
*Bgzq is a variant of Stop/DJVU. Source of claim SH can remove it.
Bgzq File
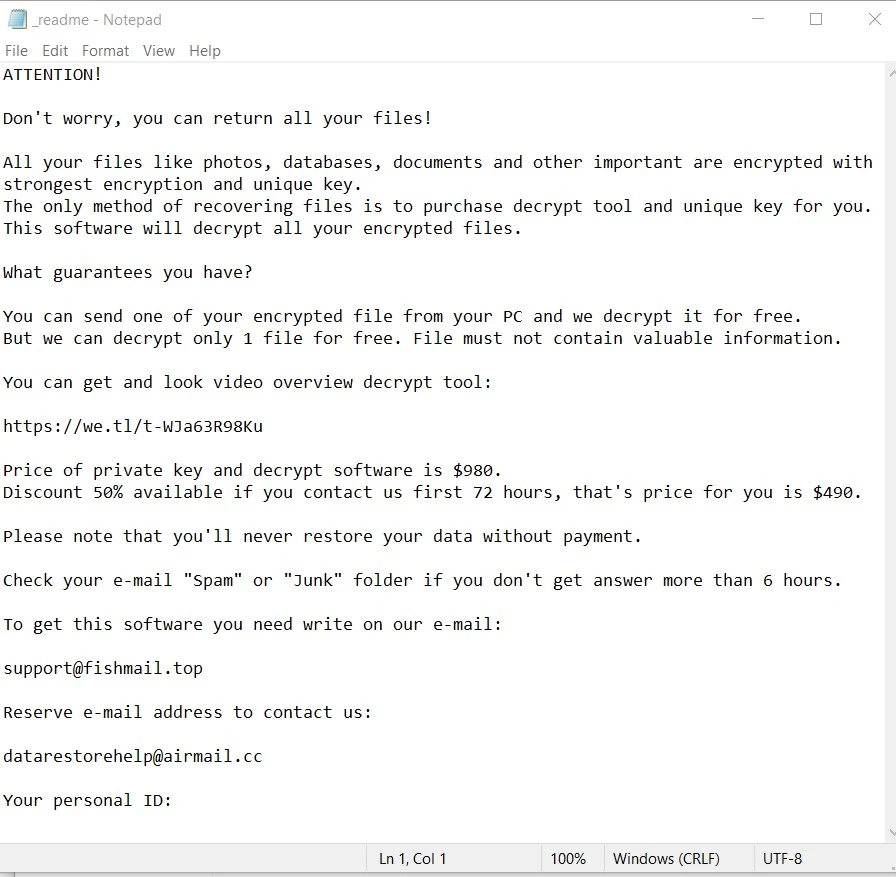
The Bgzq file encryption is a malicious process where ransomware software encrypts the files on a victim’s computer or network, rendering them inaccessible and unusable without the decryption key. The encryption process converts the files into a format that can only be deciphered with a unique key held by the attackers. Once the encryption is complete, the ransomware displays a ransom message demanding payment in exchange for the decryption key. The Bgzq file encryption is typically performed using strong encryption algorithms, making it extremely difficult, if not impossible, to decrypt the files without the correct key. Ransomware file encryption is a devastating tactic used by cybercriminals to extort money from victims, as it denies access to critical data and systems until the ransom is paid.
How to decrypt Bgzq ransomware files?
How to remove Bgzq ransomware virus and restore the files?
Bgzq Virus
The Bgzq virus is a malicious software that infects computers and initiates a sophisticated encryption process to lock the files stored on the compromised system. It demands a ransom payment from the victim in order to regain access to the encrypted files, as instructed by the creators of the virus. If you find yourself infected with the Bgzq virus, it is crucial to remain calm and approach the situation with a clear mind. While paying the ransom may seem like a tempting solution, it is not the ideal option due to the uncertainty of receiving the decryption key even after making the payment. There is a risk that the hackers may take your money without providing the necessary key to unlock your files.
Bgzq
Ransomware infections like Bgzq, Bgjs, Wwza and Wwpl are widespread malware programs the primary objective of which is not to damage or steal data, but rather to hold the files hostage and demand a ransom for their release. Once the targeted files are locked with a sophisticated encryption code, the Bgzq ransomware displays a message on the victim’s desktop, stating that the only way to regain access to the files is by paying a specified amount of money to the criminals behind the ransomware attack. Typically, a deadline is given, usually a day or two, for the payment to be made. If the payment is not made within the given timeframe or is refused, the victims are often threatened that they will permanently lose access to their files.
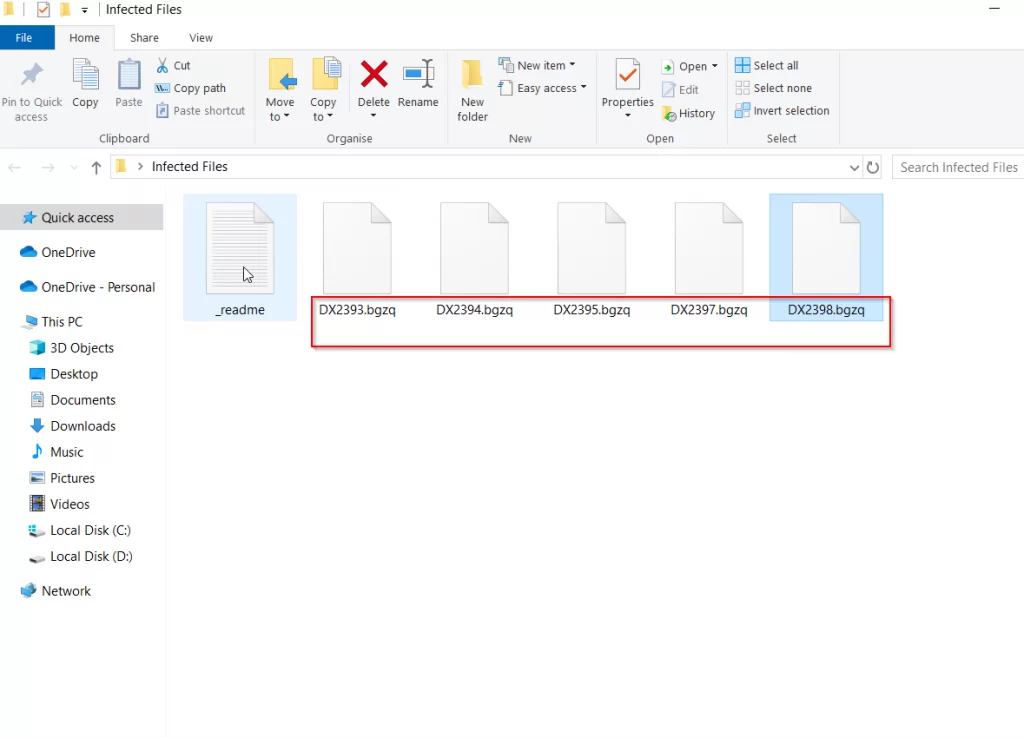
.Bgzq
