Venus Ransomware
This page aims to help you remove Venus Ransomware for free. Our instructions also cover how any Venus Ransomware file can be recovered.
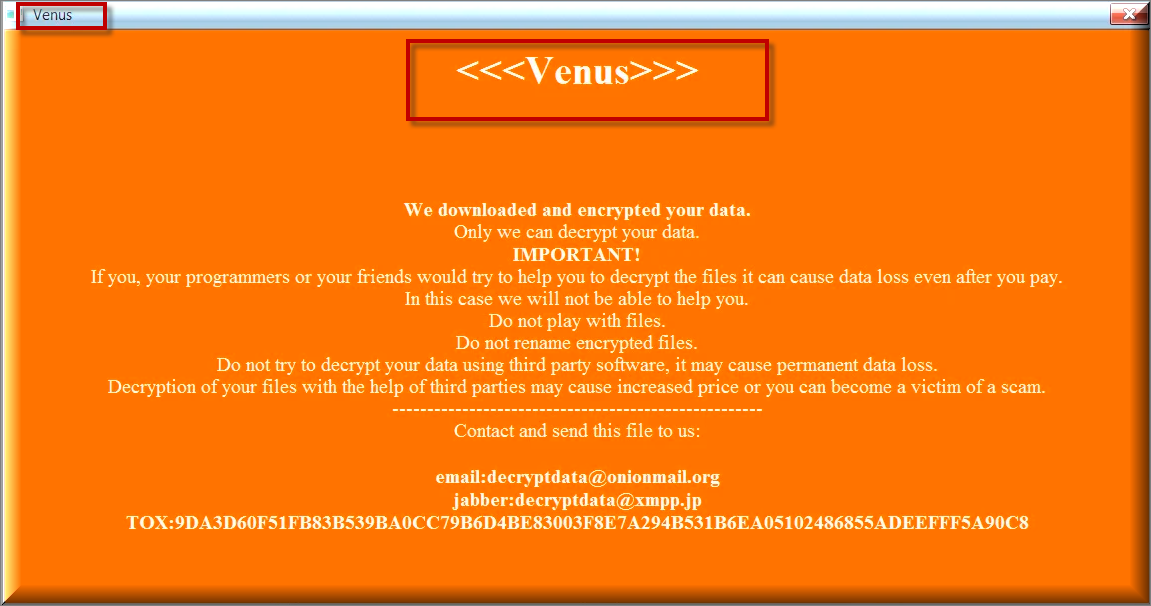
In the coming paragraphs users who have had the misfortune of getting to know a virus called Venus Ransomware are going to get all the info about it. This awfully malicious program has been characterized as a standard file-encrypting Ransomware version. The aforementioned malicious category comprises all the online threats able to infect your device without your consent and following that – get access to and encrypt the files they have concluded are important to you in some way. When all of these files have been encrypteded by Venus Ransomware , the victim user receives a terrifying message. Normally, the message the virus generates contains instructions about the way the requested ransom for the hijacked data is supposed to be paid. What’s more, the affected users may be threatened that if the demanded sum is not paid off in a timely manner or in full, the hackers who exploit this awful virus will NOT grant them back access to the inaccessible data.
Ransomware viruses usually operate as follows:
Such malicious programs like Venus,Tuis, Powz don’t resemble any other malware versions, and that’s the ultimate fact about them. It is possible that’s how and why they have become the most terrible PC threats that have ever existed on the web. Another very important detail about them is that Ransomware is almost never detected by any common anti-malware tool. Perhaps it’s like that because these malicious programs in fact don’t automatically show their malicious face. For example, what Venus Ransomware is able to do is NOT directly harming your device. It just creates copies of any data that it encrypts and then deletes the originals, in this way making you incapable of opening these files. Moreover, no symptoms usually result from such a malicious process and thus, it’s not visible to begin with. In some extremely rare cases, the unusually intensive usage of system resources like CPU/RAM could give the infection away. To top it all off, you need to keep in mind that the process of encryption itself has been first introduced strictly for safety purposes. Nevertheless, the creators of Ransomware have come up with a way to use it illegally for blackmail and personal gain.
The .venus file distribution
In case you are in fact thinking about paying the demanded ransom, we would like to remind you that the online criminals behind this .venus file virus really look forward to making you do that. They want you to believe this is your only available option.

Also, what you need to know about the process of paying the ransom is that there is normally a deadline, and a preferred currency is also mentioned – typically Bitcoins. This online form of payment is, among other things, well known for being absolutely untraceable. This is the way in which such criminals will try to avoid getting caught, and, quite unfortunately, in most of the cases they succeed in their attempts to do so.
Despite that, what is more important when we talk about Ransomware is that even the payment of the demanded ransom may not help the victim users and they may not receive any decryption solution. Consequently, our advice for you is to research all the options available first and only after then make the decision of whether you are willing to risk both your money and your files (pay the ransom), or simply just the already hijacked data (say no to paying the hackers). We have a little something that may help you fight off Venus Ransomware: we have attached a tested Removal Guide here, to assist you in making an attempt to remove this awful infection from your PC. However, it is not a miracle treatment and you should not expect it to necessarily save your files and deal with the virus automatically.
How does Ransomware get distributed?
What’s more, we advise you to try to maintain your PC in the best possible condition, since prevention is the only thing that always helps against threats such as Venus Ransomware. Prevention is mainly:
- To begin with, at any time, only visit reputable websites. Avoid all the web locations that are not completely trustworthy and trust your gut feeling.
- Always be extremely careful when it comes to all forms of SPAM. In the general case, Ransomware viruses travel via emails (and contaminated social media chat messages). It is quite simple: don’t click on any suspicious links or download (or open) any shady attachments.
- To conclude, here is the most important aspect of prevention – backing up your files. Learning to always back up all your essential data is the habit you need to teach yourself. Only this can sufficiently minimize any risks when it comes to Ransomware.
SUMMARY:
| Name | Venus Ransomware |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Venus Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Venus Ransomware files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!
All you need to know about paying the required ransom

Leave a Reply