HsHarada
HsHarada is a ransomware infection that has been programmed to encrypt user files and keep them locked for ransom. The victims of HsHarada are typically asked to transfer some money to a cryptocurrency account in order to obtain a decryption key for their encrypted files. The following paragraphs will help you learn all about the specifics of HsHarada and the methods that you can use to deal with it. This malicious program is one of the worst cyber threats you can ever encounter because it belongs to the notorious ransomware family. It is very difficult to remove a ransomware from your computer, not only because it can hide really well but also because reversing the consequences of its attack may not always be possible. As a result, many experts are having trouble deleting the virus and restoring the encrypted files from the infected computer. We, however, will share with you our removal guide and our tips for free file recovery with the idea to help you remove HsHarada and get back some of your data. Perhaps our guide and our article will help you manage this terrible virus successfully.
The HsHarada virus
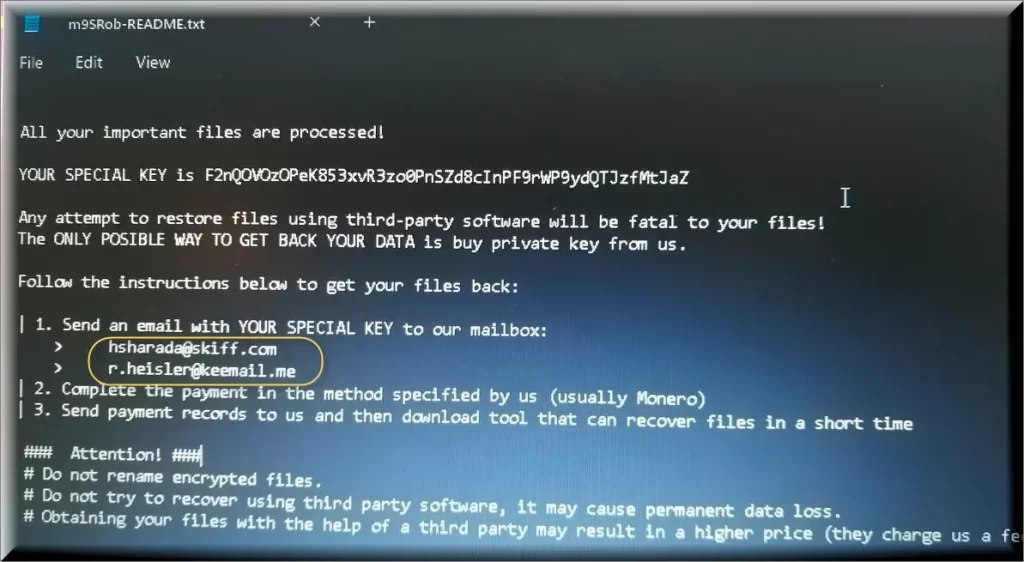
The HsHarada virus is a file-encrypting member of the Ransomware group that is aimed at encrypting user data and keeping it hostage for ransom. The HsHarada virus, like GREEDYFATHER performs its attack by completing a list of all the files that are in use at the moment and adding a different file-extension to them. After all the listed files have been encoded, the ransomware displays an extremely disturbing ransom warning on the screen of its victims. Usually, this warning contains ransom requests, a deadline for the ransom payment and some additional threats that if no payment is released, the encrypted files will be lost forever. Probably, the most prudent way to act after receiving the ransom notification is to wait until you’ve researched the available alternatives that do not involve paying ransom.
The HsHarada file encryption
The HsHarada file encryption is a process where regular user files become encoded and cannot be accessed without a decryption key. The HsHarada file encryption is a stealthy process and visible symptoms of it can hardly be observed. Any files that are encrypted with HsHarada Ransomware will have a random 6 character alpha-numerical extension appended to the end of the encrypted data filename and typically will leave ransom notes which include apparently the same [random 6 character]-README.txt but actually a “hard-coded 6 character string” as part of its name
In the event of an infection of this sort, it is very difficult to tell you what to do. Perhaps there is no appropriate response, nonetheless, the removal guide we have included in this article can always be used to help you remove the infection if you don’t want to pay the ransom to the hackers. Unfortunately, the restoration of your encrypted data cannot be guaranteed no matter what you do. Still, we believe that seeking out alternative solutions is still better than sponsoring some anonymous hackers. In reality, however, preventing Ransomware is the only effective anti-Ransomware treatment. For that, you have to surf the web carefully, install a reliable anti-malware tool that could detect and prevent infections of this type while they’re still in progress and create external backups of all the files that you don’t want to lose.
SUMMARY:
| Name | HsHarada |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
Remove HsHarada Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt HsHarada files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment