
C3rb3r
C3rb3r is a ransomware variant of the file-encrypting subtype. This means that C3rb3r can lock the files on a computer by encrypting them, and then demand a ransom payment in exchange for having said files decrypted.This is among the nastiest, most treacherous cyber criminal schemes on the internet, but it’s also among the oldest. Believe it or not, but ransomware has actually been around since the late eighties to early nineties. But it wasn’t until the past decade or so that this malicious software category exploded and became the plague that it is today. Largely, this had much to do with the emergence of cryptocurrencies that offer criminals the shield of anonymity. As you might have noticed, the hackers behind C3rb3r have likely requested that you pay them your ransom amount in bitcoins or some other cryptocurrency.
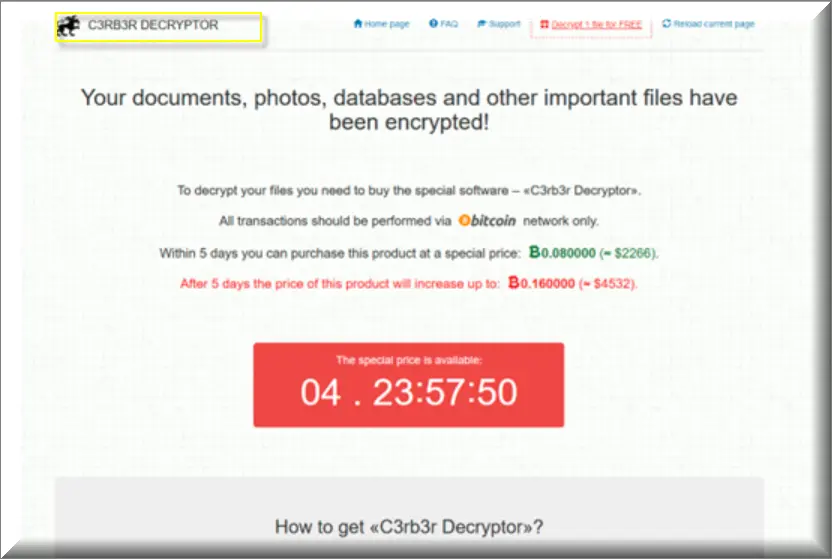
C3rb3r decryptor
Paying pay them for “C3rb3r Decryptor” for your ransom amount in bitcoins ensures that the proper authorities won’t be able to trace them when it comes to it. And with there being no legal consequences for them, the criminals are basically free to continue with their illegal enterprise. This is one of the reasons why we do not recommend immediately complying with their demands and paying up. Virtually the only way we can undermine them is by refusing to fund their line of business. But on top of that, criminals behind viruses like C3rb3r decryptor may not even be willing to provide you with a solution even after you’ve sent them your money. So it’s always best to explore alternative solutions, such as the ones we’ve listed in the second part of the removal guide below.
The C3rb3r Ransomware
The C3rb3r ransomware is a particularly tricky to deal with because it doesn’t trigger most antivirus programs. This means that the C3rb3r ransomware can easily be at work right under the nose of its victims without being interrupted at all.This is another very large advantage that ransomware viruses have over other malware. But it also puts them two steps ahead of the cyber security community as well. And the reason behind this phenomenon is painfully simple. Ransomware like C3rb3r doesn’t do anything to harm the files or corrupt them, the way that a Trojan might do, for example. Instead, it applies an encryption algorithm – something so commonplace these days that if antivirus software were to be triggered by it, it would be impossible to use the internet to check our emails or use our online banking for example.
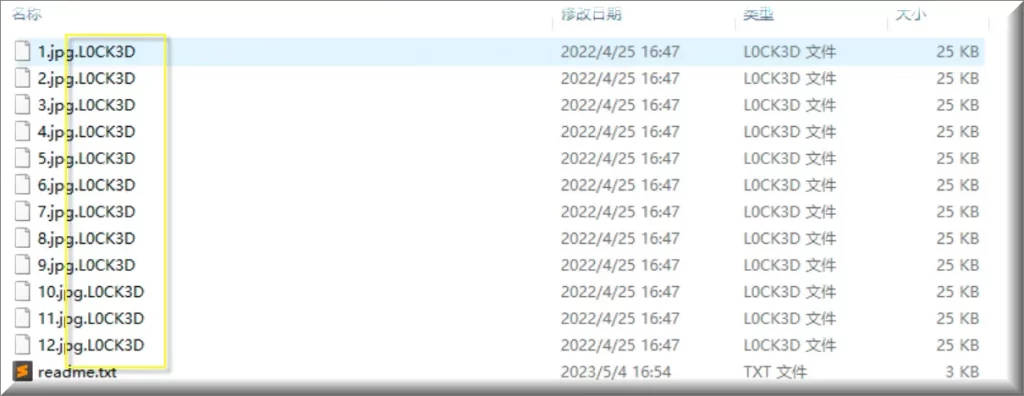
The l0ck3d file extension
The l0ck3d file extension, like .mkp is the suffix you see at the end of each and every one of the encrypted files. The l0ck3d file extension prevents any other program from recognizing the file format and therefore being able to open it. In closing, we would like to say that there is, unfortunately, no possibility to guarantee that the file restoration methods we have here will work in your particular case. Ransomware infections are notoriously difficult to deal with exactly due to this uncertainty. And as stated earlier, not even paying the hackers will guarantee results either. But we do recommend trying anyway and we hope you will be successful.
SUMMARY:
| Name | C3rb3r |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
We tested that SpyHunter successfully removes C3rb3r* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and C3rb3r may reinstall itself at the end if you don’t delete its core files. |
Remove C3rb3r Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt C3rb3r files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply