This page was created to help users decrypt Ransomware.
Below we have compiled in several steps the best possible chance you have to recover your files (except for actually paying the criminals). We firmly advise you to not pay the ransom- if you pay it, you simply fund the criminals to create even more advanced ransomware versions.
![]()
Removal
Before you begin restoring your files you need to make sure that the Ransomware program itself has been neutralized. Use the guide you came from to remove it, or it may encrypt your files again.
If you can’t remove the ransomware yourself, we advise you to download SpyHunter.
![]()
Shadow Clone Restoration
The first thing you can try is to restore your files through their shadow copies. We advise you to do this before resorting to decryptors, as it is risk-free, meaning if it fails, your files won’t be deleted by the ransomware. Some especially nasty ransomware variants threaten to delete your files if they detect any sort of tampering.
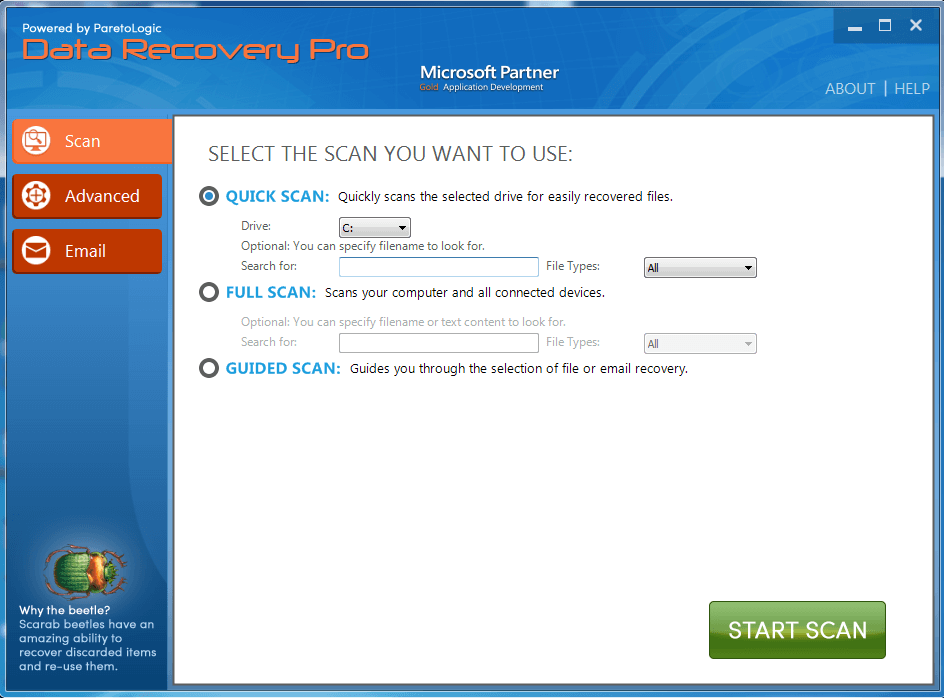
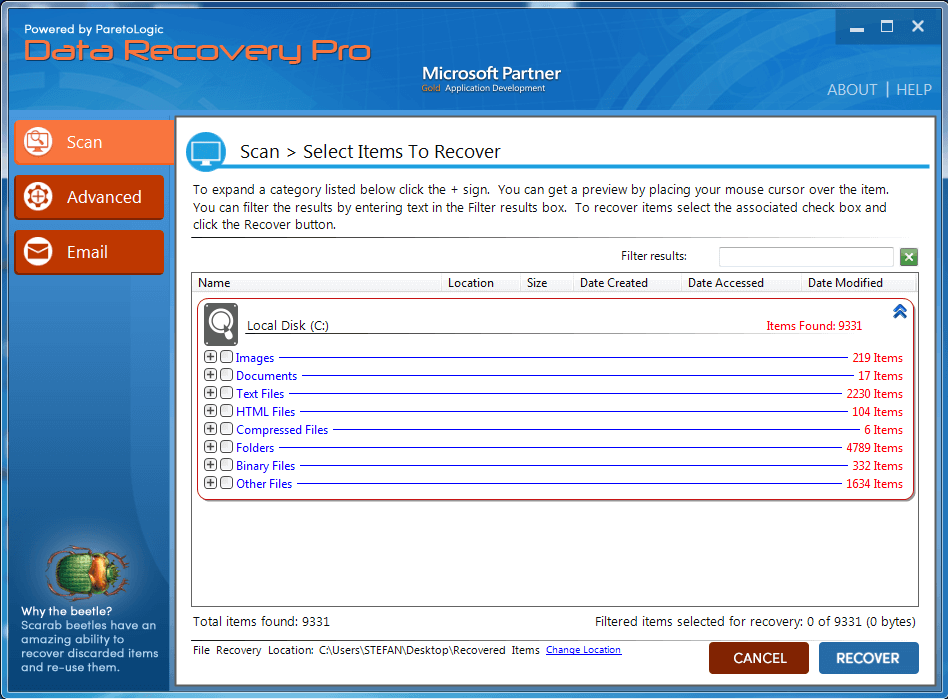
There are several different programs that use shadow volume copies to restore your files. We tested some of them and Data Recovery Pro seems to have the highest chance to help. Unfortunately that comes in the form of cost – you need to purchase the full version to receive its benefits. If you want to try:
Download Data Recover Pro from here. Install the program.
Start the program and choose the hard disk you want to scan for recoverable files. Then click “Start Scan” just like in the picture below.
If you prefer, you can specify a file name in the “Full Scan” section.
After the scan finishes, simply click “Recover” on the bottom right and see if you get your files back.
![]()
Identification
Below you will find a list of free decryption tools that can possibly help you recover your files. However, you need the right tool for the type of encryption used on your files. To learn that, use ID Ransomware – a free online service that will tell you which ransomware is currently messing with your files. You’ll be asked to upload the ransom note file (usually found on your desktop), as well as a sample encrypted file.
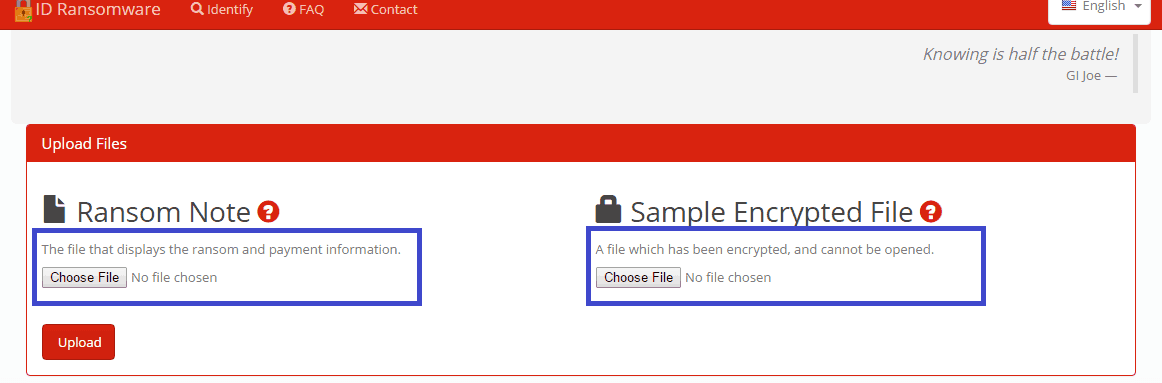
Click on Choose file in each highlighted field and navigate to the files in question
Once it’s done analyzing, ID Ransomware will tell you exactly which ransomware version you are dealing with.
Below you will find a list of all known ransomware file decryptors. Browse through the list and look for a decryptor for your particular type of ransomware. They are listed both by virus name and by extension used on your files.
![]()
Decryption
We do not 100% guarantee any of these will work and they are provided by their creators as is, but most of the time they will get the job done!
- Naturally, before you try any of them it is recommended that you make backups for all files.
- Autolocky – file extension: .locky
- Nemucod – file extension: .crypted
- DMALocker2 – file extension: unchanged
- DMALocker – file extension: unchanged
- Gomasom – file extension: .crypt
- LeChiffre – file extension: .lechiffre
- KeyBTC – file extension: .keybtc@inbox_com
- Radamant – file extension: .rdm or .rrk
- PClock – file extension: unchanged
- CryptoDefense – file extension: unchanged
- Harasom – file extension: .HTML
- Decrypt Protect – file extension: .HTML
- Apocalypse – .encrypted
- ApocalypseVM variant – .ecrypted .locked
- Xorist – .cerber (for the Cerber ransomware including .cerber and .cerber2 look below)
- Globe ransomware – .globe
A company called Emsisoft has created decryptors for all above mentioned ransomware programs. Kudos to those guys.
Emsisoft is a company that specialized in ransomware decryption and they are doing a pretty good job at that. You can download all decryptors for the ransomware from the list above from their website here. Their decryptors are user-friendly and there’s nothing difficult about using them. Most decryptor tools by Emsisoft have similar interface and are used in the same way. Simply run the tool designed for the specific ransomware(no installation required) and in the resulting window choose the folder/disk you’d like to have decrypted. You can add or remove folders with the buttons below. Once you’re ready, simply select the folder in question and click on Decrypt. 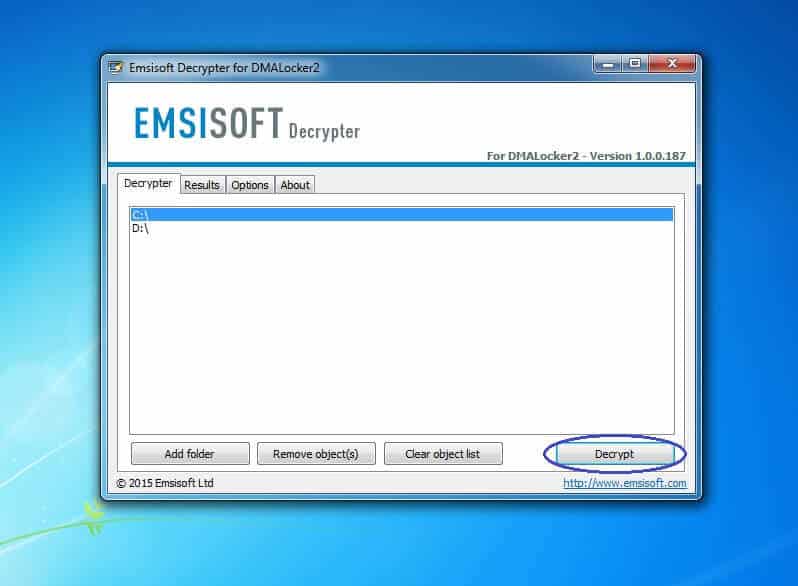
HydraCrypt and UmbreCrypt – file extension: .hydracrypt and .umbrecrypt
This decryptor tool works a bit differently compared to most other decryptors by Emsisoft and this is the reason we separated the instructions on how to use it from the rest. In order to use it, you will need to find an encrypted file on your computer, where you also have its un-encrypted version. Once you have the pair, you’ll need to select both of them and drag-drop them over the tool’s icon. In case you’re unable to get such a pair (pretty likely scenario), find an encrypted PNG file (basically a picture, Windows has sample PNG picture files in the Picture category in My Documents) in your system and then download a random PNG picture from the internet. The files in question need not be the same – only the extension matters! Use the two PNG files as your pair. Doing this will enable the decryptor to bust the code for the encryption. Note that this guide method may apply to future Emsisoft decryptors as well. 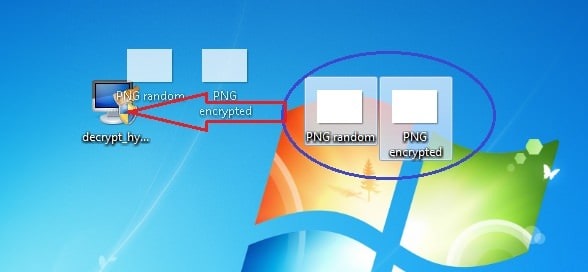
Petya password generator – no extension, whole HDD is locked
First you will need to unplug your infected HDD/SSD and plug it into another machine. Make sure the other computer has an anti-virus installed and running! Petya should be already inert, but we don’t want to take any chances. Now download and start the Petya Sector Extractor by Wosar. It will scan the infected HDD and extract the relevant data, which you’ll copy and use to fill in the fields of this site Here. Once done hit submit and you will get a code. Write it down on paper. Put the HDD back into your PC and start Windows as normal. When Petya prompts for the key use it and you should now have access to your files..
Operation Global III – file extension: .exe
The name of the tool used here is OG3 Patcher. Click here to download. This tool is simple and easy to use. Once you’ve downloaded it, just run it and in the resulting window click on Patch. After the patching has finished a simple double-click on any encrypted files should be enough to bring them back to normal. Keep in mind that using this tool to decrypt executable files might occasionally render them unusable, therefore, you may need to reinstall the program associated with them. This happens due to the fact that the ransomware itself is problematic and there is nothing really that can be done about it. Also, it is strongly advised that you reinstall your whole OS and format all affected drives (or at least do a deep security sweep) once you’ve secured and backed-up any important files. This will ensure that there are no traces of Operation Global III left on your machine.
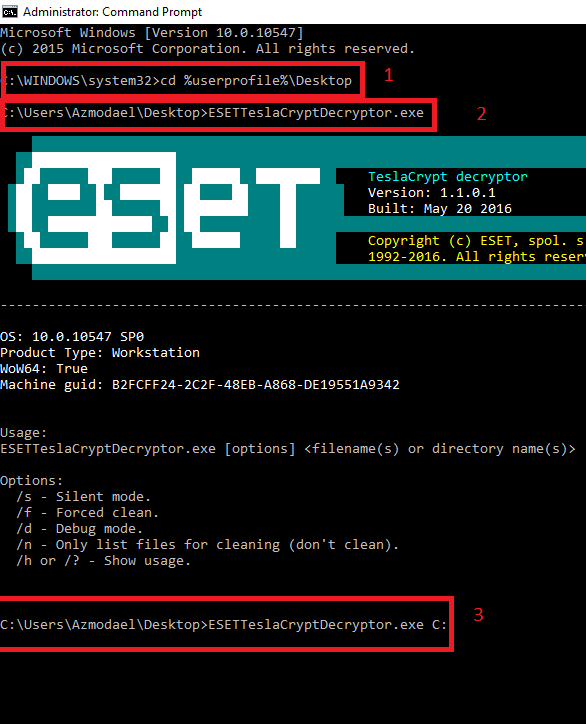
TeslaCrypt – file extensions .ECC, .EXX, and .EZZ
In order to use this tool you’ll need the “key.dat” file that is created by TeslaCrypt. The tool will NOT work without this file, period! The tool will automatically search for “key.dat” in the original location of the file, if it doesn’t find it there it will look in the directory it has been installed it. If it doesn’t find it there it will exit with an error message. Make sure “key.dat” is found in either of these two directories! You will need to input the directory you need decrypted. You’ll need to provide either the path of the name of file to be decrypted. For example if you dump everything in a directory called Decryption that is located in the C drive you need to write the following: C:/Decryption Group the files you need decrypted, enter the directory, hit enter and you are done! The tool supports the following command line options
TeslaCrypt – file extensions .micro, .xxx, .ttt, .mp3 or “unchanged”
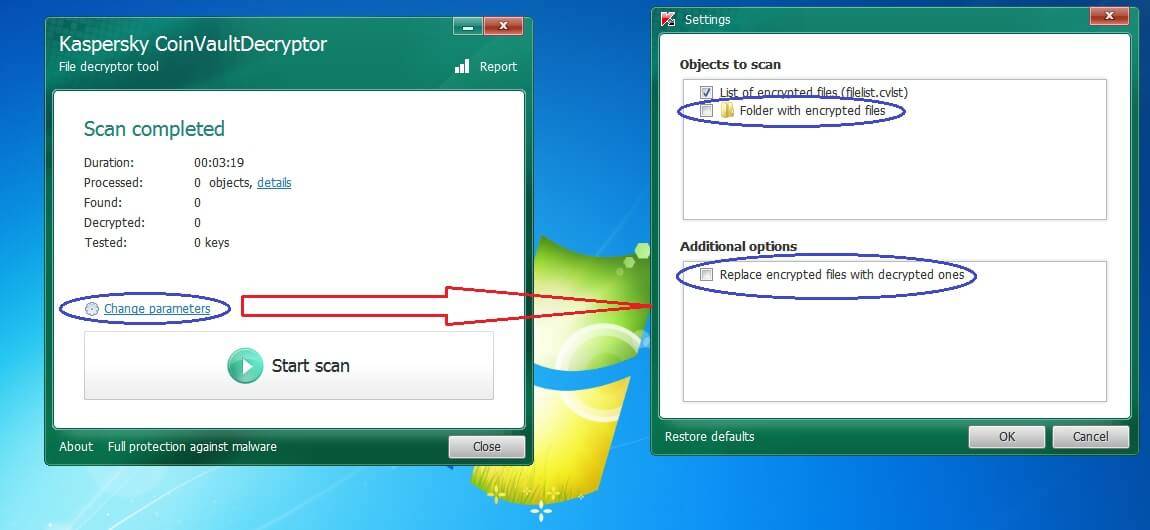
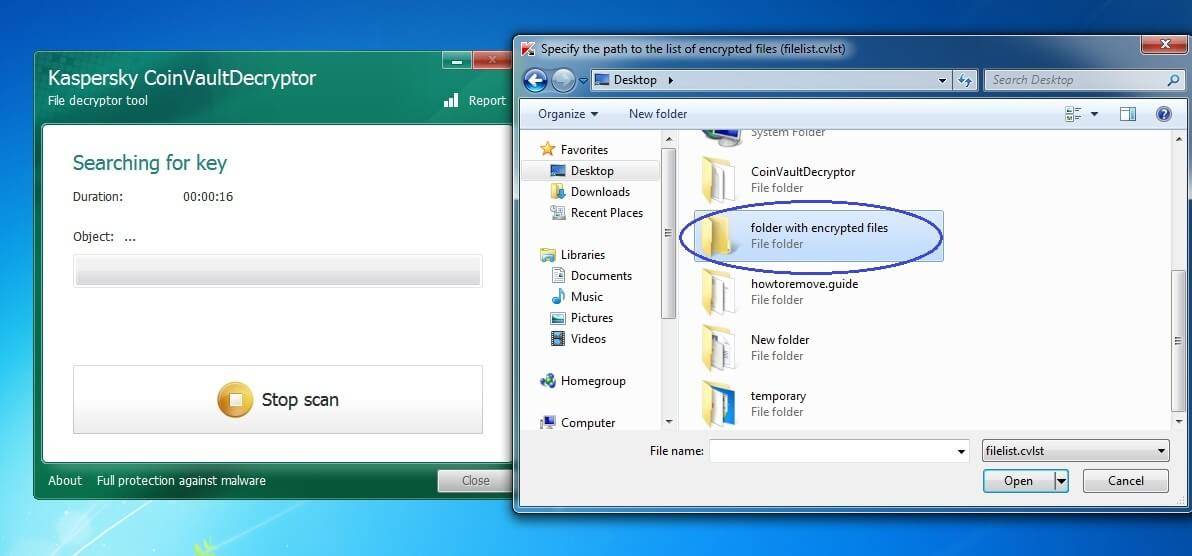
BitCryptor and CoinVault – file extension: 7z.encrypted
Kaspersky has also developed decryptors for the following ransomware viruses:
CrySiS – .crysis and .crysis2 file extensions. Use the Rakhni decryptor for this one.
Rector – file extension: unknown
Rakhni – file extension: .locked
.kraken; .nochance; .oshit; .oplata@qq_com; .relock@qq_com; .crypto; [email protected]; .pizda@qq_com; .dyatel@qq_com; .crypt; .nalog@qq_com; .hifrator@qq_com; .gruzin@qq_com; .troyancoder@qq_com; .encrypted; .cry .AES256; .enc; .coderksu@gmail_com_id371; .coderksu@gmail_com_id372 .coderksu@gmail_com_id374; .coderksu@gmail_com_id375; .coderksu@gmail_com_id376; .coderksu@gmail_com_id392; .coderksu@gmail_com_id357; .coderksu@gmail_com_id356; .coderksu@gmail_com_id358; .coderksu@gmail_com_id359; .coderksu@gmail_com_id360; .coderksu@gmail_com_id20; [email protected]_characters; .hb15;
._date-time_$address@domain$.777; .xxx; .ttt; .micro; .mp3
Scatter – file extensions: .pzdc .crypt .good
Xorist – file extension: unknown
Rannoh – possible file extensions locked-<original_name>.<four_random_letters> ; <original_name>@<mail server>_<random_set_of_characters> ; <original_name>.crypt
Rector (decryptor link) Rakhni (decryptor link) Scatter (decryptor link) Xorist (decryptor link) Rannoh (decryptor link) Please note that decryptors for all of these ransomware are pretty similar to the one used for CoinVault and BitCryptor above, so if you follow the guide for that one, you should do fine with the rest of these tools.
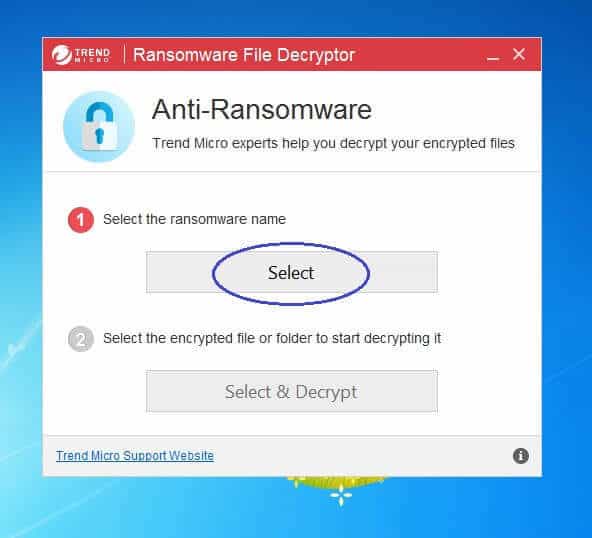
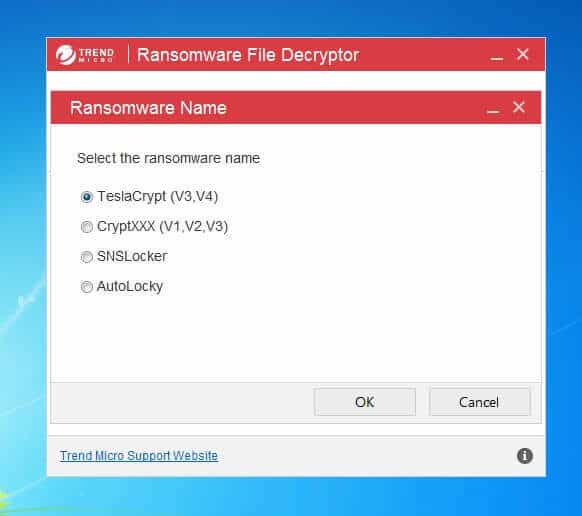
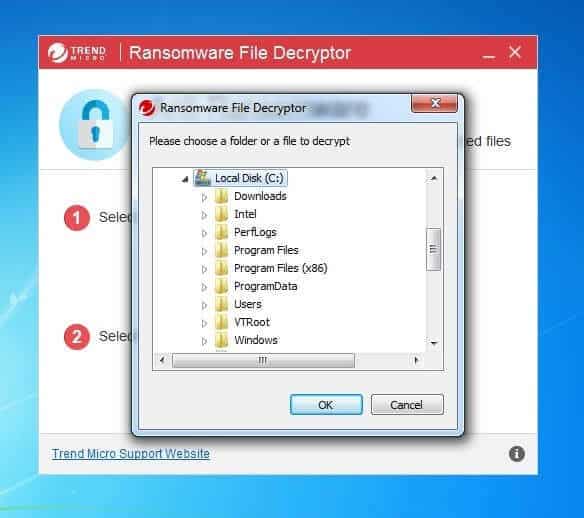
Trend Micro’s Decrypter will allow you to decrypt files affected by:
TeslaCrypt(v3, v4) – extensions .micro, .xxx, .ttt, .mp3 or “unchanged”
AutoLocky – extension: .locky
SNSLockeр – extension: .RSNSlocked
CryptXXX(v1, v2, v3) – extension: .crypt
This is a tool developed by Trend Micro that will help you with the decryption of your files. There are several ransomware encryptions that this tool can deal with. We’ve listed them above. To download the decryptor click here.
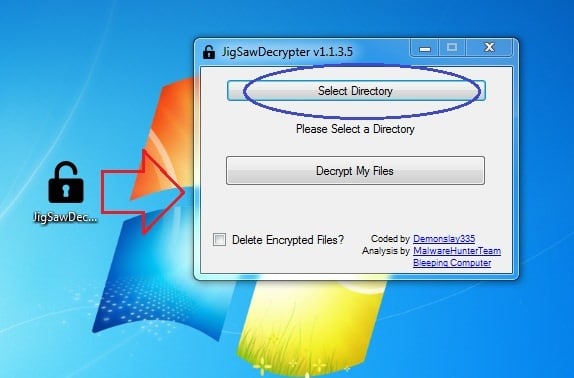
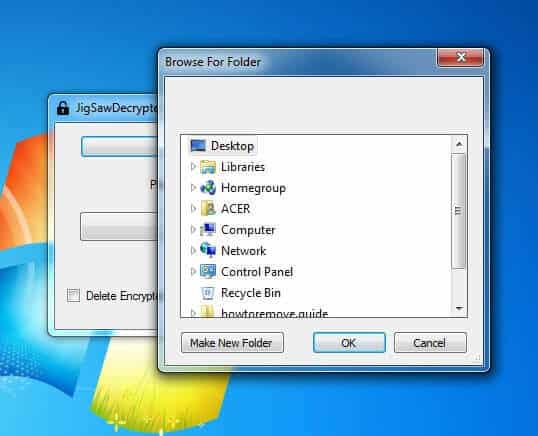
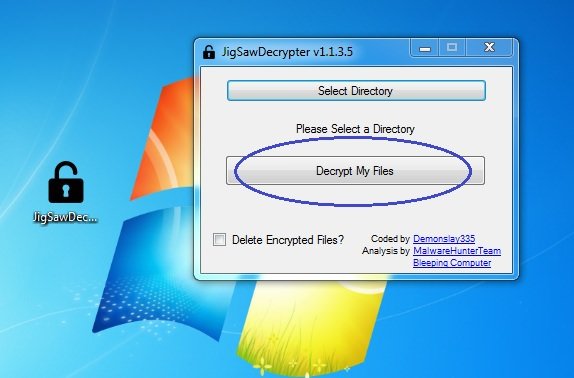
Jigsaw – file extensions: .fun; .kkk; .gws; .btc; .PAYSM
CryptXXX – file extensions: .crypz and .crypt1 ONLY
This one is not actually a decrypter, but rather a bug with the decryptor system itself. It appears that victims of the ransomware with the .crypz and .crypt1 ransomware can follow the instructions as outlined by the ransomware itself and decrypt their files without paying for it! Hurry before the hackers realize their mistake and fix this issue!
The ODCODC ransomware
Download link is here
Breaking Bad themed ransomware with the following file extensions:
.xtbl, .ytbl, .breaking_bad, .heisenberg.
Download link is here. The decryptor is provided by Kaspersky Labs and is fairly simple to use – download, run it and select the appropriate locations to scan. It will do the rest on its own.
Cerber ransomware with the following file extensions:
.cerber and .cerber2
Link is here. WARNING! Site appears to be temporarily down at the moment. We are waiting for the owner to restore functionality while looking for an alternative soltion. Please make a backup of the encrypted files and patiently wait for a resolution. The decryption is a two-step process as described on the site.
DMA Locker 3.0
Decryptor tools for 7ev3n Ransomware
MBRFilter (Ransomware blocker tool for Petya, Satana and Petya+Mischa)
This is a very useful tool that protects your PC from Ransomware viruses such as Petya, Satana and Petya+Mischa. Those viruses, instead of encrypting your files, lock you out of your computer until you pay the ransom. The tool prevents them from modifying your Master Boot Record which in turn makes the virus powerless and harmless. Here is what you need to do in order to get the tool:
![]()
Waiting for a solution
Neither ransomware viruses nor their creators are perfect or infallible and the above list of decryptors is proof of that. Unfortunately, it usually takes time for security researchers to break into the ransomware code and find the solution we so desperately need. Even if there is no decryptor tool available now this doesn’t mean one won’t be created in the future. Feel free to bookmark this page and check here for newly available ransomware solutions. We’ll add them to the list as we spot them on the Net.



my system affected by mogranos how decrypt mogranos file