Onlinehome.us
Onlinehome.us is a scam virus that is specifically aimed at Mac-compatible programs. Onlinehome.us tends to integrate with popular browsers and spam them with annoying online ads.
An aggressive stream of pop-ups, banners and different redirect links is something that you most probably wouldn’t like to experience while browsing the web but since you are reading the information on this page, we assume that this is actually what has brought you here. You most probably have noticed some strange changes in your Chrome, Firefox, Safari (or whatever browser you are currently using as your main one), as well as a stream of nagging commercial messages on every web page that you visit.
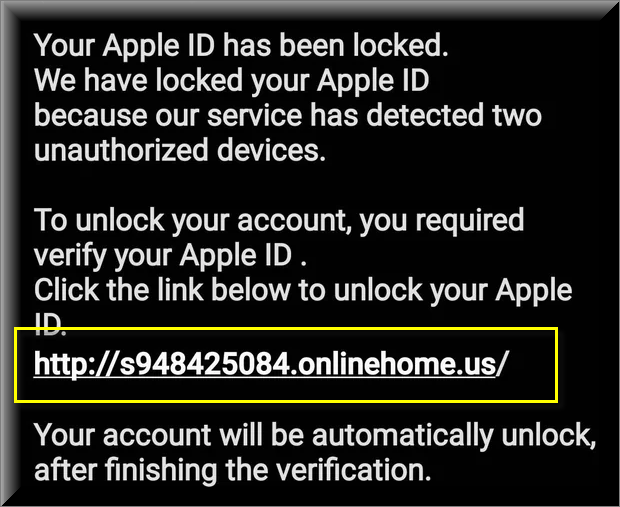
Many of our Mac users reported to us about an ongoing scam with the following messages:
Your Apple ID has been locked.
We have locked your Apple ID because our service has detected two unauthorized devices. To unlock your account, you required verify your Apple ID.
Click the link below to unlock your Apple ID.
http://s948425084.onlinehome.us/
Your account will be automatically unlock, after finishing the verification.
Copyright © 2023 Apple Distribution International, Hollyhill Industrial Estate, Hollyhill, Cork, Irlande.
All rights reserved.
You may also have noticed some unwelcome changes inside your homepage or in the main search engine. In addition, an automatic page-redirect service which has started to reroute most of your searches to specific websites may have been added to your browser. Before you assume that you might have been attacked by some nasty virus (or a stealthy malware like a Trojan, spyware or some nasty Ransomware), however, let us tell you that the most probable source of these changes is an app called Onlinehome.us.
Onlinehome.us for Mac
Onlinehome.us for Mac is a new addition to the browser hijacker family and is a common source of browser irritation for many. Onlinehome.us for Mac installs ad-generating components on users’ computers and thus is responsible for the many ads you’ve been seeing.
So, in case the nagging messages displayed on your screen say something along the lines of “sponsored by Onlinehome.us” or “generated by Onlinehome.us”, then this is exactly the application that you are dealing with. And if you want to remove the aggressive ads, you will have to uninstall the imposed browser modifications from your main browsing program.
What is Onlinehome.us?
Onlinehome.us is malware of a virus and it is generally considered harmful. Onlinehome.us will corrupt your system or damage the files stored on it. Scammers are sending the fake and phishing text to potential victims with a link to a fake Apple website that steals account credentials, personal, and financial information.
We need to warn you, though, that dealing with a representative of the browser hijacker category may not be easy. The main reason why most web users don’t want to have such software on their computers is because apps like these typically tend to get in the way rather than improve the web browsing experience. They normally try to make you interact with as many ads, pop-ups and banners as possible and to redirect you to specific sponsored sites, the clicks on which generate income for the creators of the browser hijacker. In many cases, aggressive advertising methods such as Pay-Per-Click are incorporated in the activity of applications like Onlinehome.us and they dictate their behavior. Therefore, no matter how much you try to close the sponsored ads or to remove them from the screen, they will pop-up again and again unless you uninstall the software that is generating them.
The Onlinehome.us app
Recognized as malicious, software like the Onlinehome.us app should be approached with caution. There are certain dangers indirectly associated with the activities that the Onlinehome.us app may engage in.
The browsing disturbance and the potentially unwanted browser changes are definitely an unpleasant effect of having an application like Onlinehome.us on your PC. However, what’s worse is that a major risk for your safety may come from clicking on the unfamiliar links and random messages generated by the hijacker as those may redirect you to dangerous web locations. This is because the ads and the offers that are shown on your screen by the hijacker typically don’t go through any quality control. They may originate from sites with a questionable reputation or ones with weak security as well as from all kinds of sketchy sources, which, in turn, opens room for the distribution of different security hazards, including nasty infections like Trojans, rootkits and even Ransomware viruses.
Unfortunately, it is almost impossible to distinguish normal ads from malicious ones. That’s why it is best to stay away from such random messages and get rid of any software that is spamming you with them.
SUMMARY:
| Name | Onlinehome.us |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Your screen may get spammed with various aggressive ads, pop-ups and redirects. |
| Distribution Method | Spam messages, free software bundles, automatic installers, ads, torrents, freeware and shareware sites. |
| Detection Tool |
Remove Onlinehome.us Scam

More information on SpyHunter, steps to uninstall, EULA, Threat Assessment Criteria, and Privacy Policy.
The first thing you need to do is to Quit Safari (if it is opened). If you have trouble closing it normally, you may need to Force Quit Safari:
You can choose the Apple menu and click on Force Quit.
Alternatively you can simultaneously press ⌘ (the Command key situated next to the space bar), Option (the key right next to it) and Escape (the key located at the upper left corner of your keyboard).
If you have done it right a dialog box titled Force Quit Applications will open up.
In this new dialog window select Safari, then press the Force Quit button, then confirm with Force Quit again.
Close the dialog box/window.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
More information on SpyHunter, steps to uninstall, EULA, Threat Assessment Criteria, and Privacy Policy.
Start Activity Monitor by opening up Finder, then proceed to ![]()
Once there, look at all the processes: if you believe any of them are hijacking your results, or are part of the problem, highlight the process with your mouse, then click the “i” button at the top. This will open up the following box:

Now click on Sample at the bottom:
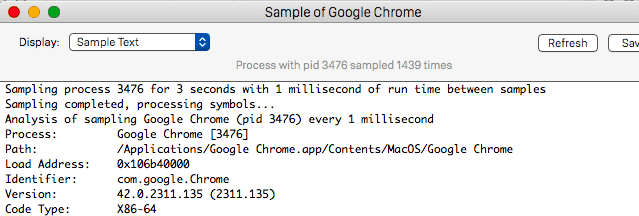
Do this for all processes you believe are part of the threat, and run any suspicious files in our online virus scanner, then delete the malicious files:


The next step is to safely launch Safari again. Press and hold the Shift key while relaunching Safari. This will prevent Safari’s previously opened pages from loading again. Once Safari is opened up, you can release the Shift key.
On the off chance that you are still having trouble with scripts interrupting the closing of unwanted pages in Safari, you may need to take some additional measures.
First, Force Quit Safari again.
Now if you are using a Wi-Fi connection turn it off by selecting Wi-Fi off in you Mac’s Menu. If you are using a cable internet (Ethernet connection), disconnect the Ethernet cable.

Re-Launch Safari but don’t forget to press and hold the Shift button while doing it, so no previous pages can be opened up. Now, Click on Preferences in the Safari menu,
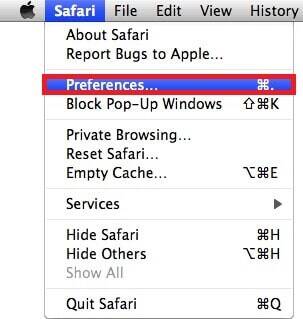
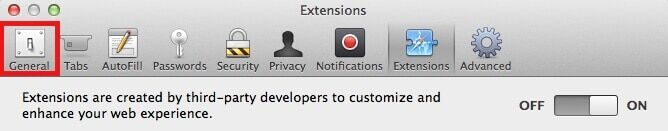
and then again on the Extensions tab,

Select and Uninstall any extensions that you don’t recognize by clicking on the Uninstall button. If you are not sure and don’t want to take any risks you can safely uninstall all extensions, none are required for normal system operation.
![]()
The threat has likely infected all of your browsers. The instructions below need to be applied for all browsers you are using.
Again select Preferences in the Safari Menu, but this time click on the Privacy tab,

Now click on Remove All Website Data, confirm with Remove Now. Keep in mind that after you do this all stored website data will be deleted. You will need to sign-in again for all websites that require any form of authentication.
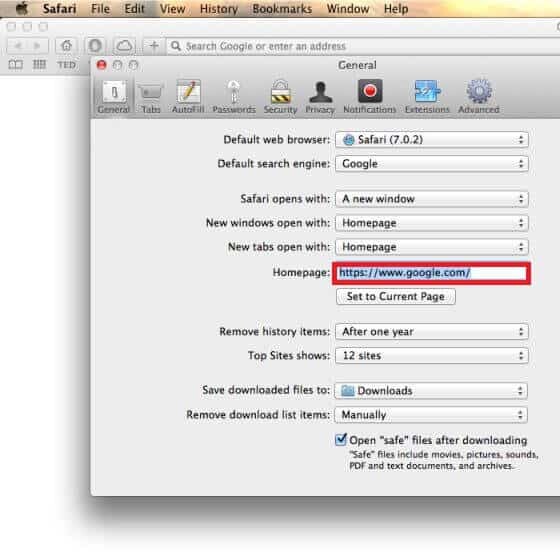
Still in the Preferences menu, hit the General tab
Check if your Homepage is the one you have selected, if not change it to whatever you prefer.
Select the History menu this time, and click on Clear History. This way you will prevent accidentally opening a problematic web page again.
![]() How to Remove Onlinehome.us From Firefox in OSX:
How to Remove Onlinehome.us From Firefox in OSX:
Open Firefox, click on ![]() (top right) ——-> Add-ons. Hit Extensions next.
(top right) ——-> Add-ons. Hit Extensions next.

The problem should be lurking somewhere around here – Remove it. Then Refresh Your Firefox Settings.
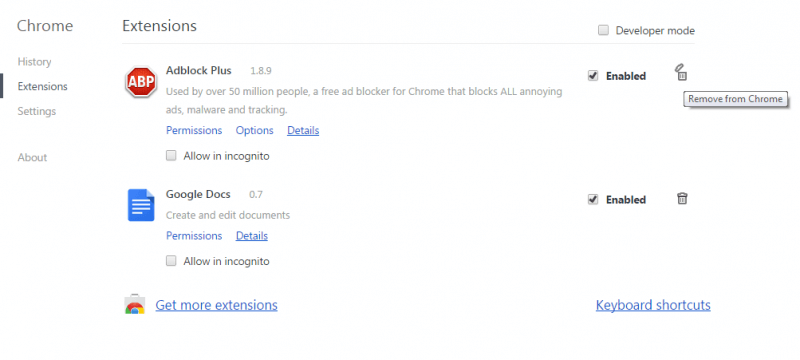
![]() How to Remove Onlinehome.us From Chrome in OSX:
How to Remove Onlinehome.us From Chrome in OSX:
Start Chrome, click ![]() —–>More Tools —–> Extensions. There, find the malware and select
—–>More Tools —–> Extensions. There, find the malware and select ![]() .
.
Click ![]() again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
again, and proceed to Settings —> Search, the fourth tab, select Manage Search Engines. Delete everything but the search engines you normally use. After that Reset Your Chrome Settings.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply