Nokoyawa
Nokoyawa is a stealthy Ransomware infection that asks you to pay a ransom in order to liberate your files from its encryption. When you get infected, Nokoyawa secretly encodes all your most valuable information and generates a ransom-demanding message on the screen.
If you want to avoid the ransom payment that the hackers behind Nokoyawa, Ygvb, Dwqs demand, the information we’ve prepared here can assist you to cope with this danger. Moreover, our “How to Remove” team is devoted to assisting users like you deal with such malware, and here you will learn how to efficiently remove the Ransomware, and protect your machine in the future.
The Nokoyawa virus
The Nokoyawa virus is a dangerous infection which is also known as a cryptovirus. Eliminating the Nokoyawa virus is of utmost importance if you want to be able to safely use your computer in the future.
With this in mind, in the next lines, we will share with you our tested and detailed removal instructions. We will also provide you with some alternatives to the ransom payment, which may assist you to get back your information without giving the criminals your money. So, once you remove the infection, we’ll point you to the guide’s file recovery section, hoping you’ll find it useful. But let’s first say a few words about this new cyber threat before we move on, so you can better understand the malware you’re up against.
Ransomware infections usually happen when web users click on some malicious content. Such content is often distributed through spam emails with infected attachments, misleading messages, harmful links, torrents, and questionable downloads. Sadly, there are no noticeable signs of either the infection, or the file encryption process, so the Ransomware generally runs unnoticed until it shows itself on the victim’s screen through a ransom note.
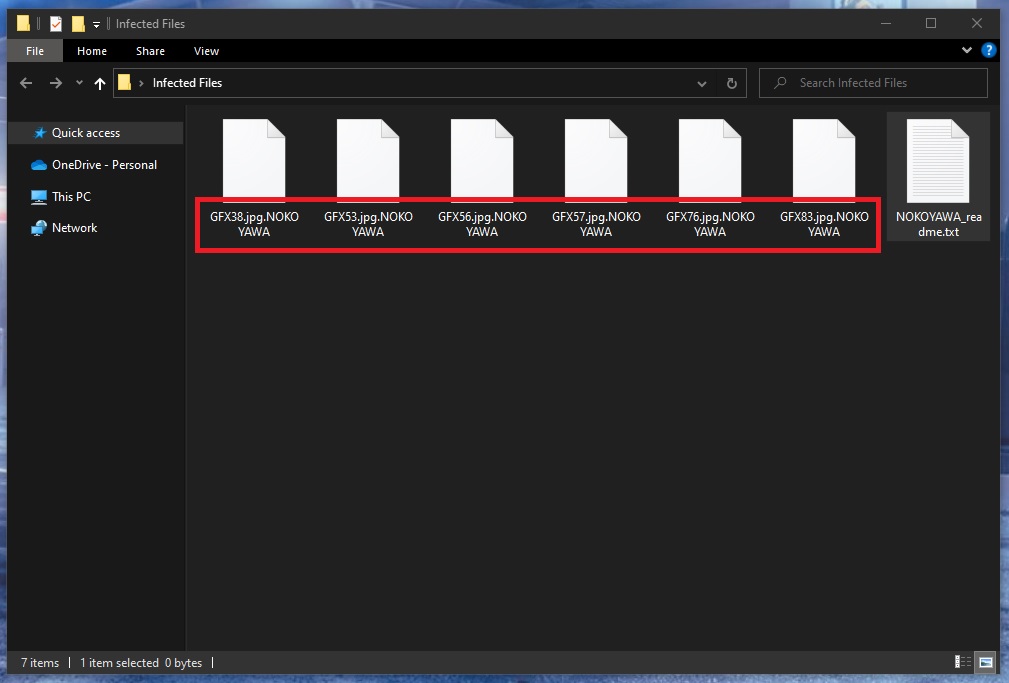
The Nokoyawa file encryption
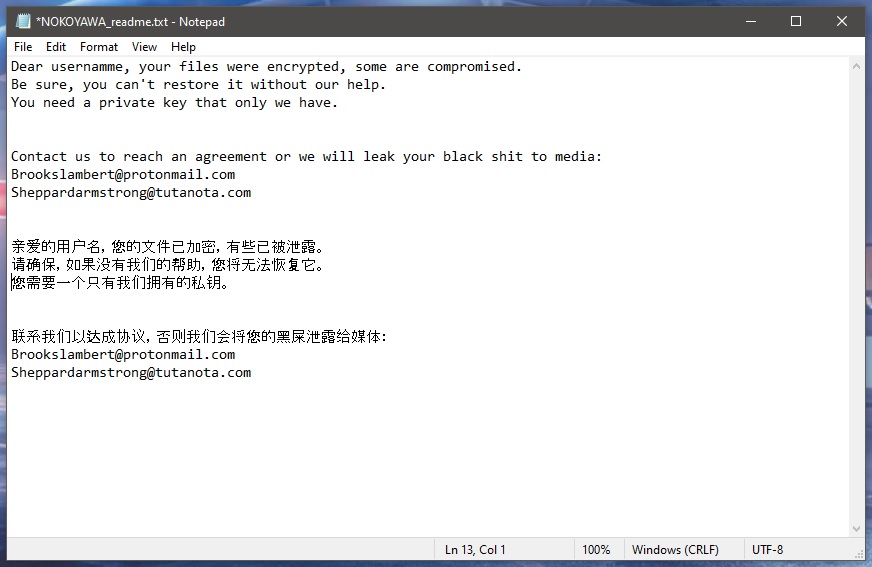
The Nokoyawa file encryption is a complex code that can only be reversed with a special decryption key. Unfortunately, the decryption key for the Nokoyawa file encryption is kept with the crooks, and they would send it to you in return for a substantial sum, payable in BitCoins.
They provide specific directions on how to pay the BitCoins within a ransom note displayed on your screen instantly after the encryption of the file has been completed. Very often, the hackers threaten to destroy the decryption key completely if the payment is delayed or not made. Alternatively, they may threaten to double the amount requested for the ransom to make the victims pay quickly. However, you shouldn’t fall for these manipulative tricks, and you should always make sure to give yourself enough time to figure out what course of action would be best in your case.
Leading security experts, including our “How to remove” team, share the opinion that it is not a good idea to send money to the crooks behind Ransomware. For one, many victims burn their money this way only to get a key that doesn’t work, and that is utterly ineffective. Secondly, many users never get a key for decryption at all.
Therefore, we encourage you to try to restore your files through other means and explore some alternatives in the removal guide below. You can recover your information from personal backup copies stored on an external drive or on a cloud, if you have any such backups. That’s why creating regular backups, and keeping them on external storage is the smartest, and simplest way to protect yourself from data loss caused by a Ransomware attack. However, to remove the virus, and prevent future infections, you would still need an adequate antivirus software with specialized anti-ransomware features, as well as a well-maintained, and frequently updated system.
SUMMARY:
| Name | Nokoyawa |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Nokoyawa Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Nokoyawa files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment