Re-captha-version-3-35.top
Re-captha-version-3-35.top qualifies as a browser capturer for its capacity to seize control of well-known browsers such as Chrome, Edge, Firefox, and others, tamper with their starting page, and enforce its preferred search engine without seeking approval. As an added irritation, this invasive software compels page redirections to diverse sites, all in pursuit of Pay-Per-Click/Pay-Per-View gains from sponsored advertisements. If your browser has fallen under Re-captha-version-3-35.top’s sway, resulting in disruptions like a substituted homepage, an undesirable search engine, and a deluge of unceasing ads, pop-ups, and banners on your display, this article provides pragmatic remedies for managing the persistent browser capturers efficiently.
The Re-captha-version-3-35.top virus
Uninstalling a browser capturer like the Re-captha-version-3-35.top malware (often inaccurately dubbed) isn’t as straightforward as a conventional program uninstallation. This is because the creators behind this sort of software have designed it to linger on your PC for as long as feasible to guarantee they accrue maximal revenue from the ads it showcases. Sadly, users gain naught from retaining the Re-captha-version-3-35.top malware on their system. Alternatively, they are perpetually exposed to random advertisements and promotional links that encourage them to engage with their content. While this might not necessarily be harmful, grappling with such a substantial volume of promotional material daily may expose you to avoidable risks.
Re-captcha-version-3-35
Re-captcha-version may not possess the malicious capabilities of severe threats like Trojans or ransomware, but its content and displayed advertisements can still pose hazards to your computer’s security. Interacting with the ads and pop-ups from Re-captcha-version-3-35 and Haksaigho without prudence could lead to redirection to various perilous websites and pages. Consequently, to safeguard your computer’s integrity, it’s vital to exercise caution and adhere to the instructions provided on this page to eliminate any potentially undesirable software before encountering significant issues. Adopting these precautions will help shield your system from potential harm and uphold a secure browsing experience.
What is Re-captha-version-3-35.top?
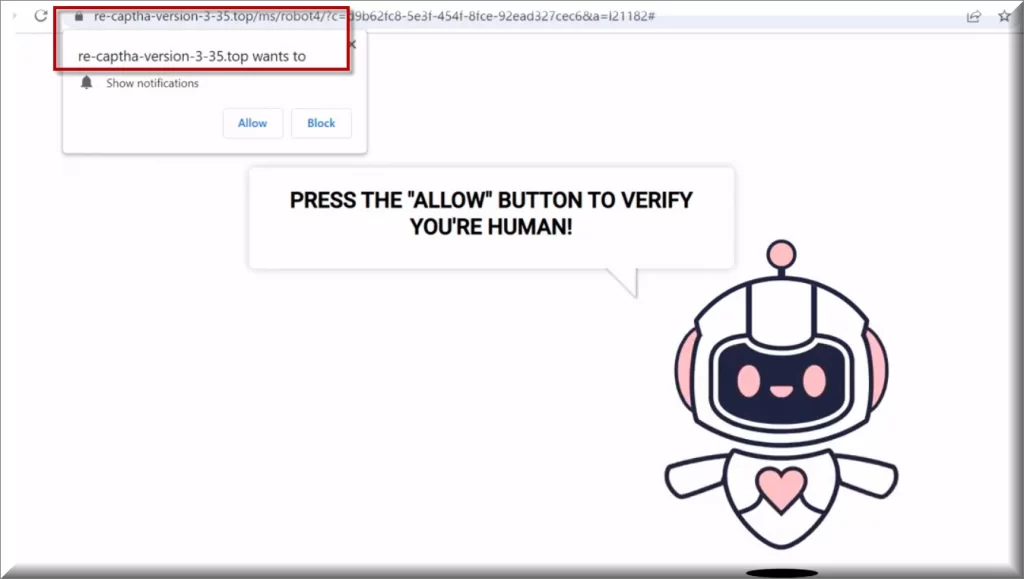
Re-captha-version-3-35.top appears to be linked with captchas, a prevalent security feature on websites used to differentiate between human users and automated bots. Captchas present challenges that demand human comprehension to resolve, ensuring that bots cannot partake in malicious endeavors like spamming or data harvesting. Nonetheless, not all captcha-related websites or services are secure. There might be websites attempting to display counterfeit messages to deceive users into subscribing to their spam notifications. Consequently, for your online protection, we advise exercising caution when engaging with captchas and opting for reputable sources. Eschew websites that tend to inundate your screen with assorted pop-ups and prioritize your online safety to avert potential risks.
Re-captha-version-3-35.top on Chrome
For numerous users, the presence of Re-captha-version-3-35.top on Chrome can be quite deceptive. Browser capturers like this one frequently pledge to enhance your browsing experience by incorporating a personalized search engine, fresh add-on, or a special starting page with various functionalities. Nevertheless, their genuine intent is to expose you to paid ads and sponsored links that enable them to profit from paid online advertising. Re-captha-version-3-35.top on Chrome is a standard software application that operates in this manner, prompting many users to seek aid in eradicating it. Fortunately, in the following sections, we will disclose an effective solution for expelling the intrusive program from your browser.
SUMMARY:
| Name | Re-captha-version-3-35.top |
| Type | Browser Hijacker |
| Deetction Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
How to Remove Re-captha-version-3-35.top
To try and remove Re-captha-version-3-35.top quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Re-captha-version-3-35.top extension (as well as any other unfamiliar ones).
- Remove Re-captha-version-3-35.top by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Re-captha-version-3-35.top and any other suspicious items.
If this does not work as described please follow our more detailed Re-captha-version-3-35.top removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Re-captha-version-3-35.top app and kill its processes
Uninstall the Re-captha-version-3-35.top app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Re-captha-version-3-35.top. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Re-captha-version-3-35.top, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Re-captha-version-3-35.top.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Re-captha-version-3-35.top changes made to different system settings
Undo Re-captha-version-3-35.top changes made to different system settings
It’s possible that Re-captha-version-3-35.top has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Re-captha-version-3-35.top from your browsers
Remove Re-captha-version-3-35.top from your browsers
- Delete Re-captha-version-3-35.top from Chrome
- Delete Re-captha-version-3-35.top from Firefox
- Delete Re-captha-version-3-35.top from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Reply