.Avast
.Avast belongs to the infamous Ransomware cryptovirus family. Typically, .Avast targets the files on a given computer with in order to encrypt them, and to then demand a ransom for the data’s decryption.
You will learn some important information about this new malware, as well as about the specifics of the Ransomware infections, in the paragraphs below. Many readers of this article may have come here to seek assistance on how to remove .Avast from their computers. If you are one of them, we have to inform you that nearly all Ransomware viruses use similar techniques to achieve their objectives. In the first stage of the infection, a complete hard-disk scan is usually performed to locate certain types of preset computer files. Documents, audio and video files, and, in some cases, data files from the system are the usual target. Once it locates them, the harmful software creates an encrypted copy of every single file, and deletes the originals. In the final stage, the virus program displays a pop-up on the user’s computer, with instructions on how to perform a payment in the form of a ransom if the victim wants to regain access to their information.
The .Avast virus
The .Avast virus is rapidly spreading all over the internet. Carriers of the .Avast virus can be various harmless-looking files, email attachments, torrents, ads, and spam.
Detecting an infection such as .Avast, Bpqd, Kqgs however, may be challenging for most security programs, since there will be no file damage after the file encryption process completes. Thus, your anti-malware program is unlikely to warn you that a file-encryption process is happening in the background of the system. This is because, in reality, the encryption is a widely used technique for data protection, and it is usually not expected to cause damage. Used by a Ransomware, however, the encryption can prevent you from opening your personal files by keeping them hostage for a ransom.
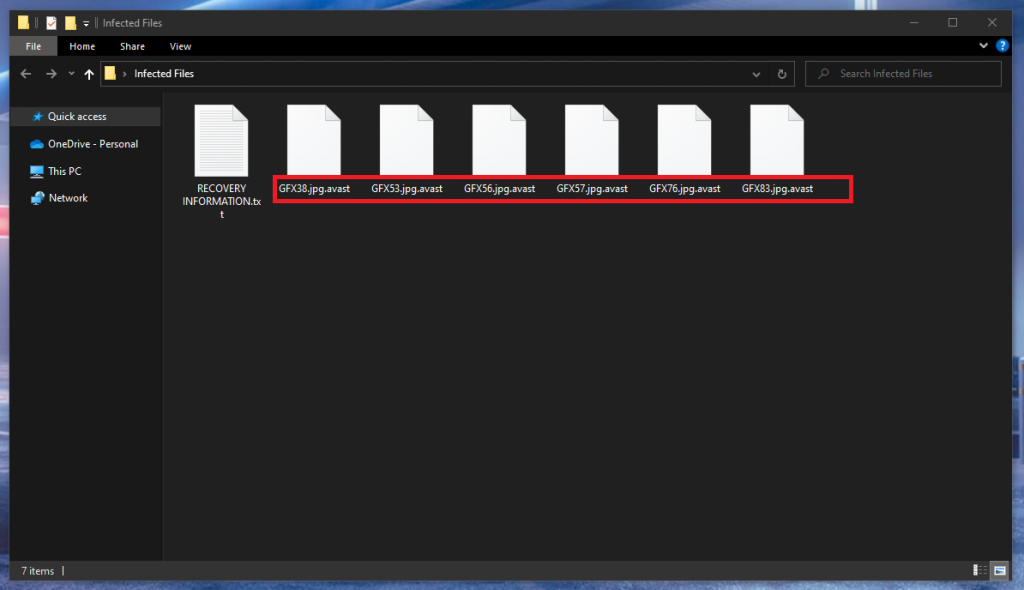
The .Avast file extension
The .Avast file extension is a special file extension that will only appear on the files that have been encrypted. The purpose of the .Avast file extension is to make the encrypted files unrecognizable to any program, and thus, make them harder to decrypt.
If your machine has been attacked by .Avast, you should remember that when it comes to Ransomware, nothing is certain. In case you decide to pay the ransom, you are likely to lose your money regardless of whether you manage to recover your files or not. Moreover, the cyber criminals may decide to ask for more money once the initial payment has been made.
Besides, even if you get a decryption key from them, there is a strong possibility that this key may not function as expected, and fail to decrypt the encrypted information. At the same time, proceeding with the payment of the ransom would definitely assist the hacker who blackmails you with continuing to do the same with other web users. Because of all of the above, we always recommend that our readers look for alternatives, and concentrate on how to remove the Ransomware, instead of give their money to some crooks. Of course, if our removal guide below, or the other techniques you may try, turn out to be ineffective, you can always consider paying the ransom as your last possible solution.
SUMMARY:
| Name | .Avast |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove .Avast Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Avast files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment