RegretLocker
RegretLocker is a ransomware-based infection which requests you to pay a fee to free your files from encryption. When infected with RegretLocker, you will get your files encoded with a complex encryption code and will be greeted by a ransom message on your computer.
The good news is that there are some methods that may be able to help you cope with this ransomware cryptovirus without paying ransom to the hackers behind it and, on this page, we will speak about them. If you stay with us, you will find out how to remove RegretLocker from your computer and how to protect your files in the future. We will also provide you with some free file-recovery instructions, a step-by-step guide and a professional program to handle the virus in the best possible way.
The RegretLocker Ransomware
The RegretLocker ransomware is a malicious piece of software with file-encrypting abilities. The RegretLocker ransomware targets user data and encrypts it so that the hackers behind the infection can demand a ransom payment for its decryption.
Infections with ransomware viruses typically occur when web users click on malicious web content. Such content is frequently distributed through spam emails, different attachments, misleading adverts and links, torrents and low-quality downloads. That’s why it is best if you stick to reputed online sources and avoid interaction with sketchy web materials as much as possible. Another good tip about prevention is to always create backups of your most valuable data and store it on an external storage or another device. In this way, you can always access your files from the backups and even if ransomware like RegretLocker attacks you, once you remove it, you can copy the encrypted data back.
The RegretLocker file encryption
The RegretLocker file encryption is a complex code that is applied to the files stored on the ransomware-infected computer. The RegretLocker file encryption can be reversed only by the users who purchase a decryption key from the hackers behind the infection.

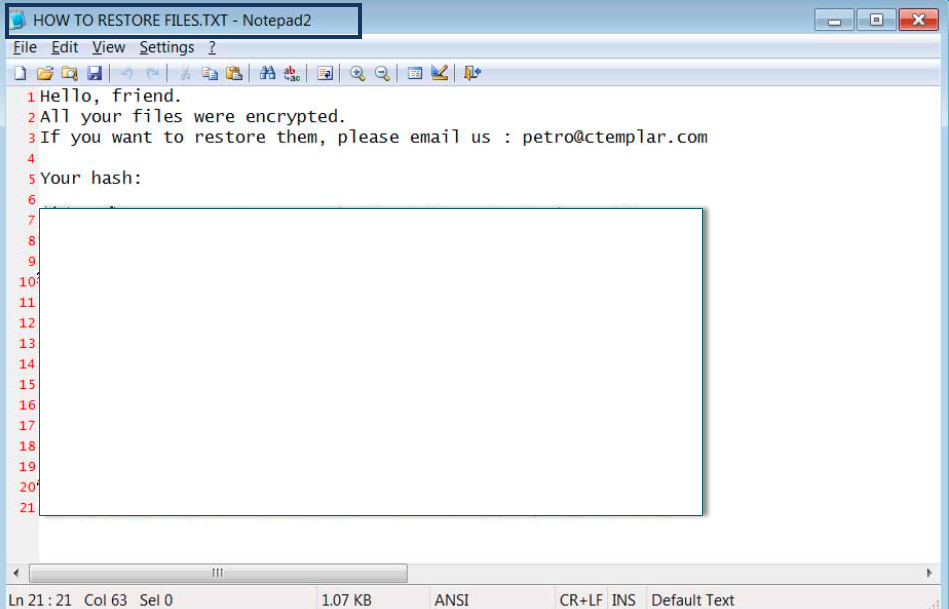
The victims of the ransomware are typically given concrete instructions (in the form of a text message) on how to send the money for that key. Quite often, however, if the payment is postponed or not made the hackers threaten to permanently destroy the decryption key and leave the encrypted data inaccessible forever. They also typically threaten to double the demanded ransom amount after a few hours so that the victims pay as quickly as possible. Nonetheless, you must be aware that the cyber criminals only use these forms of intimidation to frighten the victims and not give them time to seek alternatives.
Leading security experts, however, share the opinion that sending money to Ransomware crooks is not a smart idea. There is a significant risk for the victims to just burn their money and get a key that doesn’t work and is totally ineffective or never get a decryption key at all. Therefore, our suggestion is to remove RegretLocker and try to retrieve information from personal backups when they are available or try to extract files from the system just as it is shown in the file-recovery section of the removal guide below.
SUMMARY:
| Name | RegretLocker |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | No Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
RegretLocker Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt RegretLocker files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply