.Mkp
.Mkp is a Ransomware virus that encodes different files on the attacked computer, thus rendering them inaccessible. As soon as .Mkp completes the file-encryption, it starts blackmailing the user, asking for a ransom payment in exchange for a decryption key.
The worst viruses that can attack your machine are the so-called Ransomware cryptoviruses. They can secretly sneak inside any computer, scan it for a specific list of files and then encrypt those files one by one. Once encrypted, the targeted files become inaccessible and no program can open or use them unless they get decrypted. The decryption, however, is only possible with the help of a decryption key, which is held by the hackers who stay behind the Ransomware. The crooks blackmail their victims to pay a ransom in order to receive the key for the sealed information.
In the next few pages, we will speak about all the possible methods to deal with the .Mkp Ransomware and we will provide you with instructions on how to remove it from your system. We will also give you some file-recovery instructions which may prove effective in retrieving your files from system’s backup copies, which would allow you to avoid the ransom payment.
The .Mkp ransomware
The .Mkp ransomware is a virus infection that can apply encryption to the files stored on a the attached computer and restrict the access to them. When done with the encryption, the .Mkp ransomware demands a ransom payment for the files’ decryption.
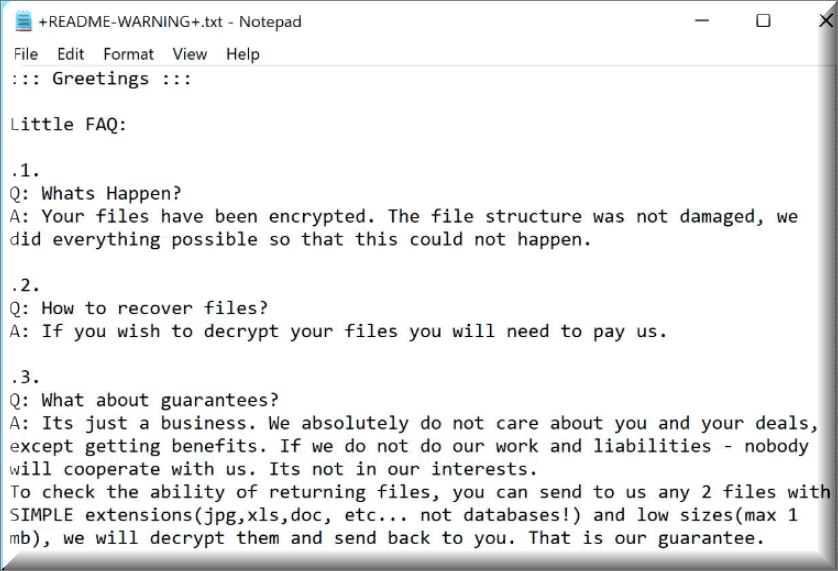
The Ransomware typically scans the computer drives and locates file formats that are commonly used. All the predetermined information eventually ends up getting secured with encryption and thereby rendered inaccessible. If you try to open an encrypted file you will most likely see an error message. But before you even try to open any file, you will most probably be notified about the applied encryption with the help of an on-screen message. The role of that message is to inform you that, in order to access your files again, you will have to pay a ransom to the hackers who hold the decryption key. If you refuse to pay the required money on time, you might be threatened to never receive a decryption key and to never be able to open or use any of the encrypted information again.
The .Mkp file encryption
The .Mkp file encryption is an advanced algorithm that can render digital files inaccessible. Reversing the .Mkp file encryption requires the application of a decryption key which is kept on the computers of the hackers behind the Ransomware.

Many web users ask us what they should do in order to cope with this horrific infection. Unfortunately, there is no method that could guarantee a 100% success when it comes to dealing with cryptoviruses such as .Mkp, Jhgn, Jhbg or Jhdd. At times, neither paying the ransom nor deleting the virus from the system will get the encrypted files back to their previous state and they may ultimately be lost forever. Therefore, each victim must decide whether to try to remove .Mkp on their own or make the payment and risk losing their money in vain.
The main problem if you decide to pay is that nothing can guarantee that after the ransom has been paid in full within the time provided limit the online criminals will immediately send you a decryption key. Not to mention that, if such a key really exists, it may still fail to reverse the complex encryption that the Ransomware has applied. If you remove the infection from your system, however, you may have a chance to save some of the files through personal backups or with the help of the instructions in the removal guide below. Of course, we can’t promise that you will be able to recover all your files, but it’s worth trying all available alternatives.
SUMMARY:
| Name | .Mkp |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Most users don’t notice anything suspicious while the Ransomware is locking-up their most important files. |
| Distribution Method | This type of malware is oftentimes paired with Trojan Horse backdoors that distribute it and deliver it to the users’ computers. |
| Detection Tool |
Remove .Mkp Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt .Mkp files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment