FlexInterval
FlexInterval is a type of software that can infect most popular browsers such as Chrome and Safari. Then, FlexInterval proceeds to adjust some of the browser settings, which is why it’s better known as a browser hijacker. These adjustments oftentimes include replacing the default search engine with a new one, as well as setting a new browser homepage.

And on top of that, users are often subjected to frequent page redirects that can either take place in the same tab or can result in new tabs and browser windows. The sponsored web locations that FlexInterval may redirect you to typically sell some type of product or service. So, in a sense, browser hijackers like Ib search, Yahoo Search are mainly used as advertising tools. Hence, also why this piece of software has likely filled your screen with all sorts of banners, popups, in-text links and other such online ads.
FlexInterval for Mac
FlexInterval for Mac can also engage in recording your browsing activities. For instance, FlexInterval for Mac can track your history and log the type of content you interact with. This information is then normally used to optimize the flow of ads and make those appearing on your screen more relevant to you.
And while this activity may sound relatively harmless and benign, it’s often completely uncalled for. Moreover, most people never knowingly agreed to have a browser hijacker operating in their system, so they would hardly be too happy to know about this process. This, as well as the annoying ads, is a fairly solid reason to want to remove FlexInterval from your Mac computer once and for all. And we happen to have just the thing for that – below is a detailed removal guide that will walk you through the steps necessary to delete FlexInterval and all of its components.
What is FlexInterval?
If you are wondering whether FlexInterval is dangerous to you – it isn’t. FlexInterval cannot directly harm your system in any way, but it can lead to some rather unpleasant developments. For one, as a result of its activity, your computer may be significantly slowed down. Furthermore, this hijacker’s activity could potentially interfere with the work of other applications that you use, making them freeze up or even crash. This is especially true for your browser, which can become overloaded with all the numerous ads that are being generated on its screen.
The Flex Interval App
Another question users have about the FlexInterval app is where it came from. The FlexInterval app and others like it are normally distributed with the help of program bundles. And you are most likely to have downloaded one yourself from some torrent site or similar platform where software is available for free download. There are, of course, also other means of distribution such as spam emails and other advertising programs that you may have already had on your computer. But program bundles are by far the most common. And the good news is that if you customize the setup of your newly downloaded program and pay attention to the installation steps, you may very well be able to prevent browser hijackers like FlexInterval from ever entering your system henceforth.
SUMMARY:
| Name | FlexInterval |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Detection Tool |
Remove FlexInterval Mac

The first thing you need to do is to Quit Safari (if it is opened). If you have trouble closing it normally, you may need to Force Quit Safari:
You can choose the Apple menu and click on Force Quit.
Alternatively you can simultaneously press ⌘ (the Command key situated next to the space bar), Option (the key right next to it) and Escape (the key located at the upper left corner of your keyboard).
If you have done it right a dialog box titled Force Quit Applications will open up.
In this new dialog window select Safari, then press the Force Quit button, then confirm with Force Quit again.
Close the dialog box/window.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Start Activity Monitor by opening up Finder, then proceed to ![]()
Once there, look at all the processes: if you believe any of them are hijacking your results, or are part of the problem, highlight the process with your mouse, then click the “i” button at the top. This will open up the following box:

Now click on Sample at the bottom:
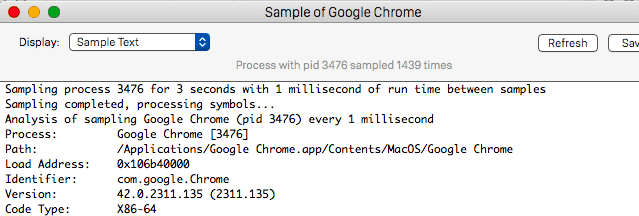
Do this for all processes you believe are part of the threat, and run any suspicious files in our online virus scanner, then delete the malicious files:


The next step is to safely launch Safari again. Press and hold the Shift key while relaunching Safari. This will prevent Safari’s previously opened pages from loading again. Once Safari is opened up, you can release the Shift key.
On the off chance that you are still having trouble with scripts interrupting the closing of unwanted pages in Safari, you may need to take some additional measures.
First, Force Quit Safari again.
Now if you are using a Wi-Fi connection turn it off by selecting Wi-Fi off in you Mac’s Menu. If you are using a cable internet (Ethernet connection), disconnect the Ethernet cable.

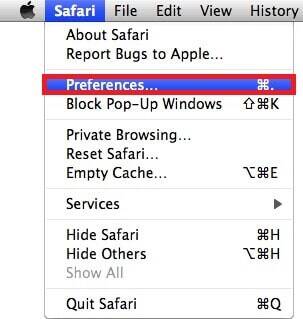
Re-Launch Safari but don’t forget to press and hold the Shift button while doing it, so no previous pages can be opened up. Now, Click on Preferences in the Safari menu,
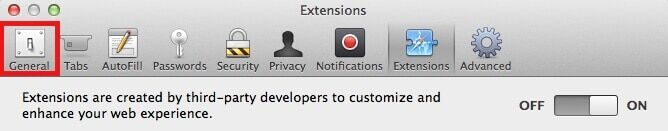
and then again on the Extensions tab,

Select and Uninstall any extensions that you don’t recognize by clicking on the Uninstall button. If you are not sure and don’t want to take any risks you can safely uninstall all extensions, none are required for normal system operation.
![]()
The threat has likely infected all of your browsers. The instructions below need to be applied for all browsers you are using.
Again select Preferences in the Safari Menu, but this time click on the Privacy tab,

Now click on Remove All Website Data, confirm with Remove Now. Keep in mind that after you do this all stored website data will be deleted. You will need to sign-in again for all websites that require any form of authentication.
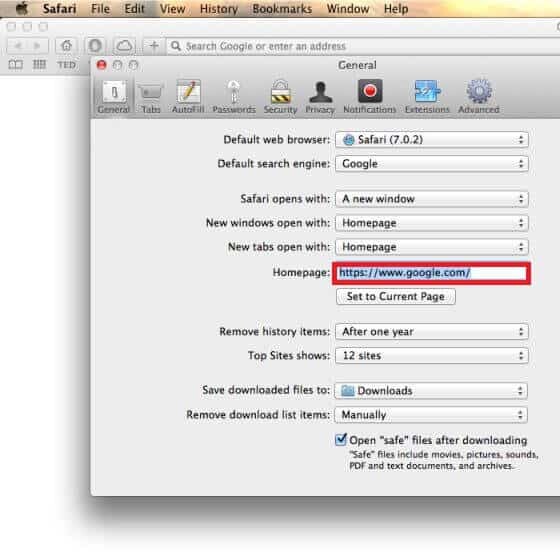
Still in the Preferences menu, hit the General tab
Check if your Homepage is the one you have selected, if not change it to whatever you prefer.
Select the History menu this time, and click on Clear History. This way you will prevent accidentally opening a problematic web page again.
![]() How to Remove FlexInterval From Firefox in OSX:
How to Remove FlexInterval From Firefox in OSX:
Open Firefox, click on ![]() (top right) ——-> Add-ons. Hit Extensions next.
(top right) ——-> Add-ons. Hit Extensions next.

The problem should be lurking somewhere around here – Remove it. Then Refresh Your Firefox Settings.
![]() How to Remove FlexInterval From Chrome in OSX:
How to Remove FlexInterval From Chrome in OSX:
Start Chrome, click ![]() —–>More Tools —–> Extensions. There, find the malware and select
—–>More Tools —–> Extensions. There, find the malware and select ![]() .
.
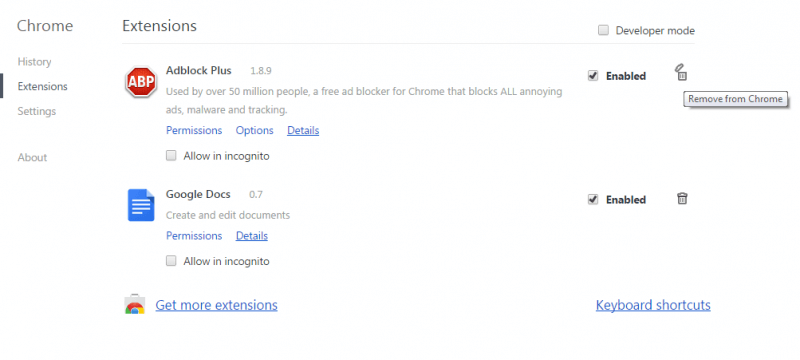
Click ![]() again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply