
*Source of claim SH can remove it.
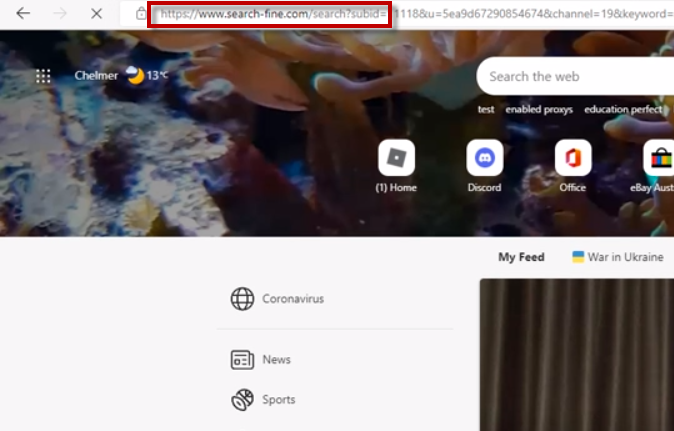
Search-fine is a potentially unwanted program that can alter the configuration settings of popular web browsers such as Chrome, Edge, and Firefox. The program can modify the settings of the affected browser to display unwanted advertisements about various websites, products, and services. This intrusive behavior makes it a browser hijacker, a term used to describe programs that take over browsers and cause unwanted modifications to their settings. These changes can negatively impact the user’s browsing experience and expose them to potentially harmful online content. To prevent any further unwanted behavior, use our Search-fine removal guide and get rid of Search-fine from the system.
What is Search-fine?
Search-fine is a type of software known as a “browser hijacker” or “potentially unwanted program” (PUP). Although it may seem like malware to many users upon their initial encounter, Search-fine is fundamentally distinct from actual malware in terms of its purpose and effects. It forces redirection and displays aggressive pop-up advertisements, banners, and other types of advertising to redirect users to a specific sponsored product or service.
Applications like Search-fine, Grakorte typically make money via Pay-Per-Click or Pay-Per-View payment models, converting each click into a small amount of revenue. Therefore, the more advertisements and links users click on, the higher the profit. It is important to note that browser hijackers are not intended to harm the computers on which they are installed, but rather to promote certain products through changes to system and browser settings. Such modifications include altering the homepage, search engine, and introducing new entries in the System Registry and Startup Items. These changes are frequently made without the user’s knowledge or consent, and are therefore considered to be potentially undesirable.
What are the possible drawbacks of not removing Search-fine?
While Search-fine may not appear to be an immediate threat to your computer system or virtual security, its intrusive advertising methods and modifications to your browser may lead to a range of issues that should not be underestimated. For instance, being bombarded with pop-up ads that cannot be closed can be extremely frustrating, especially when you’re forced to use a browser that has undergone significant modifications.
However, the true danger lies in the fact that you cannot always trust the advertising content displayed by Search-fine. Clicking on the pop-ups and sponsored links may redirect you to rogue websites that can contain phishing attempts or malware disguised as free applications, such as Ransomware, Trojans or other viruses. Moreover, while the changes to your operating system and browser may not be malicious by themselves, they cannot be uninstalled while the program is still present on your computer, leaving you vulnerable to more stealthy threats like a Trojan or cryptovirus. Considering these risks, we strongly recommend that you take steps to remove Search-fine and all associated files and settings from your computer as soon as possible.
SUMMARY:
| Name | Search-fine |
| Type | Browser Hijacker |
| Detection Tool |
We tested that SpyHunter successfully removes Search-fine* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and Search-fine may reinstall itself at the end if you don’t delete its core files. |
*Source of claim SH can remove it.
How to remove Search Fine
To effectively get rid of Search-fine from your system, you can follow these steps:
- Open your browser and access the settings menu. Depending on your browser, this can be done by clicking on the three-dot icon, the hamburger menu, or the gear icon.
- From there, select the option that says “More Tools” or “Add-ons”.
- In the new window that opens, click on the “Extensions” tab.
- Look for any extensions related to Search-fine, as well as any other unfamiliar ones.
- Once you have found Search-fine, click on the trash bin icon located next to its name.
- Confirm that you want to remove the extension and any other suspicious items you have found. If for any reason these steps are not successful in removing Search-fine from your system, please refer to our more detailed removal guide below for further instructions.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Certain steps in the removal process may necessitate leaving the current webpage. We recommend bookmarking it for later reference. To proceed, reboot your device in Safe Mode . If you are unsure how to do this, please refer to our step-by-step guide.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press the key combination CTRL + SHIFT + ESC simultaneously and go to the Processes tab (the “Details” tab on Windows 8 and 10). Identify any processes that appear to be malicious.

Right-click on each of the processes and select “Open File Location.” Scan the files in the folder with the free online virus scanner below, which uses up to 64 antivirus programs to ensure maximum accuracy.

Once you have identified infected processes, end them and delete their folders. It’s important to note that if you’re certain a file is part of the infection, delete it even if the scanner doesn’t flag it as malicious.

To remove suspicious entries and protect your computer from potential threats, follow the steps below:
- Press and hold the Start Key and R simultaneously to open the Run dialog box.
- Type appwiz.cpl in the field and press OK to access the Control Panel.
- Look for any suspicious entries and uninstall them immediately.

In the search field, type msconfig and press Enter. This will open a new window.
Next, navigate to the Startup tab and uncheck any entries that appear to be from an “Unknown” manufacturer or otherwise look suspicious. By following these steps, you can remove any potential threats to your computer and improve your system’s security.


*Source of claim SH can remove it.
To check if your computer has been hacked, follow these steps:
Press the Start Key and R key together, copy and paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. Check if there are any suspicious IPs connected to you at the bottom, below “Localhost.” If you find any, please contact us in the comments.

Open the start menu and search for Network Connections. If you’re using Windows 10, you can simply type it after clicking the Windows button and press enter.
Right-click on the Network Adapter you are using, select Properties, and then click on Internet Protocol Version 4 (ICP/IP) Properties.
The DNS line should be set to Obtain DNS server automatically. If it’s not, set it yourself.
Click on Advanced and go to the DNS tab. Remove anything that’s there (if there is something) and click OK.


It is important to follow the fifth step carefully to ensure that the threat does not reappear upon system reboot.
• Right-click on the browser’s shortcut and select Properties. Please note that while we are showing Google Chrome as an example, you can use the same procedure for Firefox, Internet Explorer or Edge.

In the Properties menu, select the Shortcut tab. In the Target field, remove all text after .exe.

![]() Remove Search-fine from Internet Explorer:
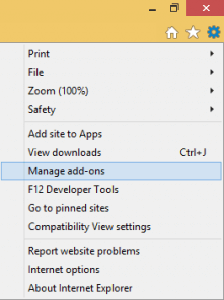
Remove Search-fine from Internet Explorer:
To remove Search-fine from Internet Explorer, launch the browser and click on the Manage Add-ons option. Find the threat and click Disable. Then, go to Internet Options and change the URL to the desired one if it has been hijacked. Click Apply to save the changes.
![]() Remove Search-fine from Firefox:
Remove Search-fine from Firefox:
To remove Search-fine from Firefox, open the browser, click on the main menu, then on Add-ons, and then select Extensions. Look for Search-fine and click on Remove.

![]() Remove Search-fine from Chrome:
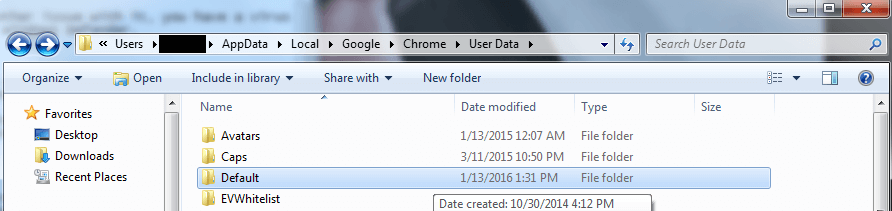
Remove Search-fine from Chrome:
To remove Search-fine from Chrome, first close the browser, and then navigate to
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data.
Once there, find the Default folder and rename it to Backup Default. Finally, restart Chrome to complete the process.

To start with, press the Windows key and type “Regedit” in the search field. Once you hit Enter, the Registry Editor will open. Then, use the “Find” function (press “Ctrl” + “F” keys) and enter the name of the threat. If any entries with similar names appear, right-click on them and delete them. If you cannot locate any entries using the “Find” function, you will need to manually delete/uninstall them from the following directories:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – if you’re not sure which ones are malicious, feel free to ask us.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If you are still having trouble removing the threat, you may want to download the anti-virus program that we have recommended or use our free online virus scanner. Alternatively, you can always ask for our assistance by leaving a comment below.

Leave a Reply