Realistic Media
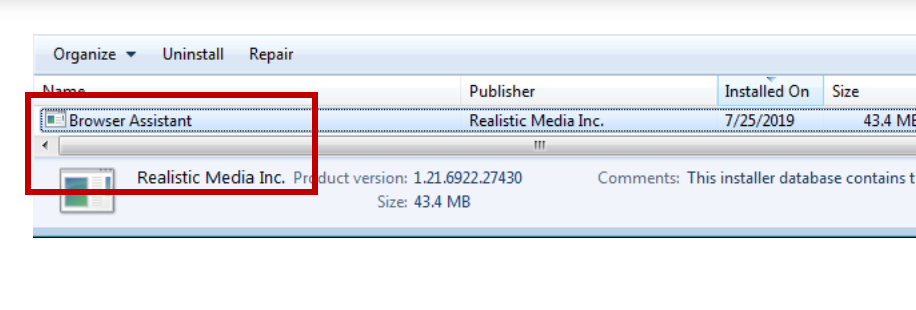
If a Trojan Horse virus has infected your system, you can be in a lot of trouble if the malware is allowed to stay in the machine for long. This article has been dedicated to one of the latest additions to this category of malicious software – a threat known as Realistic Media. Realistic Media Inc. creates Browser Assistant installer and aiming it at Windows systems.
Some of our readers have recently encountered this specific Trojan, and have requested our assistance for its removal. Therefore, below you will find a removal manual with step-by-step instructions on how to detect, and remove the infection once and for all. But before going to the manual, first of all, you should understand that such malware is very stealthy, and notoriously hard to identify. Therefore, we suggest that you read through the paragraphs leading up to the guide, so as to obtain a clearer idea of precisely what a Trojan Horse is, and how you can defend your system from threats like this in the future.
Browser Assistant by Realistic Media
The Browser Assistant Realistic Media virus have a reputation of being very sneaky computer threats. This means that you may not know that you have been infected, while the Browser Assistant Realistic Media virus in your computer is meticulously carrying out various harmful activities in the background of the system. Unfortunately, there is no way to tell you exactly what an infection like Realistic Media may have been programmed for until it completes its criminal task and the consequences of that attack become apparent.
Most Trojans can readily be used to destroy your system, delete particular files, or wipe your computer clean of any data you’ve ever had on it. Theft is another common use – the Trojan-based infections can steal any data from you, without you even knowing about what’s going on. For example, a virus such as Realistic Media can copy, and send files to the servers of the hackers without showing any visible symptoms. The criminals can also use a Trojan for espionage, and there’s more than one way that such a threat could spy on you. For instance, you can be stalked through your webcam, listened to through your mic, and carefully monitored every time you type something on your keyboard. Without your knowledge, your computer could also get filled with other additional malware. In many cases, a Trojan like Realistic Media can operate as a backdoor, and can secretly introduce viruses, and other malicious infections, most commonly (Ransomware, Worms or Spyware) to the compromised computer.
What is Browser Assistant by Realistic Media
Unfortunately, this article is not enough to list everything that a virus of the Trojan Horse category can do, but we believe you already know why it is so important to remove Realistic Media as soon as possible. In case you need professional assistance, we have a special Realistic Media removal tool linked below at your disposal, that will ensure your computer is Trojan-free in a matter of minutes.
Once you remove the infection, however, we’d suggest that you keep your system, and all the programs on it up-to-date. Also, we’d recommend you consider upgrading to a better antivirus software. And above all, while browsing the web, try to avoid the potential sources of malware, such as adult websites, fake/shady or suspicious system update requests, random pop-ups, and other notifications, such as those claiming that you’ve won a prize. Furthermore, spam messages sent via email should not be trusted, especially if they prompt you to click on links, or attachments of unknown origin. Do not open such messages, and definitely never interact with their content if you are unsure about where they are coming from.
SUMMARY:
Remove Realistic Media Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Reply