browser and go to the extensions menu – either make a screenshot of your extensions or tell us what they are. Also, did you check for anything added after “.exe” in the “target” text field in the properties of your browser shortcut (as instructed in Step 5 of the guide)?
127.0.0.1 v1.ff.avast. com
127.0.0.1 vlcproxy.ff.avast. com
Make sure to delete those IP’s and then save the changes.
What was “working normal again by itself” ? Could you be more specific with your issue so we’d be able to help you solve it.
Yes, this is how you’re supposed to do it. If you encounter any other issues, be sure to tell us here, in the comments.
So it seems that there are no problematic extension and also the shortcut seems to be okay. At this point, we advise you to use the scanner tool from the banners on this page and see if it finds anything. Tell us what happened after you scanned your PC and if the scanner detected anything. It is almost certainly that there is a file(or files) hidden somewhere in your system that you need to find and delete. We also advise you to send us a screenshot of what happens when you open the browser.
Can you locate any of the files that are regarded as threats? Probably, not all of them are problematic but some of them might be what’s causing the problem.
Here’s what you must do to be able to save the changes: Go to Start Menu and copy-past the following path – notepad %windir%/system32/Drivers/etc/hosts . After you have done this, right-click on the first search result and then choose Run As Administrator. This should enable you to make changes to the file and save it afterwards.
hi there .. m trying to end one process but its says access denied.. how can i end it .. i m also unable to open its file location .. click on option open file location redirects nowhere.. the process m trying to end is csrss.exe..
Do you have Administrator privileges on the account you are currently using on your PC?
Those IP’s are okay and there’s no need to remove them. If you still have the issue with the unwanted program, try the rest of the steps form the guide.
You should certainly remove all of those IP’s from your Hosts file. Remember to save the changes after you delete the shady addresses.
Did you check the Hosts file and the Registry Editor as instructed in the guide above?
Remove all of this since it is surely not supposed to be in your Hosts file. Remember to save the changes after you delete the shady IP’s.
these MFKRS i guess hacked!! — # localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Those IP’s are not coming from any unwanted software and should not be removed.
Oh god) i found two .exe files by going through the process you have shown) i didn’t fi d anything else and still the cse is on my computer (((
Did you check the Hosts file for any shady IP addresses. Also, what are the names of the .exe files and can you send us a screenshot of them?
In the temp files folder i found these two .exe files which are the main cause for sure but i am not an IT guy which can act like you guys.. here is their names– gB8C3.tmp.exe and gB8C2.tmp.exe weighing 174 and 180 kb respectively. also have same files on the same dates without .exe , only .temp files…
You should delete those files.
I have deleted them like 4 times and instantly they reappeared)))
In that case, open the Registry Editor and see if there are any shady keys. There are instructions on how to do that in the final step from the guide (Step 6).
All of those IP’s must be removed since they are more than likely coming from the unwanted program. Be sure to delete them and save the changes to the Hosts file.
Didi you try Step 4 from the guide to see if there are any suspicious IP’s in the Hosts file?
Probably not, but you can still check. However, what you should do now is tell us what program installs you have – it would be even better if you can send us a screenshot from the programs that you have on your PC (you can find the list of installed programs in the Control Panel under Uninstall a program).
127.0.0.1 cpm.paneladmin. pro
127.0.0.1 publisher.hmdiadmingate. xyz
127.0.0.1 distribution.hmdiadmingate. xyz
127.0.0.1 hmdicrewtracksystem. xyz
127.0.0.1 linkmate. space
127.0.0.1 space1.adminpressure. space
127.0.0.1 trackpressure. website
127.0.0.1 doctorlink. space
127.0.0.1 beautifllink. xyz
Those IP addresses are not supposed to be in your Hosts file. Delete them and save the changes to the file.
this redirect cse.google.com thingy has taken over my phone. i dont want to reset. how do i get rid of it. it redirects every app. ITS ANNOYING…
Hi Rachel,
I renewed our guide. Below the table you will see links for removing the virus from your phone. Have a nice day, Rachel!