Qdla
Qdla is probably the name of the malware piece that led you to seek our assistance. If you have Qdla in your computer, be sure to read the following information. In order to deal with this infection in the best way possible, you will need to be well acquainted with its capabilities and characteristics.
The Qdla virus
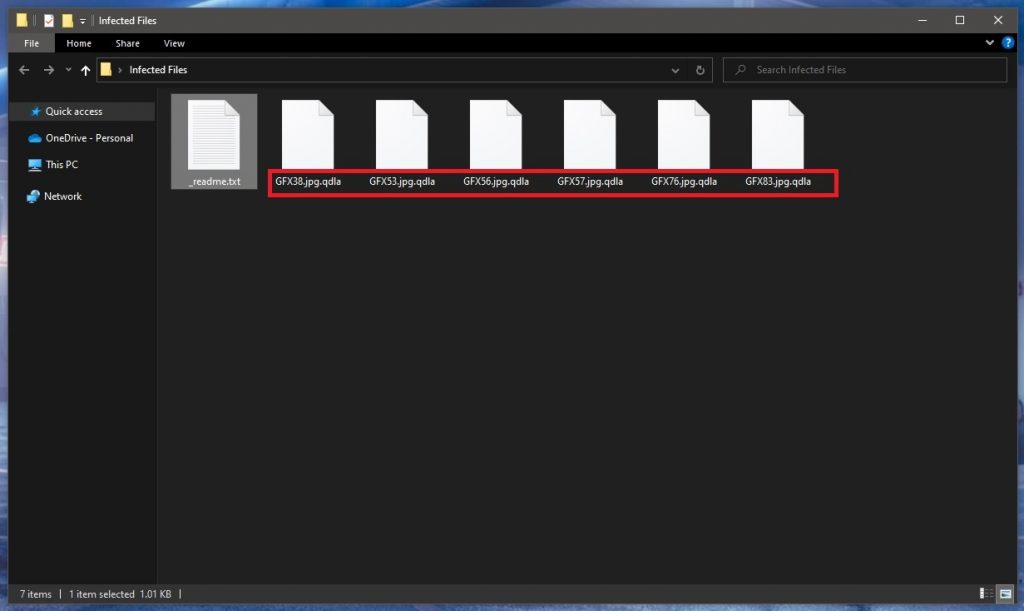
The Qdla virus is a malware program of the Ransomware family, and its target are the files in your PC. Qdla locks those files up through file-encryption, making them inaccessible.
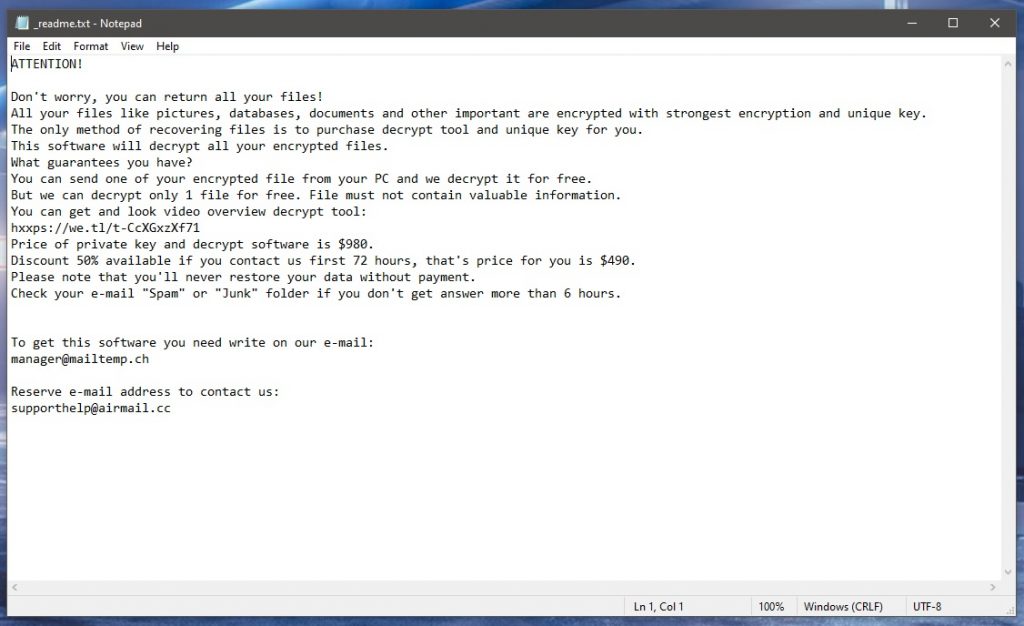
If you have been contaminated by Qdla, Stax or Irfk, and now you are searching for a way to take back your access to the files that it has locked up, you’ve come to the right place. The fact that this malware piece belongs to the Ransomware malicious software class is the very first thing you should learn with regards to this noxious virus. The reason those malicious programs are referred to as Ransomware is due to the fact that they are, in most cases, used for blackmailing the users into paying a ransom, by encrypting their files, and holding them locked until the wanted ransom is paid off. It may sound discouraging, but Ransomware is maybe the most difficult to handle type of malware you may ever get. The unfortunate truth is that even professionals are quite often powerless with regards to dealing with Ransomware.
Even though the odds might not seem to be on your side, we still strongly advise you to keep your calm and read on, for there can still be a way out of this issue. When it comes to potential ways to cope with a Ransomware virus, below you can find a removal manual for this sort of pc virus that we have designed for you. The guide is placed immediately after this article, so go ahead and use it, provided that you have already fallen prey to the awful piece of malware. With some luck, the guide may allow you to unlock your encrypted data files, and remove the computer virus.
The .Qdla file encryption
The .Qdla file encryption is the process responsible for the lockdown on the files. Through the .Qdla file encryption, the hackers are able to extort money from their victims.
These viruses are not like most other kinds of online threats, and that’s likely the reason they’ve evolved into such a major issue. Unfortunately, that is also the main reason there are not many antivirus program tools in existence which might actually handle a Ransomware virus program.
A Ransomware is undoubtedly a malicious program, yet, in general, nothing on the targeted computer gets immediately damaged by this type of programs. Due to this fact, no activity coming from the Ransomware virus is to be deemed sketchy and potentially unwanted enough to alert the antivirus program that the customer might have.
The primary concept behind the file encryption process isn’t to harm any of the user’s data files, but to keep it protected. This sort of processes don’t normally inflict damage upon the affected computer files. It’s just that this innocent method gets turned against the user by the Ransomware.
Typically, there can be several possible signs that may help you notice the ongoing contamination before it’s not too late. Yet, be aware that this is quite often a matter of luck. In some cases, though rather seldom, the warning signs of the contamination may be recognized and the PC virus process – detected inside the Task Manager. The red flags may be unusually increased use of System resources such as storage space, processor power and RAM. In general, if the computer is behaving in a strange way, and you do not know the reason for it, it’s best to check your system by scanning it with some reliable security tool, such as the one we’ve linked in our guide.
SUMMARY:
| Name | Qdla |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Before you begin this guide
Before attempting to remove a Ransomware virus from your PC, there are a couple of important things that you need to bear in mind.
- The first one is that you must make sure to immediately disconnect external hard-drives, phones, tablets, flash memory sticks, or other devices with storage memory from your PC so that their files don’t get targeted by Qdla.
- The next important thing is to disconnect from the Internet on your PC and open this page on another device. If you don’t temporarily shut down your Internet connection, Qdla may attempt to reach out to its creators’ servers and receive new instructions from there that may make removing it that much more difficult.
- We strongly advise against transferring the ransom sum requested by the hackers, but if you are thinking about doing it, then it’s preferable to remove Qdla only after having paid the sum. If you remove the virus first, the chances of getting the decryption key (even if you pay) would be much lower. Of course, after this, you should still delete the Ransomware.
- Last but not least, even if you no longer notice any signs of Qdla, be sure to perform the next steps so as to be sure your system is truly clean.
Remove Qdla Ransomware
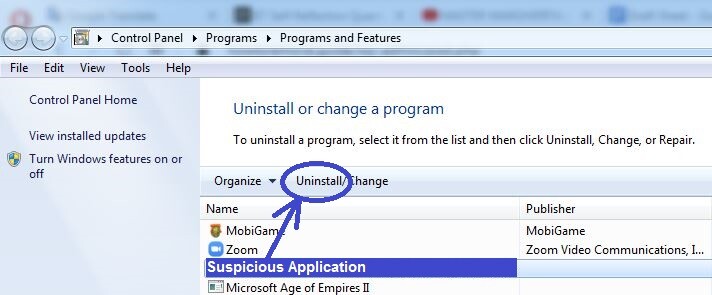
To remove Qdla, your first task is to dispose of the rogue program that infected you with it, after which you should clean your system from malware data and settings.
- Look through the programs installed on your computer looking for a suspicious, recently-installed one that may be linked to the Ransomware, and delete that program.
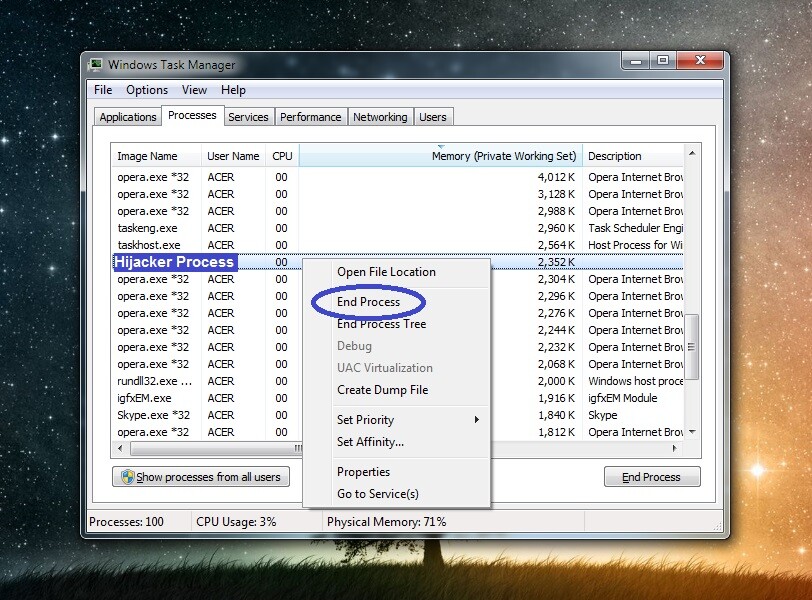
- Start the Task Manager tool and use it to single out and dispose of any rogue malware processes.
- See if there are any malware files left in the system and delete them.
- Find and remove any Ransomware entries from your computer’s Registry to remove Qdla.
For each of those four steps, we’ve provided detailed instructions that are available below – we recommend reading through them before starting the removal process.
Detailed removal instructions
Step 1
To see all the programs currently installed don your computer, open the Start Menu, search in it for the Control Panel, and open the latter. Then go to Uninstall a Program (Programs and Features) and you will see what programs are on your PC. If among them there is a recently-installed one that you are unfamiliar with and/or that has a questionable name and seems suspicious, you should delete it by selecting it from the list, then clicking the Uninstall option at the top, and performing the next removal steps. If, during the uninstallation process, you are given the option to keep data or settings from that program on your PC, refuse that option and ensure everything related to the undesirable program gets erased.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Open the Start Menu, type Task Manager, click the app that shows up, and click Processes. See which processes are using the largest amounts of processing power and virtual memory and if you think that any of them seem suspicious and could be related to Qdla, do the following things to learn more about them and hopefully figure out if they are actual threats:
Open Google and perform a search with the name of the rogue process. If there are results from security sites and forums where experts are warning that the process in question may be malicious, this would likely mean that you should dispose of that process (and its data).
The other method of finding out whether the process is harmful or not is to right-click on it, then click on the Open File Location option, and one by one drag each of the files from that folder to our free malware detector we’ve included below. If it finds malware in one or more of the tested files, this would indicate that the process they are linked to is malicious and must be stopped.


Naturally, if you find out that there’s a malware process running in your system, you should quit it and after that delete the folder where its files are contained (the file location folder).
Step 3
It’s possible Qdla may try to start its rogue processes all over again – boot the computer into Safe Mode to ensure this doesn’t happen.
Step 4
Type “Folder options” in the search bar of the Start Menu, press the Enter key, and when the Folder Options window appears, go to its View section. There, you will see a bunch of options – find the one labelled Show hidden files, folders, and drives, check it, and click on OK.
Next, copy-paste this: “%AppData%” in the Start Menu, press Enter, sort the files in the folder by date, and delete the ones that have been created since the virus infection occurred (including ones created on the day of the infection if you know what day that was).
After that, repeat this with these next three folders:
- %LocalAppData%
- %ProgramData%
- %WinDir%
Finally, open the %Temp% folder in the same way and delete everything that you find in it and not only the most recent data.
Step 5
Using the Start Menu once more, type msconfig in the search field and open the app that shows up. The System Configuration window should appear on your screen – in it, you must select the Startup tab and search the list shown there for items you don’t recognize, ones that you think are suspicious, or ones that are listed as having unknown manufacturers. If you find any such items, uncheck them and click the OK button.
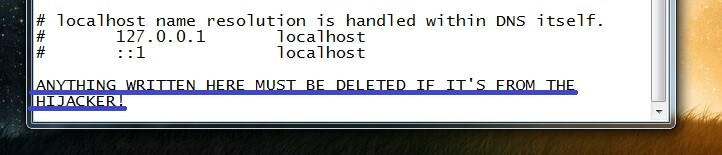
The next thing you must do is go to the C: drive (or the drive where you OS is installed if it’s another one), and then navigate to Windows\System32\drivers\etc. There, you should see a file named Hosts – double-click it and select Notepad if required to choose a program. When you see the file on your screen, check the bottom of its text for any questionable IP addresses that may be written there. If there are such IPs right under the second “Localhost” line, you should send them to use in the comments. We will soon review them and tell you if they are from Qdla and whether you need to clean your Hosts file from them.
Step 6
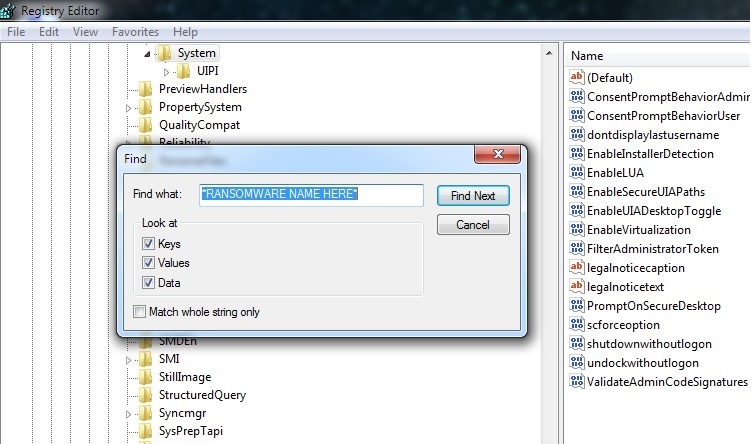
Click the Start Menu icon, type regedit.exe, and open the app with the same name that appears. You may be asked to give your Admin approval to that app in order to enable it to make system changes – click on Yes if this happens.
