Mumpings.com
Mumpings.com acts as a kind of browser extension for most popular browsers including but not limited to Chrome, Firefox and Edge. Mumpings.com primarily aims to expose internet users to various advertising materials and sponsored content.For instance, it will typically fill your browsing program during sessions with popups, in-text links, box messages and banners that promote various products and services. Furthermore, your browser may begin to trigger so-called page redirects and just randomly send you to various web addresses that are trying to sell you something.This is made possible thanks to ad-generating components that programs like this install in the host browser. And also thanks to this, this application can also gain access to some of the browser’s configurations and changes these to its benefit.
Mumpings.com Virus
Most commonly users notice changes made to the default search engine, which is often replaced with a new one. And that new search engine may also be set as the new browser homepage, too. This is done for the purposes of popularizing a given web site and boosting its traffic count. But in addition to that, a custom search engine like the Mumpings.com virus also allows the display of more sponsored search results. The above rather intrusive behavior is what has earned this particular class of software, like the Mumpings.com virus the name of browser hijackers. And what’s particularly annoying about all such pieces of programming is that they don’t really offer you an obvious removal option. As you know, most software has an ‘Uninstall’ button readily available.
That’s not the case here. Hence, we’ve prepared a free removal guide for you to make use of – just below the current post.
What is Mumpings.com?
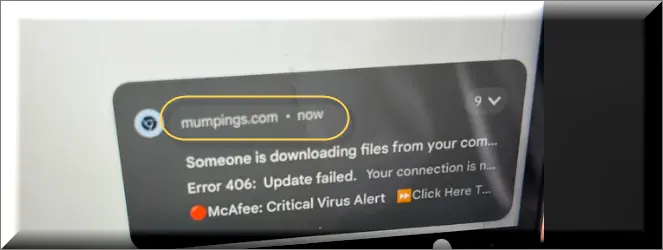
Mumpings.com is a browser hijacker virus that poses significant security risks through deceptive tactics, primarily targeting push notification permissions. This malicious scam site utilizes notification spam techniques and browser hijacking strategies to trick users into clicking on misleading prompts. By presenting false claims like “Someone is downloading files from your computer” or “Error 406: Update failed…,” Mumpings.com aims to deceive users into granting push notification permissions. Once granted, these notifications can inundate users with unwanted advertisements and redirect them to potentially harmful websites. To mitigate the risks associated with Mumpings.com and similar threats, users should exercise caution when encountering suspicious websites, refrain from clicking on misleading prompts, and regularly update their browsers and security software to prevent infection.
Mumpings.com pop ups
Mumpings.com pop up, often raises concerns about its nature, with users questioning if it’s a virus. In reality, Mumpings.com pop-up isn’t designed to directly harm systems, unlike typical viruses. Browser hijackers, including the Mumpings.com virus, Ssj4.io, Find It Pro Remove and iStart Search Bar, lack the capacity for direct system damage; their primary purpose revolves around ad exposure and revenue generation rather than causing direct harm. While they don’t possess the destructive capabilities of traditional viruses, these hijackers disrupt user experiences through intrusive ads and redirects. Although not inherently harmful, their intrusive nature and resource-intensive processes impact system performance, causing disturbances like sluggishness and browser crashes, prompting users to seek removal to restore a smoother browsing experience.
Mumpings.com on Chrome
On a more sinister note, the content you may be exposed to isn’t guaranteed to be 100% safe and secure either. Much on the contrary actually, oftentimes the sites that need promotion from a browser hijacker, like Mumpings.com on Chrome, usually have something sketchy about them to begin with. And in some cases that might even mean association with malware such as ransomware, rootkits, Trojan horse viruses, etc. So with that in mind, we wouldn’t recommend allowing Mumpings.com on Chrome to remain for much longer on your PC. It’s best to not risk contaminating your system and simply see to the prompt and thorough removal of this software instead.
Mumpings
Mumpings operates as a browser hijacker aiming to expose users to ads, generating revenue for its developers through user clicks. However, these background processes can strain computer resources, impacting overall performance. Mumpings’s intrusive activities might result in reduced battery life, especially for laptop users, and cause system sluggishness, browser freezes, and crashes. While its primary goal isn’t to cause direct harm like malware, its resource-intensive processes significantly affect user experience and system stability. The continuous background operations undertaken by Mumpings to display ads for revenue generation can exhaust system resources, leading to performance issues that impact regular browsing activities and compromise overall system functionality.
SUMMARY:
| Name | Mumpings.com |
| Type | Adware/Browser Hijacker |
| Detection Tool |
How to Remove Mumpings.com
To try and remove Mumpings.com quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Mumpings.com extension (as well as any other unfamiliar ones).
- Remove Mumpings.com by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Mumpings.com and any other suspicious items.
If this does not work as described please follow our more detailed Mumpings.com removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Mumpings.com app and kill its processes
Uninstall the Mumpings.com app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Mumpings.com. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Mumpings.com, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Mumpings.com.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Mumpings.com changes made to different system settings
Undo Mumpings.com changes made to different system settings
It’s possible that Mumpings.com has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Mumpings.com from your browsers
Remove Mumpings.com from your browsers
- Delete Mumpings.com from Chrome
- Delete Mumpings.com from Firefox
- Delete Mumpings.com from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Comment