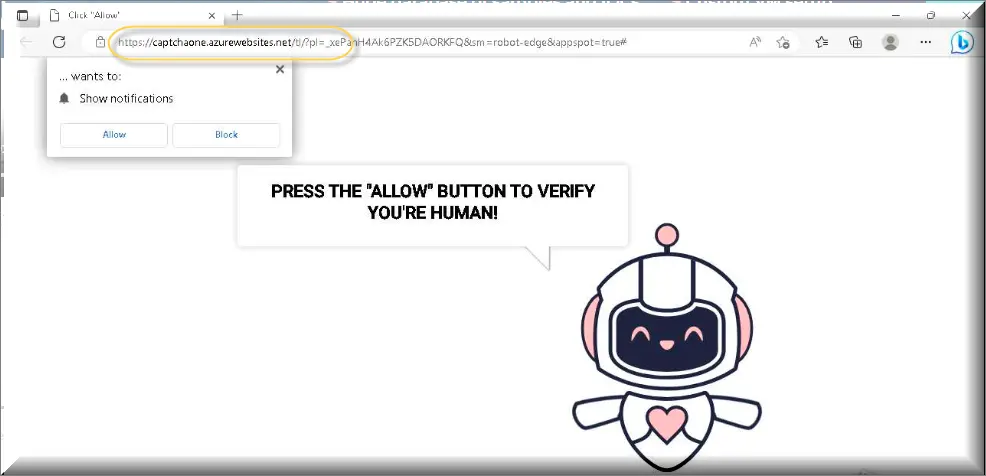
Captchaone.Azurewebsites.net
Browser redirect viruses, like Captchaone.Azurewebsites.net, are a family of viruses responsible for replacing the search results of your browser with their own. Whatever your preferred search engine maybe the Captchaone.Azurewebsites.net redirect virus will replace it. Likewise instead of receiving normal results on your searches you will receive a mixed batch of useless spam and Ads. These replacement search engines are a very poor replacement for Google/Bing/Yahoo. Their sole purpose is to display the Ads you see on your screen and this can make browsing extremely frustrating, not to mention the danger from visiting a dangerous web page through the Ads. We highly recommend that you uninstall the Browser redirect virus from your computer as soon as possible.
Is Captchaone.Azurewebsites.net Safe?
The main reason for the existence of the redirect viruses, like Captchaone.Azurewebsites.net or Pakfn.co.in ,is online traffic and the money it generates. Basically all search engines rate pages that are frequently visited higher then those that are not. Site owners want to be shown on the highest page of the search as possible and so all traffic is helpful to them. A redirect virus will spawn links of affiliated sites on hundreds of thousands infected computers. Even if a few percent of those redirected Ads are clicked on the creator of the virus will get considerable payment for his efforts from the sites that have been accessed via the links.
Captchaone.Azurewebsites.net Virus
Google and Bing display Ads too, like the Captchaone.Azurewebsites.net virus, but those Ads are well regulated and immediately taken down if found to contain malware or scams. This also means that Ads shown by redirect viruses, like Captchaone.Azurewebsites.net, are much more dangerous and often used by virus makers to spread their “children”. Sites that display dangerous Ads are quickly blacklisted and you are given a warning if you try to visit one of them if using a normal search engine. With the redirect virus installed you are on your own. Since these types of viruses exist to spam your computer with Ads it makes sense to show you the most relevant Ads to your interests. To do that these viruses will spam your online activity and filter the appropriate Ads based on your interests. This data can also be send to the remote host of the virus creator and sold out to other hackers! This is one example of how your email may get into some kind of spam list.
What is Captchaone.Azurewebsites.net?
Whenever a Captchaone.Azurewebsites.net redirection occurs a new tab will be opened containing the virus featured content. Google redirect viruses are by far the most common ones, but Bing, Yahoo and Ask also have their own variations. Sometimes redirect viruses, like Captchaone.Azurewebsites.net, a specifically tooled to target a particular browser and due to Google Chrome’s popularity it is the most common victim. A Chrome redirect virus is actually contained within the browser itself as an add-on installation. This gives it a large control over the functionality of Chrome. A redirect virus can also change your home page and it will definitely mess with the default search engine. These changes are usually applied via a script and they cannot be removed manually as the virus simply sets them back automatically on every browser restart.
Captchaone.Azurewebsites.net Pop-ups
Due to their close interaction with your browser redirect viruses, like Captchaone.Azurewebsites.net Pop-ups are usually viewed as high level threats. A Chrome redirect virus can display all kinds of Ads that may look like system related messages on your screen. These are always fake and they aim to instill some kind of urgency into you. The problems they report are either exaggerated or non-existent, but the software recommended to fix these problems is actually either useless bloatware or rigged with a virus. When you are browsing and see some kind of system error message or Captchaone.Azurewebsites.net Pop-up try to close Chrome/Firefox first. If the problem is not real, but created by a Chrome redirect virus the message should go away when your browser is closed. Don’t attempt to download any software related to that message, but focus your efforts on finding the virus instead. Similarly there are a number of other fake issues that can be caused by the redirect virus:
- Missing plug-ins, video players, codecs and the like. If you’ve had no problem seeing videos online and suddenly you see messages claiming the contrary then the cause is the redirect virus.
- Tab redirects sometimes try to make you download different executable programs directly. Often these will trigger when you attempt to download something from a site yourself. Be very careful as these contain the worst viruses inside.
- Different type of “online scanners” can be used by the redirect virus in order to confuse you. These “scanners” will claim to have searched your computer for free and found problems (viruses, errors etc). This is just a scam – a scanner can never scan your computer without you giving it permission to do so first.
- Fake lotteries, polls and programs updates are also frequently exploited. You’ll get a message that your Java/Flash/other program needs an update. That update will contain the virus. The lotteries and questionnaires will require you to download and install some file to complete installing the virus in much the same way as the update scam.
Captchaone.Azurewebsites.net on Chrome
Like most malicious applications Captchaone.Azurewebsites.net on Chrome come from infected executable files. These can be obtained from a multitude of sources, but we have compiled a short list of the most common ones you are most likely to encounter:
- Software bundle installers. These are actually installers for other programs, but they carry addition programs inside that will also get installed as long as the Default installation option is selected. Because of this we advice all of our readers never to use Default – go for Advanced instead. It takes only a couple of extra seconds and mouse clicks, but while you do them you get to see a detailed list of all the programs and features that will get installed. Remove any additional software from this list even if it looks innocent enough – you can never know for certain if there is a virus inside.
- Email attachments bombs – it’s a very old, but still very effective tricks. The latest hit is to spam emails that look well written and appear to be work related. They will contain some file like Invoice.exe or Report.exe or whatever work related file you can think of. Be wary of the .exe file extension, because .exe is an extension assigned to programs /and viruses/ and office files are never .exe. NEVER download and install .exe files unless you are sure they are safe!
- Torrent and online storage sites are a cesspool of viruses. Any executable file downloaded from a torrent site can carry a virus. Sometimes these also have multiple download buttons spread around the page and only one of these (if any) will be real. Clicking on a fake button will also result in a file download, but this file will be a virus and not the file you want!
SUMMARY:
| Name | Captchaone.Azurewebsites.net |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Remove Captchaone.Azurewebsites.net
To try and remove Captchaone.Azurewebsites.net quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Captchaone.Azurewebsites.net extension (as well as any other unfamiliar ones).
- Remove Captchaone.Azurewebsites.net by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Captchaone.Azurewebsites.net and any other suspicious items.
If this does not work as described please follow our more detailed Captchaone.Azurewebsites.net removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Captchaone.Azurewebsites.net app and kill its processes
Uninstall the Captchaone.Azurewebsites.net app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Captchaone.Azurewebsites.net. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Captchaone.Azurewebsites.net, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Captchaone.Azurewebsites.net.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Captchaone.Azurewebsites.net changes made to different system settings
Undo Captchaone.Azurewebsites.net changes made to different system settings
It’s possible that Captchaone.Azurewebsites.net has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Captchaone.Azurewebsites.net from your browsers
Remove Captchaone.Azurewebsites.net from your browsers
- Delete Captchaone.Azurewebsites.net from Chrome
- Delete Captchaone.Azurewebsites.net from Firefox
- Delete Captchaone.Azurewebsites.net from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Comment