When you see a window labelled Registry Editor on your screen, click Edit from the top of that window, then click Find, type the Ransomware name in the search box, and select Find Next. Whatever item gets found, you must delete it, and then you must search again for other related items. Make sure that you find and delete all items relate to Qdla from the Registry.
The last thing to do is to check the Registry locations shown below (you can navigate to them using the left panel of the Registry Editor) for entries with long and unusual/random-looking names, similar to this one “9240ur923j9t8u3e90tg840u3902iru30tu4jd8” – if there are such items present in those locations, tell us about them, and wait for our reply rather than directly deleting them.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
If Qdla is still in the system
One thing that may make a virus like Qdla difficult to remove manually is the presence of a secondary piece of malware in the system that is designed to hinder any attempts made towards removing the Ransomware. The way to deal with such a situation is to use a specialized anti-malware tool that can take care of both threats at the same time.
On this page, you can find a powerful malware removal tool capable of simultaneously cleaning your computer of all malware that’s presently inside it. We highly recommend it to users who are in such a predicament, so feel free to try it out if you are interested and think you may need its help.
How to Decrypt Qdla files
To decrypt Qdla files, it’s better to seek out alternative restoration options as opposed to opting for the payment of the ransom. However, to try to decrypt Qdla files with such alternative methods, you must first make sure that the PC is clean from malware.
Here, we once again remind you of the powerful online scanner you can find on this page and on our site – it will help you test any suspicious files that may be in the system so that you’d know to delete them if they turn out to be related to any malware type. Once you’ve cleaned the computer, our recommendation is to check the recovery methods we’ve included and explained in our How to Decrypt Ransomware post – go to it, check out the different variants and try them out to hopefully restore your data without having to pay anything to the blackmailers who have attacked you with Qdla.
Qdla is a dangerous piece of malicious software used by hackers for online blackmailing. The way Qdla operates is by using encryption on the user’s files to lock them and then asking its victim to pay a ransom in order to get the decryption key.
Ransomware is presently a major threat for both regular users and big corporations, organizations, and even governments. Qdla is one of the latest additions to the Ransomware category and, as such, its encryption is highly advanced and there aren’t many ways to release any files that have been locked by it.
If your data has been rendered inaccessible by the Qdla encryption, the first thing you should consider is the subjective value that the locked files have to you. You see, the main issue with viruses like Qdla is the potential for severe data loss of important files. If, however, the malware hasn’t locked any such files on your computer or if anything important that it has managed to encrypt already has backup copies in other locations, the damage this virus could cause would be nullified.
Qdla is a specific type of virus that doesn’t damage the system it attacks, but rather uses encryption to make its victims incapable of gaining access to their most valuable files. Once a file is encrypted by the Qdla virus, no program can open it.
In case this malware has entered your system and has locked some important data for which you don’t have any backups, you would be forced to choose between paying a ransom to the blackmailers or trying to find alternative solutions that may or may not bring your data back. It is, however, important to remember that even if you pay the money that the hackers demand from you, this in a way guarantees the restoration of your files. You need to remind yourself that the people behind Qdla are ruthless cybercriminals whose only goal is to make as much money as possible through their malicious programs. Because of this, you have no reason to believe their promises of providing you with a decryption key once the payment gets transferred to their virtual wallets.
To decrypt Qdla files, it’s best if you try all available options that don’t involve paying a ransom before you consider the latter course of action. Giving the hackers your money in hopes of decrypting Qdla files is risky and often leads to more trouble.
One thing you could try is to seek free decryptor tools for this specific Ransomware. There are many Ransomware decryptors distributed for free, and most of them are developed by respectable security companies. However, note that each decryptor is created for a specific Ransomware, so there’s no guarantee that there would be one for Qdla at the moment you are reading this. In our How to Decrypt Ransomware article that is available on this site, you will find an extensive list of such decryptors. There, you will also find other potential methods of recovering encrypted files that you can also try out.
Obviously, if nothing else works, you can still try the payment option, but make sure to consider the risks associated with it before you decide to go for this course of action.

Leave a Reply