*Source of claim SH can remove it.
Eternity Ransomware
Security professionals are warning web users about a recently detected threat called Eternity Ransomware. Eternity Ransomware operates as a ransomware cryptovirus and has the ability to encrypt the files that you store on your computer without your knowledge.
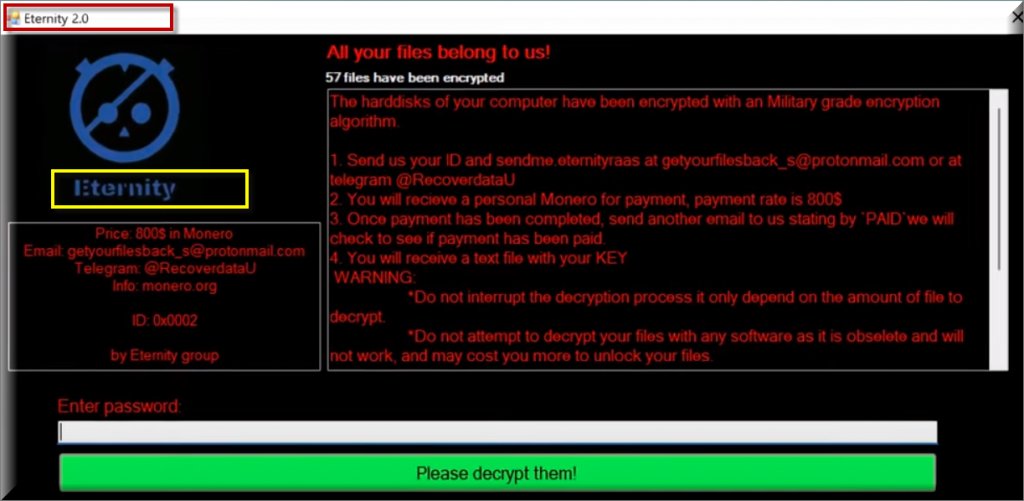
Eternity Ransomware uses an advanced algorithm and then place a ransom note on your screen which is asks you to pay a ransom for the decryption of the locked data. Like most ransomware representatives, Eternity Ransomware can do that without any symptoms. Therefore the number of victims who are suddenly greeted by a scary ransom notification on their screens, generated by this malware, is rapidly growing. What’s more, the people behind the infection use a whole arsenal of sneaky methods and different transmitters that oftentimes look harmless and legitimate and can easily mislead anyone about their true nature and purpose.
The Eternity Ransomware virus
It is really important that you detect and safely remove the Eternity Ransomware virus from your computer before you do anything else. This is because, if the Eternity Ransomware virus is active on your PC, you may not be able to use your computer normally and create new files on it.
Furthermore, you may also not be able to safely connect your backup sources or other devices in order to use them for the recovery of your data. And it goes without saying that it can be a dreadful feeling to lose access to your personal images, videos, audio collections, documents, archives and other important file.
If you are reading this because your system has been secretly compromised by this cryptovirus, then you most probably need some help in order to handle the attack and the nasty consequences that may follow. That’s why, on this page, we have prepared some useful information about the alternatives you can choose from in case that Eternity Ransomware has taken your valuable data hostage, as well as a detailed guide that can help you remove the harmful code from your system.
The Eternity Ransomware file encryption
Once a threat like the Eternity Ransomware file attacks your computer, you basically have to be prepared to deal with the unscrupulous hackers behind the infection. The hackers behind the Eternity Ransomware file encryption typically won’t hesitate to extort money from you in every possible way.
And this means that they aren’t above using threatening messages, false promises, fake data-recovery tools and more. They may display a scary ransom message on your screen, threaten you with tight deadlines, ask a ridiculous amount of money or Bitcoin and promise to send you a special decryption key which is stored on their servers – as long as you do what they demand of you.
Some hackers may even offer you to test-decrypt a couple of files in order to convince you that they have a working decryption solution in their hands, again, with the intention of making you send them the required amount of ransom money. Letting your panic take over your rational decisions, however, won’t do you any good. Moreover, there is absolutely no guarantee about the successful recovery of your files because even if you fulfill all of the ransom demands, the hackers can always disappear without sending you anything in return. That’s why trying to ignore their blackmailing tactics and opting for potential alternatives, such as the ones in the removal guide below, is a much more logical decision.
SUMMARY:
*Source of claim SH can remove it.
Remove Eternity Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Eternity Ransomware files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!



Leave a Comment