.Bgzq is a suffix that gets attached to the files affected by the Bgzq ransomware. Once applied, this suffix renders various types of digital data inaccessible and unusable unless a special decryption key is used to decipher it. The purpose of the .Bgzq suffix is to hold the victim’s files hostage, with the attackers demanding a ransom payment in exchange for the decryption key. The ransomware that uses this encryption suffix typically spreads through various deceptive methods, such as illegal downloads, spam messages, and Trojan Horse backdoors. Therefore, users must exercise caution when downloading files from unreliable sources and remain vigilant against suspicious emails or attachments to minimize the risk of falling victim to this harmful malware.
Bgzq Extension
Ransomware typically encrypts your files and alters their original extensions or adds new extensions to them. That’s why, one of the most notable indicators that you have fallen victim to an Bgzq ransomware attack is the presence of the Bgzq extension that is typically attached at the end of your regular files. For example, if you had a file named “text.docx,” it may be renamed to “text.docx.Bgzq” or have a completely different extension altogether. This change in file extensions is a clear sign that your files have been compromised by ransomware. If you come across such changes, especially the Bgzq extension, it is crucial to take immediate action to prevent further damage and begin the necessary steps to address the ransomware infection.
Bgzq Ransomware
The encryption technique employed by Bgzq Ransomware is a critical factor in its effectiveness. However, detecting the encryption process can be challenging due to its minimal and often unnoticed symptoms, such as occasional spikes in RAM and CPU usage. Even if you have a reliable antivirus program installed, it may not detect the Bgzq ransomware, as the encryption process typically does not cause any immediate harm to your computer or files. Once the encryption is completed, your data will remain locked, even if you manage to remove the malware from your system. Therefore, it is essential to prioritize the removal of the virus before attempting any data restoration methods to prevent further files from being encrypted by the ransomware.
What is Bgzq File?
As we already explained, the Bgzq file encryption works like a digital hostage situation for your files. When your computer gets infected with ransomware, the malicious program starts sneaking into your files and wraps them up in a tight digital lock. It uses advanced encryption algorithms to scramble your precious data, making it unreadable and inaccessible. It’s like putting your files inside a secret vault that only the ransomware creators hold the key to. They demand a ransom payment from you in exchange for that precious Bgzq file decryption key. Until you pay up, your files remain trapped and unusable. It’s a clever yet wicked way for cybercriminals to extort money from unsuspecting victims, holding their valuable data hostage until they give in to the ransom demands.
SUMMARY:
*Bgzq is a variant of Stop/DJVU. Source of claim SH can remove it.
Bgzq Ransomware Removal

