Killnet
Killnet is a new and very nasty malware program of the malware category of ransomware cryptoviruses. Once in the machine of its victim, Killnet finds all files that may potentially be important to the computer’s user and then locks them with its file encryption algorithm.
“Your files have been encrypted” is probably not something you would expect to see pop-up on your screen when you try to open any of the files that are inside your computer. And yet, unfortunately, this is exactly what you can expect to be greeted by whenever you attempt to open a file in your system if a ransomware cryptovirus like Killnet has managed to attack your computer.
Sadly, these cryptoviruses are really common on the Internet and, in fact, most of the people reading this article are probably on this page precisely because of a recent infection with Killnet. After the virus has fully sealed all the targeted data with its encryption algorithm, it proceeds to blackmail the victims for money.
The Killnet virus
Now, since the files can no longer be opened via any conventional means, the Killnet virus displays a notification on the infected computer. In it, the Killnet virus tells the user that their only hope of recovering their data would be through the payment of a ransom.
Many victims of Killnet, Bowd or Bozq may think that this is actually their only shot at retrieving their files but we are here to tell you that giving in to the demands given by the hackers behind viruses like Killnet is not advisable. It is perfectly possible that you will lose your money and still not get anything that may help you with the encryption that is keeping your files inaccessible. Therefore, we think it is a better idea to first try some possible alternative courses of action before you actually consider the option that involves sending money to the criminals behind this ransomware.
The Killnet file encryption
If your files have indeed been taken hostage by the Killnet file encryption, the potential file recovery options are rather limited. The Killnet file encryption is quite sophisticated and makes it very difficult to deal with.

The guide on this page should help you with the removal of the cryptovirus but even if you manage to eradicate the ransomware, this won’t automatically bring your data back. Some suggestions on what you may do in an attempt to recover your sealed files can be found in the second part of our guide but we can give you no promises as to how effective any of those suggestions may be in your case. Still, it is important to make sure to clean your PC from the ransomware infection so that at least you won’t have any more of your files locked up. Again, you can still try the payment option but this always carries the risk of getting tricked and having your money taken without really receiving a decryption key for the encrypted data.
SUMMARY:
Remove Killnet Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
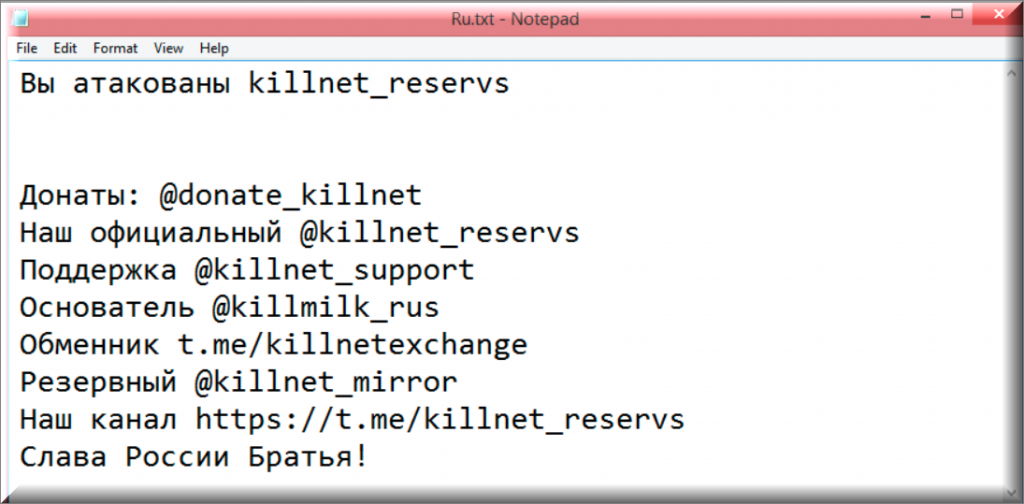
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Killnet files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply