Idsync.rlcdn.com
Idsync.rlcdn.com is a rogue page that installs a browser-hijacking component inside the browsers of Windows computers. Idsync.rlcdn.com can get installed on the computer with the help of a file-bundle or if the user mistakenly interacts with a fake browser notification.

In most cases, the presence of the hijacker on the computer becomes apparent right away. Changes to the browser’s homepage, search engine, and new-tab page as well as aggressive automatic page-redirects and ad pop-ups are all common symptoms triggered by a lot of browser hijackers.
Any browser, including highly-secure ones such as Chrome or Firefox, could get targeted and hijacked by a rogue page/software component such as Idsync.rlcdn.com, Findquide, Home Search Design . The good news is that this doesn’t necessarily mean that there’s any direct danger for your PC or the data you’ve stored on it. Unlike real malware threats (Ransomware, Trojans, Rootkits, etc.) the primary goal of Idsync.rlcdn.com and other similar hijackers is centered around advertising. Typically, browser hijackers are tools used by online marketers to gather telemetry data about as many users as possible so that they could later supply them with more relevant ads. The problem arises when the data-gathering and advertising activities start to become overly intrusive and aggressive to the point where the user’s regular browsing experience starts getting interrupted. At that point, deleting the hijacker from your browser becomes a necessity. Fortunately, though sometimes apps like Idsync.rlcdn.com can be tricky to remove, we will show you two very effective ways (one automatic and one manual) of eliminating this browser hijacker.
Potential dangers associated with browser hijackers
Even if the goal of this undesirable software is not to harm your system or data, there are still certain risks associated with it which mustn’t be underestimated. The main security problem related to browser hijackers in general is that the advertising materials they tend to spam within the users’ browsers may not always be what they seem. In addition to interrupting your regular browsing experience, an app like Idsync.rlcdn.com could also end up redirecting you to scam sites and phishing pages designed to steal personal data such as credit and debit card numbers. In more extreme cases, you may even be lured into downloading actual malware onto your computer that could cause all sorts of damage. For instance, if you accidentally end up allowing a Ransomware virus to be downloaded on your PC, the malicious program could lock all your files and ask for a payment to release them. A Trojan, on the other hand, could take over your entire system and force the computer to perform various harmful tasks such as sending out spam messages or participating in DDoS attacks.
Unfortunately, a rogue app like Idsync.rlcdn.com can be the initial cause of all those, and many more, problems even if, in and of itself, it is not a dangerous software capable of harming your system. This is the reason we recommend deleting this hijacker ASAP. The guide and the professional removal tool you’ll find below will allow you to get rid of the undesirable software and restore your browser (or browsers) to its regular state.
SUMMARY:
| Name | Idsync.rlcdn.com |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Idsync.rlcdn.com Malware
To try and remove Idsync.rlcdn.com quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Idsync.rlcdn.com extension (as well as any other unfamiliar ones).
- Remove Idsync.rlcdn.com by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Idsync.rlcdn.com and any other suspicious items.
If this does not work as described please follow our more detailed Idsync.rlcdn.com removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Idsync.rlcdn.com from Internet Explorer:
Remove Idsync.rlcdn.com from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
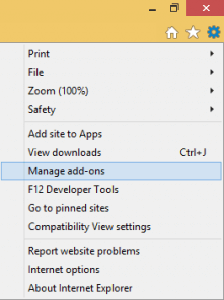
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove Idsync.rlcdn.com from Firefox:
Remove Idsync.rlcdn.com from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove Idsync.rlcdn.com from Chrome:
Remove Idsync.rlcdn.com from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
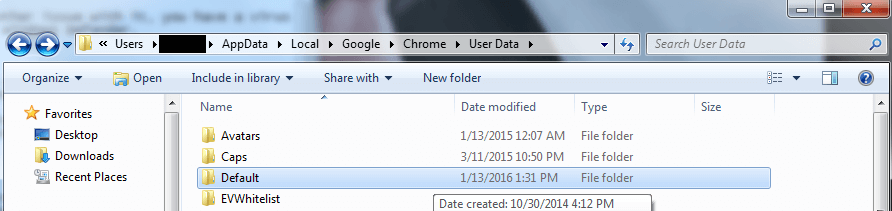
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply