The Kellyfight.com Malware
Kellyfight.com Malware is an advanced Trojan horse infection which can attack your system and harm it in a really bad way. Kellyfight.com Malware is currently distributed with the help of various stealthy techniques and carriers that typically look harmless but, in fact, contain the virus and use different tricks to make you interact with them in order to get you infected.
Some of the usual carriers of the infection may appear in the form of emails from friends, colleagues or institutions, or as attachments and links, while others may pop-up on your screen as ads, different good-looking offers, intriguing messages or even as software update requests which appear to be legitimate but are fake and misleading.
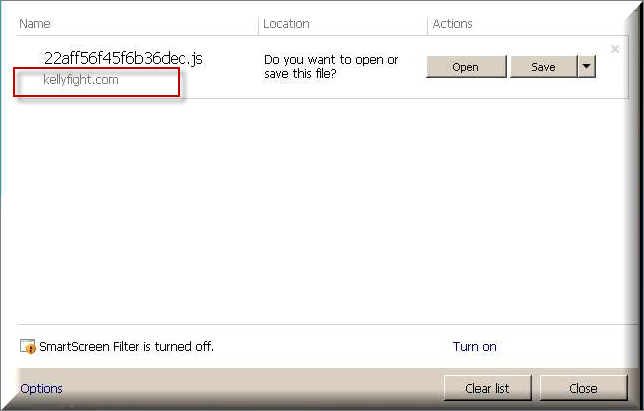
Unfortunately, without the help of a professional antivirus program, it is often very difficult to protect yourself and your computer because there is always a chance of clicking on something misleading while you are browsing the web. If you have any suspicion that Kellyfight.com Malware or Energy.exe might have somehow sneaked inside your computer, then the first thing we suggest you do is run a full scan with a reliable security software program.
In case that your security program is unable to detect the Trojan or cannot remove it effectively, you can always run a second scan with the malware removal program that you can find right below. Alternatively, you can also use a manual removal guide to detect and remove the infection on your own, but before you delete anything, we still advise you to check your system with a trusted scanner because many Trojan infections have the ability to mimic regular system processes and files and can easily trick you into deleting something that’s an essential part of your system.
Deleting something wrong will not only help the malware remain inside the computer but it may also harm your operating system in a really bad way. That’s why our best suggestion is to use the instructions that you will find below with care. Still, make sure you don’t lose time before you eliminate Kellyfight.com Malware because you may face some really unpleasant malicious consequences if you don’t deal with it on time.
Kellyfight.com Malware may gain control over your entire system and may mess with all the data that you keep there. It is very possible that you may suddenly get all of your personal files corrupted or your HDD formatted without any warnings or indications. Another possible action which this Trojan horse may perform is to secretly spy on you and collect information about your online accounts, banking details, passwords and other sensitive details, which can automatically be send to the remote servers of people with malicious intentions.
Additionally, the Trojan may launch some unauthorized background activities which may be aimed at creating security holes in your system. In this way, the malware can secretly weaken the security of your system and insert other viruses including ransomware, worms or rootkits. The worst thing is that the victims may not have a clue about any of these activities, at least not until their effects become apparent and start to cause issues.
And this is where the importance of having reliable security software comes into play. A good and regularly updated antivirus program can usually detect potentially dangerous software long before it fulfills its full agenda and can notify you about the dangerous malware so that you can take corresponding actions. In this regard, purchasing a trusted antivirus or anti-malware tool is an investment that can save you from a lot of trouble in the future.
SUMMARY:
| Name | Kellyfight.com Malware |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Usually, there are no visible symptoms, that’s why detecting the Trojan requires a good security tool. |
| Distribution Method | Spam, fake ads, misleading links, malicious emails and attachments, infected installers are among the most common sources. |
| Detection Tool |
Remove Kellyfight.com Malware
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment