
*Source of claim SH can remove it.
Diet.exe
This page aims to help you remove Diet.exe virus. Our removal instructions work for every version of Windows.

If a strange virus named Diet.exe has infected your computer and has caused you some serious issues, this page contains a removal guide that will help you remove it. If you stay here, you will learn what actions you need to take to safely get rid of the infection. Unfortunately, this is a nasty Trojan horse, and you will need all your attention to deal with it because one sure thing about this type of infections is that they can be very very harmful and tricky. That’s why, the sooner you remove Diet.exe virus, the better. But first, make sure you understand what exactly is happening to your PC, how the Trojan operates and how to identify it.
What is happening?
If a threat of the Trojan horse type like Diet.exe virus invades your system, you should know that it is highly recommended to remove it immediately because this type of malware is capable of limitless harmful deeds and can expose you to great security risks. Every Trojan infection is different and has its own “mission”, which entirely depends on what specific malicious actions the criminals, who control the threat, want to perform. This means that you can never be sure exactly what harm Diet.exe virus can do while inside your system. Mostly, an infection of this type is developed and used to perform online fraud and theft. Thanks to the vulnerabilities it creates, the Trojan can provide the hackers with unauthorized control to the infected computer and give them access to all the sensitive data, software and resources you keep there. This way, various criminal activities may take place such as data and system corruption, deletion of files, disk formatting, tracking of the victim’s activity, passwords and credential stealing, leakage of banking details and confidential or personal information, bank accounts draining and compromising online profiles, or insertion of other infections such as Ransomware and other viruses.
The victims may eventually notice some abnormal activity on their screen or some strange system behavior, such as sudden crashes, deletion of files or software, or high CPU and RAM usage without any active interaction from their side. However, in most of the cases, the Trojan tries to remain hidden and perform its activities under cover. Therefore, it is very hard to detect it and stop it unless a major system damage reveals it.
How can Diet.exe Trojan infect you?
Such a tricky malware has many ways to get inside your PC. A Trojan horse like Diet.exe virus uses the so-called “social engineering” tactics to trick the victims into clicking and installing the malicious payload, which is usually very well hidden in some seemingly harmless content. Some of the favorite distribution and infection methods that the criminals frequently use include camouflaging the infection as an email attachment, a spam message, some attractive installer or a torrent, a PDF file, or an offer, misleading link or a virus-inflicted web page. They rely on the people’s curiosity to interact with the harmful payload without knowing what is hiding inside and to get infected by clicking or installing it.
How to protect yourself
Trojan horses are the most common cause of online infections. They are the most widely spread and the trickiest to prevent, that’s why you should always have a good protection against them. Along with the popular Ransomware infections, threats like Diet.exe and Healthy.exe virus are the biggest trouble makers among the malware that roams the web. To effectively keep them away, it is a good idea to invest in reliable antivirus protection. If regularly updated to the latest virus definitions, good antivirus software can recognize a potential malicious transmitter and stop it from getting installed on your system.
However, you should not rely only on your antivirus to protect your PC. As smart and sophisticated as it can be, such software may not always be able to save you if you are careless when browsing the web and frequently expose yourself to insecure content and shady web locations. That’s why, our advice is for you to be sensible when surfing the web and not to seek for the malware by clicking on shady pop-ups, different links, and spam messages. Always run system scans and avoid installing software from unknown sources, pirate sites, too-good-to-be-true offers, free setups and torrents because sometimes the “free gifts” may come at a high price.
To remove Diet.exe virus, we advise you to strictly follow the instructions in the removal guide below. Pay attention to each step, especially when you need to interact with vital system files, because deleting the wrong ones may seriously corrupt your OS. For extra safety, don’t hesitate to use the special Diet.exe Trojan removal tool. It will help you eliminate the Trojan in a few clicks, without the risk of deleting something else by mistake.
SUMMARY:
*Source of claim SH can remove it.
How to Remove the Diet.exe Virus?
To remove the Diet.exe virus from your computer’s system, you need to clean the computer from rogue programs, processes, files, and unauthorized settings in the following way:
- The first step is to find and uninstalled any potentially unwanted programs that may have caused the infection.
- Also, you must search the Task Manager for rogue processes and stop anything that seems related to the Trojan,
- Thirdly, the DNS settings, the Hosts file, and the Startup items list must be restored to their normal states in case changes have been made to them by the virus.
- Lastly, to remove the Diet.exe virus and ensure it doesn’t return, you must clean the Registry of your PC.
To help you with the completion of those steps, we’ve provided detailed instructions and some tips for each of them down below.
Detailed Diet.exe Removal Instructions
Before you begin the guide, we recommend that you temporarily stop your Internet connection to the computer – this will prevent Diet.exe from receiving new instructions from its creators’ servers which could make removing the Trojan more difficult.
Step 1
*Source of claim SH can remove it.
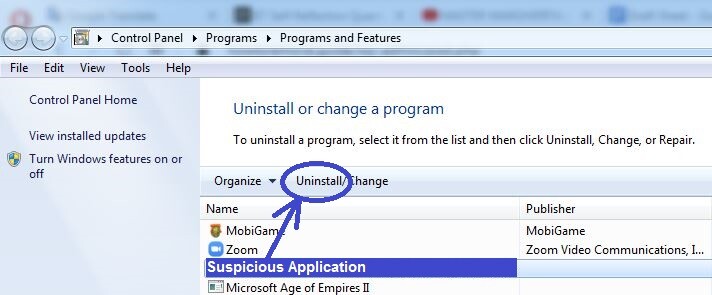
Go to Control Panel/Programs/Programs and Features (you can look for the Control Panel in the Start Menu, or search for it in the Start Menu search bar). There, look at what programs have been installed recently and if any of them are unfamiliar to you and/or look suspicious, you should probably uninstall them. During the installation, do not allow the uninstallation manager to keep any temporary files or personalized settings for the program – if you are given such an option, refuse it.
This block contains unexpected or invalid content.Attempt Block Recovery
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
This block contains unexpected or invalid content.Attempt Block Recovery

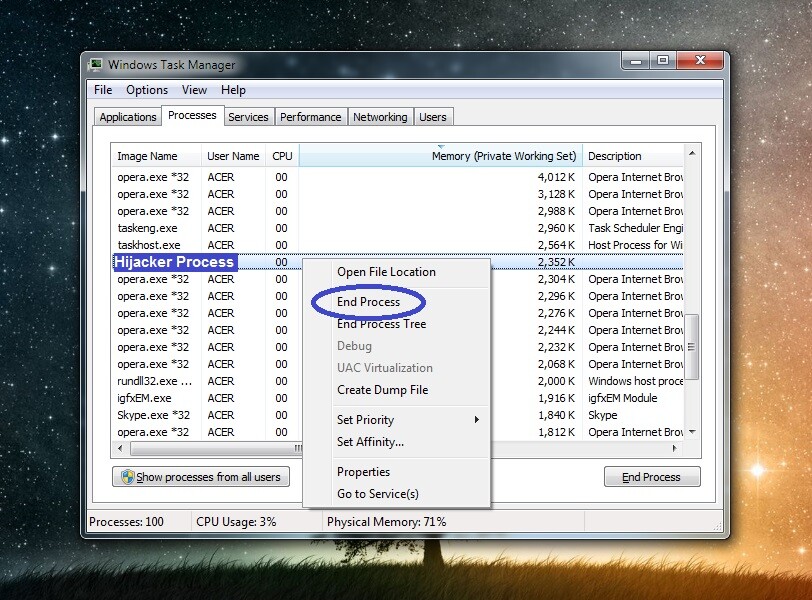
If the processes you suspected of being linked to the Trojan turns out to be malicious, right-click it again and click the End process option. After that, delete the Location folder of that process along with everything that’s stored in it.
Step 3
For the next steps, the computer must stay in Safe Mode in order to prevent Diet.exe from re-launching any of the processes you stopped in Step 2.
Step 4
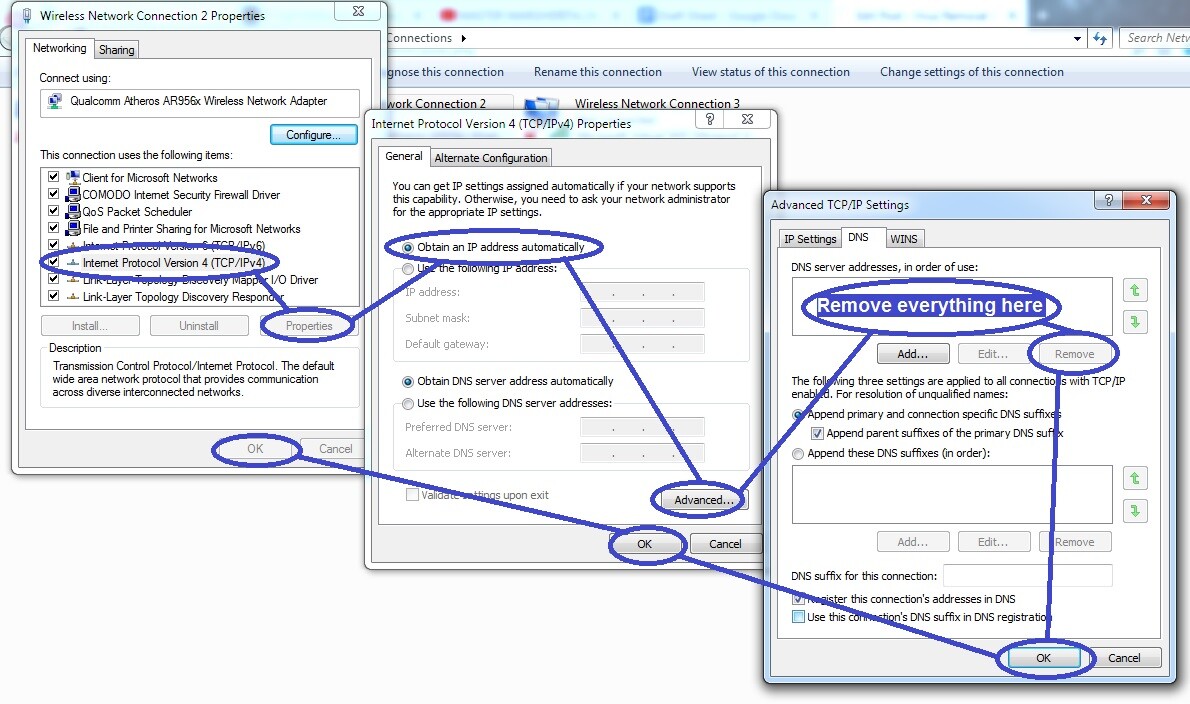
Press Winkey (the key that’s to the left of the left Alt button) + R, type ncpa.cpl, and hit Enter. Right-click on the icon of the network you normally use, go to Properties, and double-click on Internet Protocol Version 4. Next, check the Obtain an IP address automatically and the Obtain DNS server address automatically options (if they aren’t checked at the moment), and then go to Advanced. There, select the DNS tab, delete anything that may be listed below DNS server addresses, and click OK on everything.
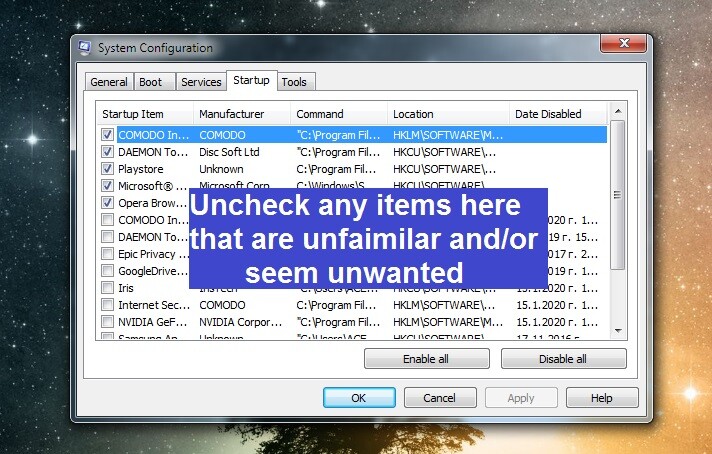
In the Run window that you opened (Winkey + R), type msconfig, press Enter, and click Startup from the top of the System Configuration window. There, uncheck everything that’s shown to be with an unknown manufacturer or that you don’t recognize and/or thing is suspicious and then click OK.
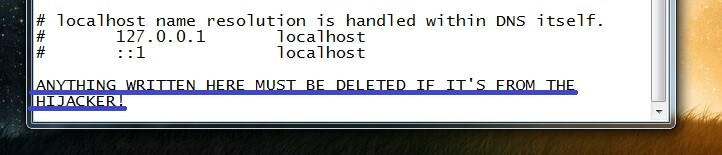
Once again go to the Run window, copy-paste this line in the search field notepad %windir%/system32/Drivers/etc/hosts, hit Enter again, and look at the bottom of the file that shows up. If you see there any strange IP addresses, you must send them to us down in the comments. We will soon get back to you with a reply, informing you whether those IPs need to be removed from the file.
Step 5
While performing this step, be sure to only delete Registry items that you are certain are from Diet.exe. When in doubt about anything, it’s best to ask us in the comments, because if you delete something that you aren’t supposed to, you may end up damaging the system.
You must first start the Registry Editor – search for its executable named regedit.exe in the Start Menu and select it from the search results. Then click Yes when your Admin permission is required and the Editor will open. When it does, go to the Edit menu and then to Find. In the Find box, type Diet.exe, and perform the search. Only one search result will get shown at a time, so after you delete the first Diet.exe item, search for more such items to delete them too.
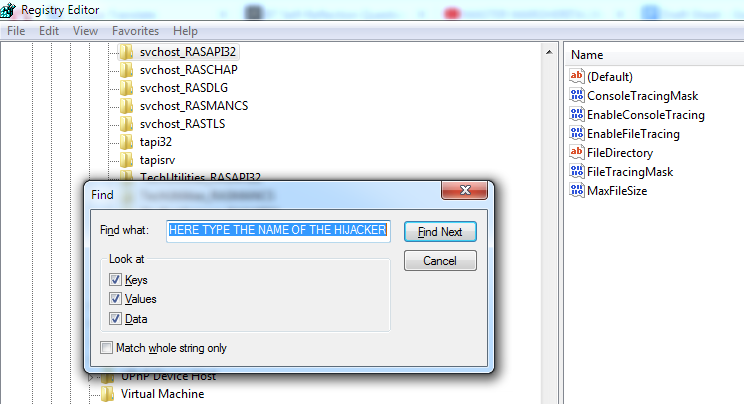
Once all results for Diet.exe have been deleted, go to the next Registry directories (use the left panel of the Editor) and there look for randomly-named items with names similar to this “43t9fu983gj9834jf8938jef9843tu398fj98w“, and if you find anything like that, tell us about it in the comments section, and we will tell you if that item(s) must be removed.
- HKEY_CURRENT_USER/Software
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Step 6
In some cases, Trojan infections like Diet.exe can get too deep inside the system, create too many rogue files, and alter too many settings for a manual removal to be feasible. In such instances, it’s a good idea to either bring the machine to an IT professional or to use a removal tool that can perform a thorough clean-up of your computer, finding and deleting every last bit of malware data. Contacting and bringing your computer to a professional can take time, and we assume that many of you need to have their computers fixed and Diet.exe removed from them ASAP. For this reason, one thing we can recommend to you here is to use the powerful anti-malware tool included in the guide above as a means of cleaning your computer. The tool will scan your entire system, find whatever malware data and settings are left in it, and eradicate them for you.

Leave a Reply