OneDriveStandaloneUpdater.exe
OneDriveStandaloneUpdater.exe is a Trojan threat that can collect personal or professional information about the victim through espionage. In many cases, OneDriveStandaloneUpdater.exe can keep tack of the victim’s keystrokes on their keyboard or hack into their webcam and microphone to record them.
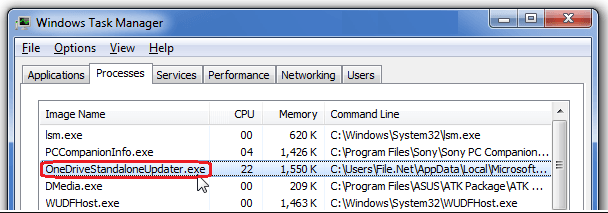
OneDriveStandaloneUpdater.exe is a legitimate Microsoft Windows process connected to OneDrive, which is located in: C:\Users\Username\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe. Oftentimes, these kinds of processes are the target of a Malware attack and can be infected without users realizing.
Trojan Horses are very widespread cyber threats that could be found all over the web. What you’ll learn from this article is how to combat a recently released Trojan named OneDriveStandaloneUpdater.exe and how to safely remove its traces from your system. Below. you will find a removal guide dedicated to that and a professional system scanner tool that you can use to scan your entire computer. Sadly, most Trojan-based infections are extremely subtle, making them extremely difficult to spot on your own. Therefore, you may really need the assistance of security software to correctly detect and eliminate the hidden Trojan code from your system.
The effects of a Trojan’s attack can be unpredictable. This malware might be spying on you and it may try to gain information about your banking details, or some sensitive information about your professional or personal life. This ability of the Trojans is one of the most disturbing ones as the hackers who are in control may get their hands on a lot of details that can later be used for cyber-crimes such as theft of identity, banking frauds, theft of online accounts, etc.
A Trojan-based program such as OneDriveStandaloneUpdater.exe can take over your system and use its resources for various crimes and other sketchy activities. For instance, it can turn the infected machine into an automated bot that can be used to distribute spam or mine cryptocurrencies. Another way the computer can be abused is by making it part of a botnet and using it to execute DDoS attacks. In addition, a Trojan may also be used to transport malware of all kinds and insert it inside the system, which means that you may become a victim of Ransomware, Spyware, and other additional viruses without even coming close to their transmitters.
Trojans such as OneDriveStandaloneUpdater.exe could be distributed via torrents, illegal web pages, all kinds of spam (unwanted emails and attachments), malvertisements, free software bundles, random on-screen notifications, and more. It takes one click to get infected but it takes much more than that to remove the malicious software once it has nested itself inside the system. In the attached Removal Guide below, however, you will find detailed instructions that can help you eliminate OneDriveStandaloneUpdater.exe if you carefully follow them.
And if you don’t want to encounter such threats again, please, be careful when you go online and be sure to keep your computer safe by protecting it with reliable antivirus software. Other good methods of prevention include updating your OS regularly and applying all the needed updates to the other software installed there. It is also important to be mindful of your browsing habits and to pick your download sources carefully. Do not download anything from random links and sketchy websites and avoid installing unnecessary software applications if you don’t need them or if you’re unsure if they are reliable.
SUMMARY:
| Name | OneDriveStandaloneUpdater.exe |
| Type | Trojan |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove OneDriveStandaloneUpdater.exe Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Reply