Restarting the computer in Safe Mode is described in detail in Step 1 of this guide. In order to remove the virus from your computer, we recommend that you begin by clicking on Safe Mode and completing the steps described in the link.
Please save this page to your browser’s preferred bookmarks, before you reboot the system, so you don’t have to search for Bgzq removal instructions every time you restart your computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Bgzq is a variant of Stop/DJVU. Source of claim SH can remove it.
Bgzq ransomware is difficult to deal with since it can remain undetected for an extended period of time and do significant harm to the system.
When this ransomware infects your computer, one of the most difficult things you’ll have to do is find and terminate its malicious processes. Please read and carefully follow the directions in the following paragraphs if you are concerned about the safety of your computer.
Press CTRL+SHIFT+ESC on your computer’s keyboard at the same time. Focus your attention on looking for processes that might be related to the threat. The Processes tab in Windows Task Manager shows this information.
The next step is to scan the files associated with any questionable processes. You can do that by opening the fast menu when you right-click on the suspicious processes and then select Open File Location.

To save time, you can use the free online scanning tool provided below to confirm that the files connected with this process are clear of any potentially harmful code.

You must first stop the processes associated with any of the files that have been marked as potentially harmful by right-clicking on it and choosing End Process. After that, remove the infected files from their original place.

Additionally, you should deactivate any potentially hazardous startup items that Bgzq may have brought to your system without your awareness, after you’ve ended the malware-related processes. You can do this if you check the Startup tab in System Configuration.
To access it, type msconfig in the Windows search field and press Enter.

Once in the startup tab, the thing you should do is uncheck any items related with the malware. Also look for any other start-up elements not associated with the applications that launch when the system boots up. Unchecking their respective checkboxes will turn them off. Make sure you don’t disable any operating system or trusted software components while you’re doing this!

*Bgzq is a variant of Stop/DJVU. Source of claim SH can remove it.
Delete any dangerous registry entries found in your registry editor to ensure the ransomware is completely eliminated, and no hazardous components are left behind.
If you type regedit in the Windows search box and hit Enter, the Registry Editor will open. Use the CTRL+F keyboard shortcut to find ransomware-related files in Registry Editor, and type the ransomware’s name in the Find box. After that, click on Find Next to begin the search. A harmful entry can be removed by right-clicking on it.
Attention! Delete just the registry entries associated with ransomware. In order to avoid damaging your system and installed software, it is important to bear in mind that altering the registry or removing anything that is not directly connected to the danger is a bad idea. In case you need help with removing the ransomare-related entries, make sure to check out this page’s link to an anti-malware program that can help you get rid of the virus and other infections on your computer.
Once you’ve finished with the Registry Editor, check the locations specified below for any other potentially harmful files or subfolders that could be lurking there. Simply type in their names in the Windows Search field and press Enter to open them one by one.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
It’s a good idea to double-check any newly-added files or subfolders for anything suspicious. Everything in the Temp folder should be deleted from your computer to remove any possibly harmful temporary files.
You’ll next want to inspect your computer for any harmful changes to the Hosts file. Hold down both the Windows key and the R key from the keyboard to open a Run dialog box, where you may enter the following command:
notepad %windir%/system32/Drivers/etc/hosts
We’d want to know if you see any strange IP addresses in “Localhost” as shown in the image below. Don’t hesitate to ask us anything in the comments section if you have any questions or concerns.


How to Decrypt Bgzq files
Even for experts, dealing with the implications of ransomware data encryption may be a challenging task. Fortunately, there are some file-restoration tools that may allow you to decode encrypted data. First, however, you need to find out what variant of Ransomware you’re dealing with. To obtain this information, look at the end of the encrypted files and their file extensions.
New Djvu Ransomware
STOP Djvu is a recently released Ransomware variant that is actively attacking users worldwide. You’ll be able to tell this particular danger apart from others thanks to the .Bgzq suffix that it attaches to the encrypted data.
There is a way to retrieve data encrypted by this variant, if the ransomware is using an offline key for its encryption. A file-decryption tool is included below, and it may be downloaded by clicking on the link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
Run the decryption tool that you’ve downloaded as an administrator, then select “Yes” to start it. Next, read the included instructions and the license agreement. The decryption process will begin when you press the Decrypt button. If you need to decode files encrypted using unknown offline keys or online encryption, please note that this tool may not be able to decode them.
Important! Before attempting to recover data that has been encrypted, carefully search your computer for any hidden ransomware-related files and harmful registry entries. We recommend that you use this page’s online virus scanner and the professional anti-virus software to remove any traces of malware that you find. If you have any questions or concerns, please free to post them in the comments area down below, so we can help you.

Leave a Reply