R0n
R0n is a malicious piece of software that belongs to the ransomware virus category. Specifically, R0n is a cryptovirus, meaning that it uses encryption to use its victims’ files as leverage in exchange for a ransom payment.
In case you have important or sensitive data stored on your computer, then you most probably want to keep this data safe. And when it comes to data protection, there is one method that is praised as the best and that method is file encryption. If an encryption is placed on your important data, then no one would be able to open or use it unless they have the special decryption key for it. This method of data protection already has a broad implementation in sectors such as banking, insurance, medical administration and other areas where digital information should be kept safe from unauthorized access. Unfortunately, this same rather useful file encryption method has become the basis for a nasty blackmailing scheme which is the main agenda of a special category of malware known as ransomware cryptoviruses.
The R0n virus
The R0n virus uses a strong encryption algorithm in order to prevent its victims from accessing their own data. Then, the R0n virus proceeds to blackmail the victims for money in exchange for restoring their access to said data.
Ransomware cryptoviruses are pieces of malware created by anonymous Internet hackers and scammers, which are programmed to secretly sneak inside the users’ computers and apply complex encryption to the files that are stored there without the users’ knowledge. The idea of this action is to deprive the victims from the access to their own files and force them to pay a ransom in order to receive the decryption key for the sealed data. When such an infection completes the encryption of the files, it will most probably generate a ransom message on your screen, through which it will tell you that you must pay a certain amount of money (usually in Bitcoin) in exchange for the special key that can liberate your sealed documents. Such “offers”, however, should never be trusted because the hackers behind the infection can easily vanish with the money without sending anything in return.
There are many cryptoviruses that are able to do that, but on this page, we will mainly focus on one of the latest representatives of this nasty malware category – R0n. And we will tell you about the issues that it may cause if it finds its way inside your computer. In case you’ve landed on “How to remove guide” because you have already been infected with this threat, the information below may be very helpful to you if you want to remove the traces of the infection from your system and learn about the alternatives to the ransom payment.
The R0n file encryption
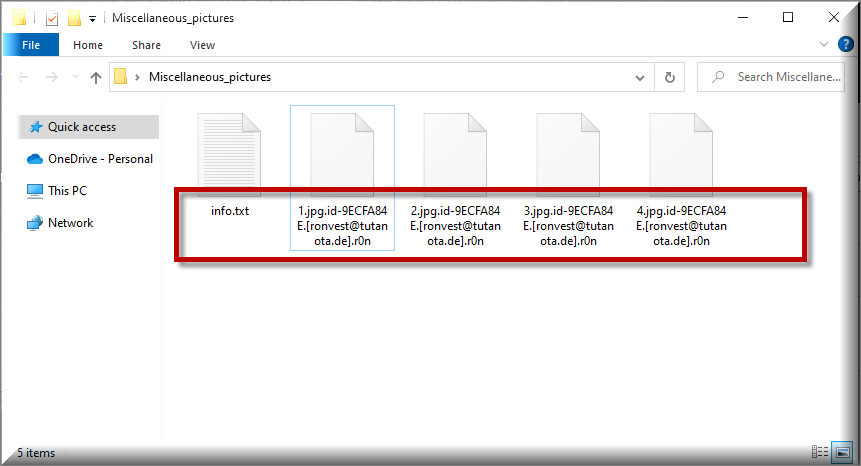
The R0n file encryption is very complex and undoing it can prove to be very difficult. You can recognize the files affected by it thanks to the R0n file extension added to the end of the encrypted file names.
What the best way to deal with a ransomware infection may depend on the specific case. That’s why we cannot tell you what the best thing to do is if you have been infected with a threat like R0n or Mztu. We can only give you some suggestions and alternative methods that you may want to try and also inform you about the risks and the consequences of the different courses of action.
The main problem with all ransomware-based infections is that, no matter what you do, there is usually no guarantee about the future of your files and that of your computer. If you have copies of your valuable data on an external drives, on cloud storages or on some other sources, this is the ideal case because you would only need to remove the malware and copy the needed files on your machine. If you don’t have backups, however, you should at least try some alternative tactics and methods of malware removal and file-recovery before you consider the ransom payment option as a “solution”. Our guide below has the instructions you may need to remove R0n as well as suggestions related to the data recovery.
SUMMARY:
| Name | R0n |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove R0n Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt R0n files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply