I Am A Professional Hacker
“I Am A Professional Hacker” is a harmful malicious script that is capable of running a wide range of dangerous processes on your machine. “I Am A Professional Hacker” falls into the category of Trojan horse viruses and can lead to very serious damage.
If some strange and disturbing spam e-mails have been flooding your inbox lately, telling you about a hidden Trojan horse infection present in your computer and demanding that you pay a certain amount of money to the person who has sent them, then stay with us on this page until the end of this post in order to learn what the best course of action is in such a situation.
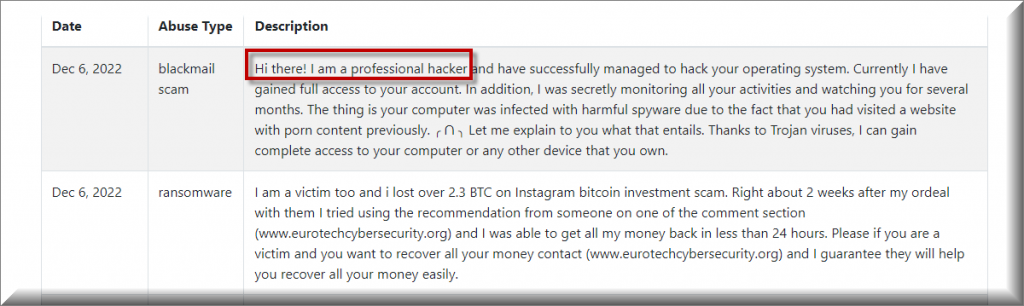
Many of our users reported to us about an ongoing email spam with the following message:
Subject: Your personal data has leaked due to suspected harmful activities.
Hi there! I am a professional hacker and have successfully managed to
hack your operating system. Currently I have gained full access to
your account. In addition, I was secretly monitoring all your
activities and watching you for several months. The thing is your
computer was infected with harmful spyware due to the fact that you
had visited a website with porn content previously. Let me
explain to you what that entails. Thanks to Trojan viruses, I can gain
complete access to your computer or any other device that you own. It
means that I can see absolutely everything in your screen and switch
on the camera as well as microphone at any point of time without your
permission. In addition, I can also access and see your confidential
information as well as your emails and chat messages. You may be
wondering why your antivirus cannot detect my malicious software. Let
me break it down for you: I am using harmful software that is
driver-based, which refreshes its signatures on 4-hourly basis, hence
your antivirus is unable to detect it presence. I have made a video
compilation, which shows on the left side the scenes of you happily
masturbating, while on the right side it demonstrates the video you
were watching at that moment… All I need is just to share this
video to all email addresses and messenger contacts of people you are
in communication with on your device or PC. Furthermore, I can also
make public all your emails and chat history. I believe you would
definitely want to avoid this from happening. Here is what you need to
do – transfer the Bitcoin equivalent of 850 USD to my Bitcoin account
(that is rather a simple process, which you can check out online in
case if you don’t know how to do that). Below is my bitcoin account
information (Bitcoin wallet): 12nEVuGNtRFMVjeVmLtD4nt2sHX68S47yH Once
the required amount is transferred to my account, I will proceed with
deleting all those videos and disappear from your life once and for
all. Kindly ensure you complete the abovementioned transfer within 50
hours (2 days +). I will receive a notification right after you open
this email, hence the countdown will start. Trust me, I am very
careful, calculative and never make mistakes. If I discover that you
shared this message with others, I will straight away proceed with
making your private videos public. Good luck!
First, we need to tell you that such phishing e-mails and blackmailing messages aren’t something to be trusted. In most of the cases, the people behind them do not actually have access to your computer or data and are simply trying to scare you in hopes that you’d fall for the bait and send them the demanded sum. Of course, it may not always be easy to spot the scam at first – the crooks behind them can be very creative and convincing in their money-extortion tactics. However, unless you have actual solid proof that there may indeed be a virus in your computer, there shouldn’t be a real reason to worry at the sight of such messages.
SUMMARY:
| Name | I Am A Professional Hacker |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Trojans may cause all sorts of disruptions on your computer but they may also operate silently, without showing any symptoms. |
| Distribution Method | Clickbait ads, spam letters, pirated programs and more. |
| Detection Tool |
Please follow all the steps below in order to remove “I Am A Professional Hacker”!
How to remove I Am A Professional Hacker
- First, click the Start Menu on your Windows PC.
- Type Programs and Settings in the Start Menu, click the first item, and find “I Am A Professional Hacker” in the programs list that would show up.
- Select “I Am A Professional Hacker” from the list and click on Uninstall.
- Follow the steps in the removal wizard.
Read more…
What we suggest you do first is, check the list of programs that are presently installed on the infected device and uninstall any rogue software that you find there:
- From the Start Menu, navigate to Control Panel ->>> Programs and Features ->>> Uninstall a Program.
- Next, carefully search for unfamiliar programs or programs that have been installed recently and could be related to “I Am A Professional Hacker”.
- If you find any of the programs suspicious then uninstall them if they turn out to be linked to “I Am A Professional Hacker”.
- If a notification appears on your screen when you try to uninstall a specific questionable program prompting you to just alter it or repair it, make sure you choose NO and complete the steps from the removal wizard.
Remove “I Am A Professional Hacker” from Chrome
- Click on the three dots in the right upper corner
- Go to more tools
- Now select extensions
- Remove the “I Am A Professional Hacker” extension
Read more…
- Once you open Chrome, click on the three-dots icon to open the browser’s menu, go to More Tools/ More Options, and then to Extensions.
- Again, find the items on that page that could be linked to “I Am A Professional Hacker” and/or that might be causing problems in the browser and delete them.
- Afterwards, go to this folder: Computer > C: > Users > *Your User Account* > App Data > Local > Google > Chrome > User Data. In there, you will find a folder named Default – you should change its name to Backup Default and restart the PC.
- Note that the App Data folder is normally hidden so you’d have to first make the hidden files and folders on your PC visible before you can access it.
How to get rid of “I Am A Professional Hacker” on FF/Edge/etc.
- Open the browser and select the menu icon.
- From the menu, click on the Add-ons button.
- Look for the “I Am A Professional Hacker” extension
- Get rid of “I Am A Professional Hacker” by removing it from extensions
Read more…
If using Firefox:
- Open Firefox
- Select the three parallel lines menu and go to Add-ons.
- Find the unwanted add-on and delete it from the browser – if there is more than one unwanted extension, remove all of them.
- Go to the browser menu again, select Options, and then click on Home from the sidebar to the left.
- Check the current addresses for the browser’s homepage and new-tab page and change them if they are currently set to address(es) you don’t know or trust.
If using MS Edge/IE:
- Start Edge
- Select the browser menu and go to Extensions.
- Find and uninstall any Edge extensions that look undesirable and unwanted.
- Select Settings from the browser menu and click on Appearance.
- Check the new-tab page address of the browser and if it has been modified by “”I Am A Professional Hacker”” or another unwanted app, change it to an address that you’d want to be the browser’s new-tab page.
How to Delete “I Am A Professional Hacker”
- Open task manager
- Look for the “I Am A Professional Hacker” process
- Select it and click on End task
- Open the file location to delete “I Am A Professional Hacker”
Read more…
- Access the Task Manager by pressing together the Ctrl + Alt + Del keys and then selecting Task Manager.
- Open Processes and there try to find a process with the name of the unwanted software. If you find it, select it with the right button of the mouse and click on the Open File Location option.
- If you don’t see a “”I Am A Professional Hacker”” process in the Task Manager, look for another suspicious process with an unusual name. It is likely that the unwanted process would be using lots of RAM and CPU so pay attention to the number of resources each process is using.
- Tip: If you think you have singled out the unwanted process but are not sure, it’s always a good idea to search for information about it on the Internet – this should give you a general idea if the process is a legitimate one from a regular program or from your OS or if it is indeed likely linked to the adware.
- If you find another suspicious process, open its File Location too.
- Once in the File Location folder for the suspicious process, start testing all of the files that are stored there by dragging them to our free online scanner available below.
- Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared. - If the scanner finds malware in any of the files, return to the Processes tab in the Task Manager, select the suspected process, and then select the End Process option to quit it.
- Go back to the folder where the files of that process are located and delete all of the files that you are allowed to delete. If all files get deleted normally, exit the folder and delete that folder too. If one or more of the files showed an error message when you tried to delete them, leave them for now and return to try to delete them again once you’ve completed the rest of the guide.
How to Uninstall “I Am A Professional Hacker”
- Click on the home button
- Search for Startup Apps
- Look for “I Am A Professional Hacker” in there
- Uninstall “I Am A Professional Hacker” from Startup Apps by turning it off
Read more…
- Now you need to carefully search for and uninstall any “I Am A Professional Hacker”. racing-related entries from the Registry. The easiest way to do this is to open the Registry Editor app (type Regedit in the windows search field and press Enter) and then open a Find dialog (CTRL+F key combination) where you have to type the name of the threat.
- Perform a search by clicking on the Find Next button and delete any detected results. Do this as many times as needed until no more results are found.
- After that, to ensure that there are no remaining entries lined to “I Am A Professional Hacker” in the Registry, go manually to the following directories and delete them:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/Random
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/Random
One of the main problems related to the Trojan horse infections is that their symptoms may be inconsistent and in many instances, there may be no visible infection indications whatsoever. This is part of the reason why the e-mail scammers oftentimes choose to threaten their victims with this precise form of malware. Even if you see no infection symptoms, this doesn’t necessarily mean that no Trojan is present on your computer.
Due to this, it’s important to check your system for potential malware hazards of this type if you receive any such blackmailing messages. The best way you can do that is through the use of some reliable software security program like an antivirus or an anti-malware tool. On this page, you can find such a program – it is linked in the removal guide below. The removal guide itself is focused on a specific Trojan horse threat named “I Am A Professional Hacker”. If you detect this or another similar infection in your machine, you can use the guide to remove it. The anti-malware tool can also automatically remove the virus in case you don’t want to use the manual steps.
Even if you are one of the few unlucky users who do indeed have a Trojan like “I Am A Professional Hacker” in their machines, the best course of action is to try to remove the malware yourself rather than send your money to the blackmailers who are harassing you. There’s no telling whether or not the virus would go away if you pay them – for all you know, it may get activated right after you issue the payment, in which case you would have simply wasted your money. Therefore, we have made sure to offer you an alternative solution in the form of the guide you’ll see below and we advise you to use it as well as the removal tool that’s in it if you have any suspicions about the presence of “I Am A Professional Hacker” or another Trojan in your computer.

Leave a Comment