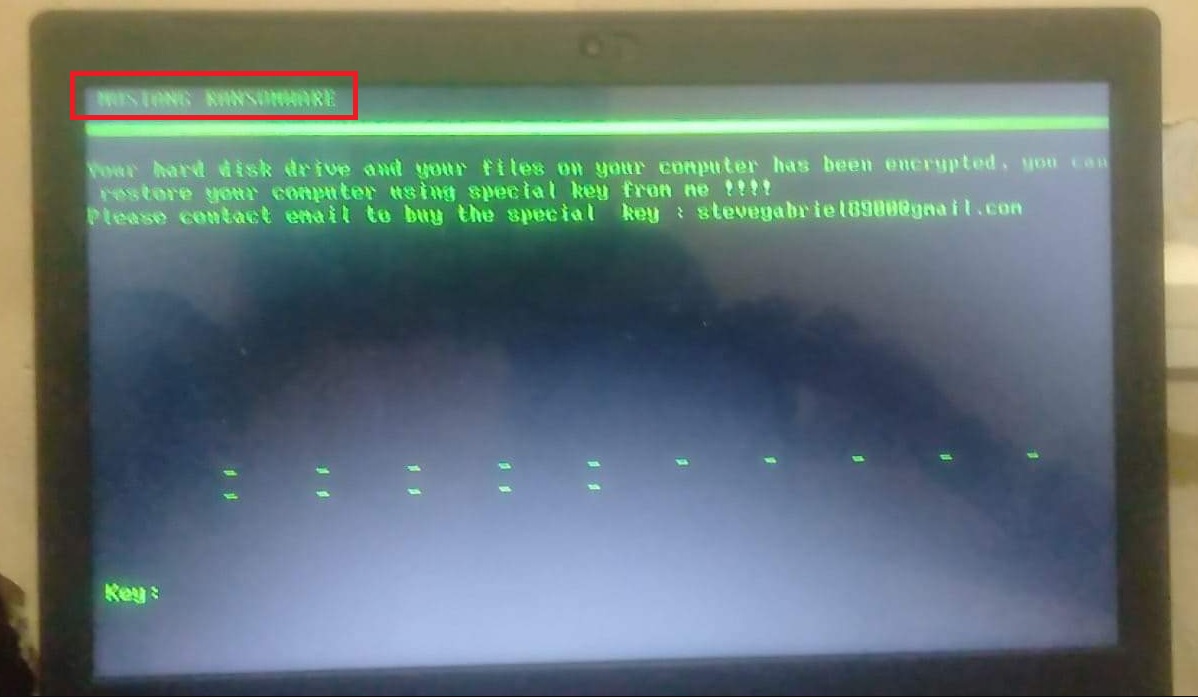
The Mustang Ransomware
Mustang Ransomware is a virus programmed to make your files unusable by locking them via data encryption. After Mustang Ransomware encrypts your files, it will inform you about a payment you are supposed to make in order to regain access to the unavailable data.
An attack from such a virus can be a particularly serious issue for users who haven’t made sure to create periodical backups of their valuable data. A data backup is the best defense you can have against a Ransomware attack since it will keep safe copies of the files you don’t want to lose on another device or inside a cloud storage, where the Ransomware cannot reach them. However, since most users don’t have the habit of backing up their files, Ransomware threats such as Mustang Ransomware tend to be very successful.
Another reason for the high success rates of these viruses is their stealthiness and ability to not be noticed. Most people don’t even get the chance to stop the virus before it has finished with its encryption process. There are very few noticeable symptoms and those symptoms aren’t exclusive to this kind of malware. Usually, the only infection sign before the files are locked is the increased use of virtual memory and CPU. This could cause slowdowns in the system during the encryption, but such slowdowns due to excessive use of system resources could be triggered by all kinds of processes, many of which aren’t harmful. Therefore, most Ransomware attacks go unnoticed, at least until the virus is ready with the encryption and shows the user the demands of the hackers who control it.
The Mustang Ransomware virus
The Mustang Ransomware virus is a virus program recognized as file-encrypting Ransomware that blocks personal user files via data encryption. The Mustang Ransomware virus creates a special key that can release the files and sends it to the hackers who want their victim to pay for it.
If you are a victim of Mustang Ransomware or other virus such as Gujd or Guid, and are currently being harassed by a ransom message on your screen that is telling you to pay a certain sum for the access key for your files, then be sure to first carefully assess the situation and consider your options before you do anything.
Even if you have the required sum readily available and you are willing to pay it if that would bring your files back, we advise you to hold off that action. Know that the payment won’t guarantee the recovery of anything. Yes, you may get the needed key for your files, but this is only a possibility and not something that is guaranteed. Therefore, it is better to first try the options that won’t require you to send money to some anonymous hackers.
The Mustang Ransomware file encryption
The Mustang Ransomware file encryption is an almost unbreakable algorithm used for making the files of the attacked victims inaccessible. The Mustang Ransomware file encryption has a unique key for each infected computer, which key is required to set the encrypted files free.
If you don’t want to risk your money by sending it to the criminals while not knowing if you’d receive the access key for your files in return, try out the guide we have prepared for our readers and posted below, and follow the instructions in order to remove Mustang Ransomware and hopefully bring some of the locked files back.
SUMMARY:
| Name | Mustang Ransomware |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Mustang Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Mustang Ransomware files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply